If only Marv and Harry were burglars today; they might have found it much easier to case houses and — perhaps — would know which houses were occupied by technically inclined kids by capitalizing on the potential vulnerability that [Luc Volders] has noticed on ThingSpeak.
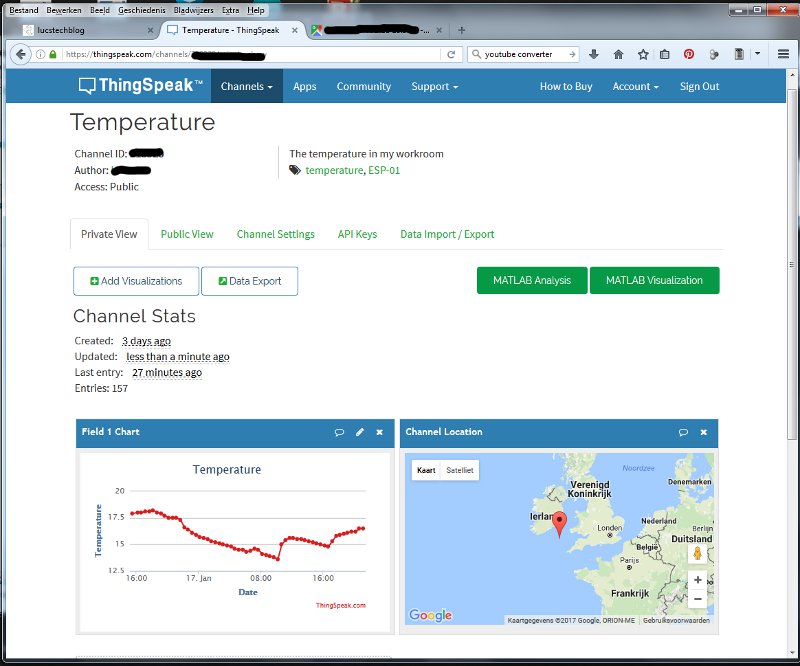
As an IoT service, ThingSpeak takes data from an ESP-8266, graphs it, and publicly displays the data. Some of you may already see where this is going. While [Volders] was using the service for testing, he realized anyone could check the temperature of his man-cave — thereby inferring when the house was vacant since the location data also happened to be public. A little sleuthing uncovered several other channels with temperature data or otherwise tied to a location that those with nefarious intent could abuse.
Not a vulnerability with the software per se, but [Volders] well observes that privacy settings must needs be altered whenever you’re using an online IoT service. Despite the awesomeness of IoT inter-connectivity, always be aware of the downsides and take steps to mitigate them.















Is there a ThingSpeak service that can be self hosted?
Influxdb + Grafana
+1 . just setup an influx driven grafana on a local container. Seems to work ok (DHT11s will need to be replaced though)
nimbits?
Thinkspeak is/was open source: https://github.com/iobridge/thingspeak
I don’t think their current platform is using that same code, but I don’t know that for certain.
I use emoncms.org , it is intended for energy, but works with whatever you want.
I’ve never understood some peoples driving obsession with having every other thing they own needlessly connected to the internet. Kinda hope I never do :P
I agree this is boy with a hammer taken to the limit. While I can see some utility with this degree of fine control in some business/institutional situations, it is simply overkill for a private dwelling.
It’s not needless. The internet connected part comes from benefits of remote access and a logging service. For the most part I think there’s a desperate need for an easy to setup home of things alternative to what we are doing today, but really the problem is that nothing is universal. Most companies provide something proprietary and that drives users to put it on the internet without actually having to.
remote access should be minimized and logging should be done locally. On a FruitPi like device if you do not want to waste the power with a continuously running PC. Or perhaps with some application on an OpenWRT based router or a tablet computer.
This is just not the kind of data I want in the hands of general public or a third party service provider.
