There’s some debate on which program gets the infamous title of “First Computer Virus”. There were a few for MS-DOS machines in the 80s and even one that spread through ARPANET in the 70s. Even John von Neumann theorized that programs might one day self-replicate. To compile all of these early examples of malware, and possibly settle this question once and for all, [Mikko Hypponen] has started collecting many of the early malware programs into a Museum of Malware.
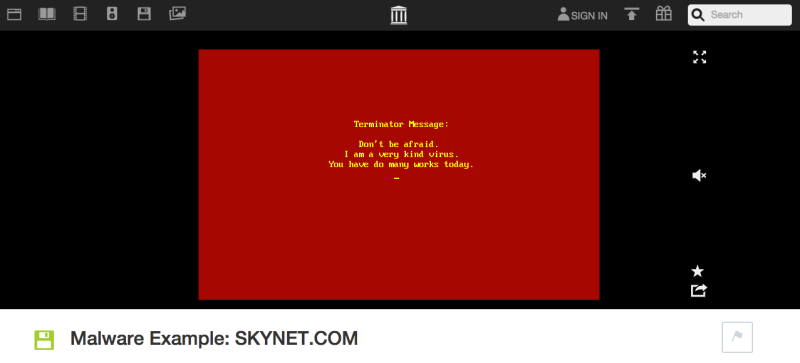
While unlucky (or careless) users today are confronted with entire hard drive encryption viruses (or worse), a lot of the early viruses were relatively harmless. Examples include Brain which spread via floppy disk, the experimental ARPANET virus, or Elk Cloner which, despite many geniuses falsely claiming that Apples are immune to viruses, infected Mac computers of the 80s. [Mikko] has collected many more from this era that can be downloaded or demonstrated in a browser.
Retrocomputing is an active community, with users keeping gear of this era up and running despite it being 30+ years old. This software, while malicious at the time, is a great look into what the personal computing world was like in its infancy. And don’t forget, if you have a beige computer from a bygone era, you can always load up our Retro Page.
Thanks to [chad] for the tip!















https://xkcd.com/350/
I’d be interested to see Windows 95 malwares in action, right when people were starting to get online in a big way. Somewhere where a malware’s transmission vectors and signatures could be documented and observed in real time.
Better than an aquarium.
https://xkcd.com/350/
Someone actually build that, with live streams of all the screens. Anyone could upload exe files to the VM’s which where automatically run. I think it included a Windows 95 machine but unfortunately I can’t find the site anymore :-(
I found HaD’s writeup, but the actual site won’t load…
http://hackaday.com/2014/06/28/xkcds-virus-aquarium-made-real/
There was one pretty nasty virus for Win95, called CIH or Chernobyl. It would activate only once a year, on 26.04. (date of Chernobyl nuclear accident) and delete contents of motherboard BIOS. So computer would be bricked, only way to recover it was to remove BIOS from DIP socket and reprogram it with EEPROM programmer.
Or don’t use your computer on that day?
There was also an equivalent on Macs called SevenDust, which had multiple varieties of varying complexity. It was also the first polymorphic virus on Mac. http://virus.wikidot.com/sevendust
There are some youtube channels dedicated to this (danooct1, rogueamp).
This page has a pretty nice summary of the payloads!
Depending on your definition of ‘virus’ or malware’ – there were origins even before personal computers like the XT / Apple etc.
Programmers challenged each other to create programs to kill all competing programs until only one remained – the winner. Some replicated into various memory blocks. Some were just asterisk guns that wrote the ascii for the asterisk into random memory location. Some would mutate and hide.
ISTR there was a sort of virtual machine environment for that competition.
It was called ‘REDCODE’
See core wars. The game was introduced to the public in May 1984, in an article written by A. K. Dewdney in Scientific American.
Heh, yes back in the innocent days we had all sorts of fun like that.
In the 80’s when I was about 15 I wrote a little piece of 6502 assembly language for the BBC micro that took advantage of the total lack of security on the BBC Econet network. So much fun in our school’s nascent computer science lessons remotely pushing commands into another user’s keyboard buffer. I’d sit at the back of the class, distract a friend and then push something silly into his keyboard buffer and try to suppress laughter when he turned around and found there was a ‘ghost in the machine’. Another similar one sniffed the admin password as it passed unencrypted through every machine on the network.
More fun in the early 90s at University. The computer room was a mix of Commodore Amigas, text terminals and graphical X-Terms (can’t remember the make). All were being used as terminals on to the department’s Sun servers. I preferred to work at the graphical X-Terms but the problem was that an inconsiderate group of ‘lads’ liked to play x-pilot on them. All day. So I studied the source to x-pilot and noticed that one of the remote commands that it accepted was a timed shutdown that, when received, would display a per-second countdown on the screen and then shutdown immediately. All unauthenticated of course. A little command line program was duly created that sent that shutdown command to a workstation of my choice with a timer of my choice. Let’s see, can they click the ‘abort shutdown’ button in 3 seconds? How about 2? Nobody got it in one second. Score one for the geeks.
So much innocent fun back then. It’s all way too serious now that morons have computers.
Reminds me of a trick we pulled on a new co-worker. We installed a customized command.com on his machine that would only execute the chdir and dir commands. Much hilarity ensued.
There was a big missed opportunity to use pre-OS X Mac OS as a vector for spreading PC viruses. How? By hacking the software which enabled a Mac to read and write to microsoft formatted writeable media.
A Macintosh that can read and write PC media (including OS X) automatically creates various folders and files on it without asking the user for permission to do so. It should have been possible to hack that to read boot sectors off floppies then write them to the next disk that gets inserted. Or as part of the hack, inject an infected boot sector into the Mac software then write that to PC media.
Yet another option would be to have it check for a bootable disk then copy a virus installer to the disk and alter the autoexec.bat (or create one if there wasn’t one) to run it and infect a PC booted off it.
Far as I know, that vulnerability of places running Mac and PC systems was never exploited. It would have been such a creative malicious hack that likely would have taken a good while to discover.
I can’t help but think that our computers would be much more secure than they are now if we let the viruses run instead of deleting them and simply improved memory protection and file permissions instead. operating systems wouldn’t be as easily exploitable for botnet, cryptolocker and stuxnet use. Any malware that managed to root the box would be instantly crippled by a plethora of viruses competing for the same registry keys.
The Elk Cloner was an Apple II virus, yes? So… not a Mac.
Macs definitely had viruses. http://lowendmac.com/2015/classic-mac-os-viruses/
nVir still pops up in old Mac shareware game archives all these years later.
I wonder if I still have that L0pht Heavy Industries CD-ROM with old viruses on it…
Ah, yes, ancient malware. In the ’80s I got interested in self-replicating code after reading about the possibility in a book by Douglas Hofstadter. The IBM PC had come out a couple of years before. I had one and an assembler for it, so I wrote a self-replicator for amusement and to see if I could. A while ago while looking for something else I came across a printed assembly listing and made a pdf of it. You can see it here: https://drive.google.com/file/d/0B6sp4xMLNOZITnpLRnB0eGkyTzA/view
Real x86 programmers use DEBUG!