Last weekend saw the announcement of ProxyHam, a device that anonymizes Internet activity by jumping on WiFi from public libraries and cafes over a 900MHz radio link. The project mysteriously disappeared and was stricken from the DEFCON schedule. No one knows why, but we spent some time speculating on that and on what hardware was actually used in the undisclosed build.
[Samy Kamkar] has just improved on the ProxyHam concept with ProxyGambit, a device that decouples your location from your IP address. But [Samy]’s build isn’t limited to ProxyHam’s claimed two-mile range. ProxyGambit can work anywhere on the planet over a 2G connection, or up to 10km (6 miles) away through a line-of-sight point to point wireless link.
The more GSM version of ProxyGambit uses two Adafruit FONA GSM breakout boards, two Arduinos, and two Raspberry Pis. The FONA board produces an outbound TCP connection over 2G. The Arduino serves as a serial connection over a reverse TCP tunnel and connects directly to the UART of a Raspberry Pi. The Pi is simply a network bridge at either end of the connection. By reverse tunneling a TCP connection through the ‘throwaway’ part of the build, [Samy] can get an Internet connection anywhere that has 2G service.
Although it’s just a proof of concept and should not be used by anyone who actually needs anonymity, the ProxyGambit does have a few advantages over the ProxyHam. It’s usable just about everywhere on the planet, and not just within two miles of the public WiFi access point. The source for ProxyGambit is also available, something that will never be said of the ProxyHam.















At that point, why not just use vpn and/or tor? GSM seems orders of magnitude more trackable than ham.
I’ve heard it said that you can use some sort of directional antenna to only get reception from one cell tower, which at least broadens where you can be to a likely radius instead of being easily triangulated.
But I don’t see that mentioned in the writeup, so I don’t see how this is more secure than me tethering with my cell phone.
VPNs are honeypots- checkout snowden docs on that topic – apparently 5-eyes have ‘pwned’ like 80% of VPN providers.
Meanwhile TOR was invented by the navy. There are now growing instances where tor has also proven to be a honeypot.
The EFF beg to differ
https://www.eff.org/deeplinks/2014/07/7-things-you-should-know-about-tor
Surely these growing instances have been verified. Individual nodes may be operated by the Government but that doesn’t make the whole service a honeypot. AFAIK all the published attacks on tor have been addressed by the tor project.
Lastly if you’re using tor as your only ‘security’ or ‘anonymity’ you’re doing it wrong.
Yeah… There is no single panacea, also, because i dont do anything or have anything secret, I dont actually practice these tasks – I just like to read about computer security.
The tor attacks seem pretty clear, no matter what tor crew says – be it bad web development leaking IPs, or government running slews of exit nodes – it isnt anonymous.
That’s… kind of the opposite of what EFF said in that article. Yes, they can sometimes get around Tor, but largely it relies on them finding exploits in the Tor bundle, people mis-configuring it (which is why you use a Tor bundle) or people being monitored before their connection enters the Tor network (in which case you’re screwed anyway). If they want to monitor you and you’re using Tor, they’re really going to have to work for it, and even then there’s a decent chance they won’t be able to track it back
Oh, and the government running the exit nodes isn’t a huge issue. It’s only an issue when they’re also running the entry node you connect to, so can link the activity going out to the activity going in. If only one end is being tracked it becomes significantly harder to track you
is the arduino really needed, or could it be done without? rpi has plenty of gpio…
rPi GPIO struggles to be realtime.
Oh how i would like to say some things.
Big brother is watching. but i must admit some times he’s not to smart and locks up the wrong people.
I’ve done a lot of cool things. that I know he /she would not like.
One thing i can say. I have a direct wireless connection to my inlaws house to help watch over them.
they are 3.5 km away. there are 5 cameras, 4 voice channels and i can turn on most of the lights in the house. and now have a internet connection there as well.
When i started this there I didn’t know about the arduinos back then. I all so can call from there house from my house as well, more so if i have to call 911. and have a connection to my network at my place when i’m there. They still dont have a internet there.
In all works out good. Going on 7 years now. I have upgraded 3 times over the years. But I think this will be the last tiime.
But remember big brother is watching. ( more so recording… and your data will goto the highest bidder. ) so what ever you say or do on the internet will be used against you in the future. There is no privacy now.
thanks
So, how’d you do that, then? I’m interested.
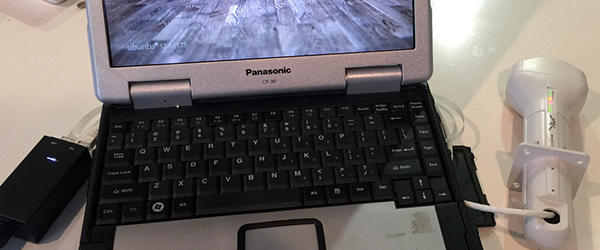
I’ve seen Perry’s setup, it really should be written up here. The actual sight of it is beyond words but here ya go…
He started with a whole lot of old acoustic modems. He attached tin cans to the speakers and mikes. He attached really long strings to the cans. Each one is pretty low bandwidth but he makes up for that in quantity. These masses of strings vibrating across the neighborhood.. well.. it’s something you just have to see!
How is this better than a pay-as-you-go plan tethered to your laptop? I mean, isn’t that essentially what [Samy] has recreated? Root an older smartphone, buy a sim card, done. No fiddling w/ power supplies or breadboards.
This provides no additional privacy. Government monitoring, measures packet timings and sizes (metadata) and can cross correlates this on a global scale. You can use a VPN, encryption, compression, there will still be a strong correlation. If you are tagged, you will be tracked. Buffering packets with random delay times would be more useful. Using IP on GSM and IP on something else will not reduce the correlation.
Thanks Ed Snow.
I’m not Ed, but thanks for the complement.
is he a bastard from the north?
Orrrrr…. get a cheap used android smartphone or something and write some proxy software for it.