Small aircraft with streaming video cameras are now widely available, for better or worse. Making eyes in the sky so accessible has resulted in interesting footage that would have been prohibitively expensive to capture a few years ago, but this new creative frontier also has a dark side when used to violate privacy. Those who are covering their tracks by encrypting their video transmission should know researchers at Ben-Gurion University of the Negev demonstrated such protection can be breached.
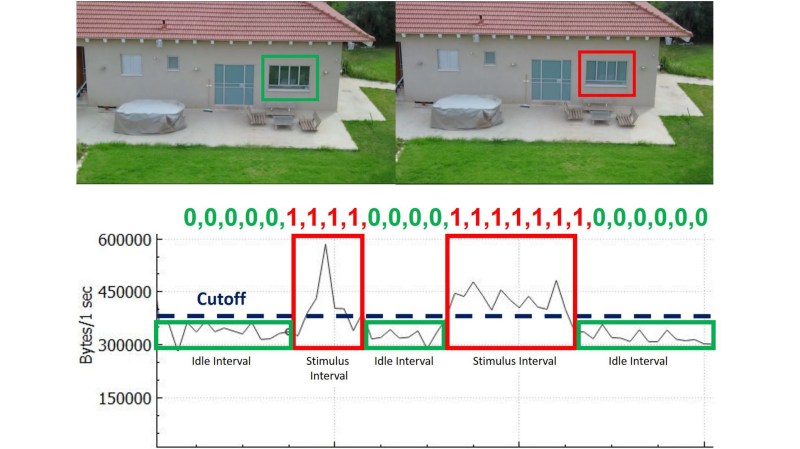
The BGU team proved that a side-channel analysis can be done against behavior common to video compression algorithms, as certain changes in video input would result in detectable bitrate changes to the output stream. By controlling a target’s visual appearance to trigger these changes, a correlating change in bandwidth consumption would reveal the target’s presence in an encrypted video stream.
The idea demonstrated here is early and share challenges common with every side-channel attack: teasing signal out of noise. The signal may be misinterpreted resulting in a false positive, or the technique can be circumvented by adding more noise. Future research will surely pursue both fronts, just as surely as some FPV equipment makers will work to evade detection (careful what frequencies you use) and some people will take a more direct approach to deterrence.
[via Wired]










Seems like a lot of trouble to watch my cat take a shit on a cold morning…
Remember R34
What is this about?
Internet rule #34 – Generally accepted internet rule that states that pornography or sexually related material exists for any conceivable subject.
A valid concern in a world where fences no longer have any meaning.
so you only have to stream the whole video and analyze it somewhere else…. might be harder on the drones battery?
If you stream the video, this technique will detect your drone. It detects streaming.
Uuuh…the drone is already streaming the video. That’s the point of this, they grab the video stream and analyze if the bitrate changes when the filmed subject changes.
To avoid this you’d actually have to do the opposite, record the video on the drone without actually streaming it. Which is not possible with the usual storebought consumer drones.
Or just pad out the data stream such that the bitrate remains constant.
Or just use a CBR to start with…
Even cbr is inherently variable, it just has a fixed target bitrate and less allowance to go over. Though it does mean the variance is generally less. The only way to have a true fixed bitrate is to pad the blocks in the stream with random data. With nearly any compression, the output depends on the input. Different data will compress differently and that’s what’s exploitable. It’s even more troublesome in the more efficient lossy transform codes, as their bitrates tend to vary more widely.
Rather than constant, why not make it random?
>>To avoid this you’d actually have to do the opposite, record the video on the drone without actually streaming it. Which is not possible with the usual store bought consumer drones
This is the normal behavior of cheap (<200USD) quads from China you buy in the mall. Slap in an SD card, buzz around and hope you've got interesting footage.
Huh?
I have yet to see one of those, tbh. Most cheapo quads i’ve seen with a cam on them had some sort of wifi link to transmit video to your phone.
“ARE YOU THE STAR OF AN ENCRYPTED DRONE VIDEO STREAM?”
No, HIGHLY unlikely, but meanwhile, how many people have paid to install for the sake of trivial conveniences an always listening and, with the new models, always watching internet connected device sending data to the cloud for a huge corporation to do anything it wishes with.
Since this is Israeli research I’m guessing this might be also relevant in regards to Hezbollah or IS or such groups drones.. and that is a whole different kettle of fish.
And tagged onto that of course the CIA and military intelligence of the US and their opposites, like NK drones for instance.
