Since the Beginning of Time* humans have been irresistibly attracted to the blinking of an LED. At first there was one LED and it was good, but eventually there were many working in unison and the matrix was formed. Badge hacking at the Hackaday SuperConference challenged everyone to do something interesting with the display matrix and other yummy hardware on this year’s badge and we were in awe of what people managed to pull off.
We named three winners, and recognized the first hacker to solve the Crypto Challenge. Check out the presentations in the video below and then join us after the break for a close look at each winning hack. Three winners received $256 and the crypto challenge winner received $512; two of them told Hackaday they plan to donate their prize to charity.
*we of course mark the beginning of time as the Unix Epoch
Best Dead Bug
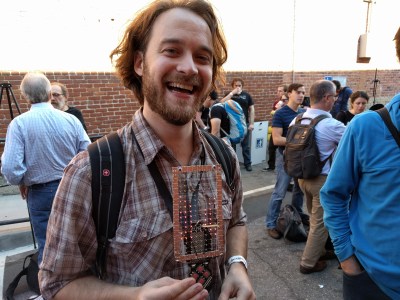 Dead-bug refers to the method of placing a DIP part on its back and soldering your circuit to the upward-pointed leads. [Zach Fredin] went all out with his entry for badge hacking, dead-bugging all of the LEDs on the display.
Dead-bug refers to the method of placing a DIP part on its back and soldering your circuit to the upward-pointed leads. [Zach Fredin] went all out with his entry for badge hacking, dead-bugging all of the LEDs on the display.
He depopulated 128 surface mount LEDs. He then built a frame using his awesome Xacto knife and copper clad prototyping technique. This frame holds a grid of wires in open air to which the LEDs are soldered to reform the same 8×16 matrix but much larger (here’s a super-closeup image). The result is spectacular and shown off well at 2:27 in the presentation video.
An honorable mention simply must go out to [Jessie Tank], who you may know better as [ThunderSqueak]. She wanted to generate audio with her badge, but didn’t want to limit her project to using headphones. The solution was to build her own speaker out of paper plates and enameled wire. It works amazingly well as she shows at about 5:55 into the video.
Best Blinky
Creative use of a relatively low-resolution display is a real challenge, and the reason that [Ivgeni Segal’s] hack is so interesting. He and his teammates, [Zhou Tan] and [Tizoc Franco], built a maze which shows off a real depth of architectural interest (you will not be bored exploring the different parts of the maze). The maze contains a “ball” the user needs to navigate to the exit. Check it out at about 21:42.
There are four buttons on the badge for directional input, but [Iv] made the maze much more interesting by skipping the D-pad and going for the accelerometer. Tilt the badge in any direction and gravity will move the ball around its digital obstacles. Check out the source code for the maze hack.
Also worth mentioning is [Mark VandeWettering] who pulled off a set of very cool visualizations on his badge at just about 12:00 into the presentations. He included one we weren’t familiar with: Munching Squares was originally implemented on the PDP-1 way back in 1962!
Most Over-the-Top
 [Sprite_TM] never fails to amaze. He gave an intensly-entertaining talk (look for that video next week) on Saturday, solved the crypto challenge by disassembling the binary, and still had time for this hack.
[Sprite_TM] never fails to amaze. He gave an intensly-entertaining talk (look for that video next week) on Saturday, solved the crypto challenge by disassembling the binary, and still had time for this hack.
The stock firmware on the badges uses 1-bit color (pixels are either on, or off). [Sprite] didn’t just implement greyscale but made a synchronized network of badges. He’s still using the bootloader but doesn’t send the interrupt vectors back to the kernel. This lets him use his own interrupts to generate the different levels of brightness.
The networking aspect starts with him flashing firmware to three slave badges. His master badge sends synchronization information using IR and turning the slave badges into a single displays. This way, his Rick Roll has 24×16 pixels to work with rather than the 8×16 of a single badge. Impressive. See it in action at 28:52 and check out his source code for the hack.
Crypto Challenge
![[Jonathan Dahan] explaining how he solved the Crypto Challenge](https://hackaday.com/wp-content/uploads/2016/11/jonathan-dahan-crypto-challenge-winner.png?w=400)
[Jonathan] solved Mastermind by brute forcing the first entry, using 1234 as the value until he received a large number of correct information, making the subsequent guesses much easier. He used an app on his phone to interpret the Morse code but was entering one of the answers incorrectly. This led him to disassemble the hex file to get at all the strings which were the answers. The third challenge uses four columns of bits which need to align to make some type of image. He made his own help, copying them onto paper slips and playing around with it. But in the end a good night’s sleep was what did it. He skipped the fourth challenge, realizing that he had almost everything he needed to complete the final set. He simply brute-forced the last few letters to unlock the win screen.
Well done and congratulations. We love to see that so much collaboration went into this enjoyable activity!
Badge Hacking Has a Purpose
It’s easy to look at these winners and feel amazed by the skill and creativity that went into each. There was a great vibe from everyone taking part in badge hacking — this was one of the best shows of community from the SuperCon. The badge hacking area was buzzing with conversation. Everyone was goofing around, looking over each other’s shoulders to ask what they were working on, and asking for help which was happily greeted by everyone around.
You don’t need to pull off an epic hack to be successful. There were people at the con who have just blinked their first LED, and others who have been elbow deep in designing silicon, yet everyone treated each other as equals because everyone is a beginner and some point and all want to see beginners acquire leet hardware skills.
We want to thank [Ari] who got up on stage at 39:56 to present his badge hack: he compiled the sample C framework and flashed it to the badge — his first time working with embedded hardware. He is proud of this first step, and he should be! We can’t wait to see him at next year’s SuperCon, wearing this year’s badge and showing off all that he managed to learn from this humble beginning.
















Please be kind and respectful to help make the comments section excellent. (Comment Policy)