I use it for remote security, but I’m sure it could be used for personal SaaS, to getting the needed market data to drive a smart thermostat (electric or gas cheaper?)
This is a variation on the old wireless power meter issue where reading the signal of the meters, and doing a bit of radio finding work, will let you profile a given house’s activity level which you can then use for criminal purposes.
All the sensors on your mobile phone are a more generalised form of this threat.
Having data remotely accessible does have its advantages for some people. Unfortunately to do it easily usually means lack of security. It’s not often at the forefront of your mind that what data I’m looking at in the privacy of my office can also be seen by anybody else – it’s kind of like your in your house at night with the lights turned on. You can see clearly everything inside and nothing outside and in your mind you are in a private place but so totally oblivious to the fact anyone outside can see straight in.
Keeping security/privacy at the front of your mind is somewhat difficult when your focused on developing a cool project for your personal gratification.
Facebook posting:
Going on a shopping spree in another state won’t be back for hours Oh they joy of too much money … :-?
Yes some people mistake Facebook for their diary.
With the amount of data we are talking Internet seems unsafe overkill. Why not a dialup modem or SMS, most important data would not take more than a few kb, maybe more with some light crypto and simply obscure format.
“Someone in Szechuan China is using the internet to turn our lights on and off”
https://www.youtube.com/watch?v=0kzjqBacF1k
What, not [Marv] and [Harry]?
IOT devices are usually good for people who travel. Got to the airport and forgot to turn down your thermostat.. no problem log in and turn it down. The issue of boy with a hammer comes in on things like toasters and refrigerators with forced cloud connectivity. Every IOT device should be able to operate in a stand alone fashion with an option for local cleartext protocol or over an SSL connection with proper documentation. I don’t buy devices that don’t fall into this category. That way security of the devices is totally up to the end user.
Intranet of Things is much superior technology in my experience..
The “S” in IoT is for security
In my experience, you have to explicitly provide lat/lon to the ThingSpeak channel, so it’s pretty easy to remain anonymous, location-wise. ThingSpeak does NOT use the uploading IP address to get location. So in fact in the example above the person creating the “channel” went out of his way to give his location (or perhaps gave a bogus one?)
Geocoordinates? Great!
That’s most user friendly. For the burglars. Just imagine a newfangled app: “vacant homes near your current location…”.
Ugh.
You are correct. ThingSpeak channels have to be specified to public and location data is optional. Most channels are private. In some cases like our weather station, we are deliberately sharing the channel publically so others can use the data in weather data analytics.
Is it only me or this is the poorest/quickest/emptiest article ever written for hackaday? Jesus Christ, I do understand the point of it (“privacy”) but an 174-word stuff can’t even be considered eligible for “hackaday article”, right?
Why do so many feel the need to whine about the purported “quality” of the articles that someone else wrote, and hackaday is publishing online for you to read for free?
I still believe that this falls under the category of: “if you think you can do better, then go ahead and do it? No-one is stopping you.”
It is far more helpful to use the comments section to discuss something actually relevant to the article. How to replace these insecure services with ones hosted locally? Or how to flash new firmware that uses ssh, or calls to a server over https. Or alternative solutions that may offer a secure service…
Agree. Only glowing praise hence forth! All others culled!
Mr. Anon, that is exactly my point! let me explane it to you: Hackaday often opens job positions for article writers, for anyone to apply (people like me and you). I have been flerting with the possibility of applying for the last two opportunities, but NEVER DID. Do You know why? I KNOW I WON’T BE ABLE TO KEEP THE BAR HIGH ENOUGH, so therefore I DO NOT APPLY. If one is going to write for hackaday, one has to understand the opportunity and responsibilities of the duty. That’s all .
Also, Mr. Anon, have a look at the lenght of ALL his articles http://hackaday.com/author/thehacksmith/ . They all sit at the 140-150 words. Is it what hackaday stands for, and asks for? NO. And as a part of this community I feel in the right of bringing this discussion to light.