If a drone is in your airspace violating your privacy, then you’re permitted to use a jammer or signal scrambler to disrupt the signal & bring it crashing down. Better yet, drone-seeking pet hawks! ????
No, it is much more fun to engage in a drone dogfight
Intruder reconnaissance drone breached our perimeter!
Launch the fighter drones!
Honey, kids, everybody, BATTLE STATIONS!
The family: “Wheee!”
Hacker cred special bonus for the first one who trains their pet dog to pilot a drone in a dogfight. “Curse you, Red Baron!”
Comments like this make me wish HaD had a moderation system like slashdot.. +5, Funny :-)
I don’t think you are permitted to do that… consider other devices your jammer will affect.
Now, if you’ve identified the exact wifi connection maybe it would be okay to flood it with deauths…
Yeaaaah…no. I don’t think the usage (or even posession) of a jammer is allowed anywhere.
Who’s gonna know? Directional antenna, bring it down, setup back to the closet.
You would have to jam not only the control frequencies and the GPS frequencies as well.
Because most intelligent models have a return to home mode if the control signal is lost.
Now the simple FPV systems that do not depend on GPS, thats a different story.
And in the US a Drone or UAV is considered a protected aircraft.
Downing by any means is a federal offense.
Please be aware that my yard isn’t your airspace.
If you crash my drone because seeing it flying above my house “triggers” you, you’ll be paying for a replacement.
If you cannot tolerate living in proximity to other people without dictating what they do in their free time, I highly recommend you leave civilized society a la the Unabomber.
No, you’re not.
Hi Guys,
My comments:
1. Transmitting mock data decreases the amount of original data that the drone can send on the channel so you eventually it limits the drone to lower resolutions instead of using its HD capabilities.
2. Detecting a nearby drone is something that was done 20 years ago. However, the difference between a legitimate use and illegitimate use of a drone is sometime depends on the angle of the drone’s camera rather than the drone’s location (as you can see in the film). This is the first technique that extracts streamed target from an encrypted channel.
3. While some of you might say, that they will not stream the video captured by the drone to its operator, others that already used a drone understand that you cannot maneuver a drone without FPV channel. New drones provide their pilot the ability to fly a drone for few kilometers. How do you suggest to maneuver the drone without video streaming 5 kilometers from your location?
Thanks
Ben
The easy answer is to just establish a “No Fly Zone” around your property. A 12 gauge is helpful in enforcing it. Of course, don’t do this if it is illegal in your jurisdiction to do so.
You know, there are anti flight zone mechanisms.
Most cities have laws about discharging weapons.
And the FAA will have a problem with it also.
So throw/launch a net at it. Hard to call that weapon, let alone a lethal one. Bring it down, strip it of its useful parts, finish the job with a baseball bat or a shredder.
Yes they do, but here in KY in the county, no problem. I do not think the FAA has any jurisdiction on the airspace below 1,000 feet over my property. As power hungry as these government agencies have been over the past 10 years, it would not surprise me if they thought they did.
Can’t we please just ban drones? What is the actual point of them apart from invading privacy and smuggling contraband into prisons?
Better ban RC aeroplanes, hot air balloons and recreational light aircraft too then.
The entire fun of drones as a hobby is the first person view part combined with a headset, but currently they for 95+% use old style SD video cameras because HD streaming is very pricey for normal hobbyists.
It’s like a action game where you are a jet pilot and big fun flying around without needing to sign up with the airforce and getting years and years of training.
Honestly, I don’t have a FPV setup and it’s still a lot of fun just doing laps and loops with my cheap Syma x8c. I got my neighbor’s permission to fly around his yard too, and there’s a vacant lot next to him, so I can pick up some decent speed before I have to turn around.
That’s also why this talk of fixed wings taking over is nonsense, fixed wings are cool and all but who has the damn space? you need miles of empty space for those things while a little drone can be fun in something as small as the garden.
They’re fun? It’s a free country so people are allowed to do what they want in the privacy of their own homes.
What’s the point of a motorcycle? What’s the point of high-end GPUs? Knives? 10W lasers? Drag racing cars?
Anything can be used maliciously. Here in America it is generally thought that people should be left alone unless they are hurting someone somehow.
If you want a totalitarian government that tells you what hobbies you can and can’t participate in, there’s plenty of dictatorships in the world to choose from.
You make some good points. But, I do think that multicopters/drones present some quite tricky challenges that other ‘fun’ things don’t, especially in terms of privacy and nuisance, partly due to their availability and ease of use (compared to RC planes etc).
Can’t we just ban cars? They kill thousands of people every day.
In a way we are. No more non-autonomous cars.