The most important rule of password use, especially when used for online logins, is to avoid reusing passwords. From there, one’s method of keeping track of multiple passwords can vary considerably. While memorization is an option in theory, in practice a lot of people make use of a password manager like Lastpass or KeePass. For those with increased security concerns, though, you may want to implement a USB password keeper like this one based on an ATtiny.
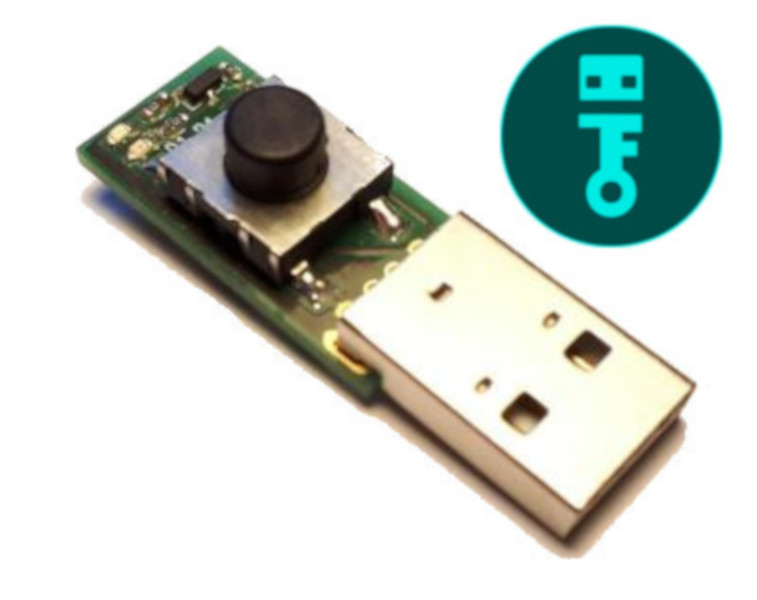
This password keeper, called “snopf”, is a USB device with an ATtiny85 which adds a layer of separation to password keeping that increases security substantially. Passwords are created by the USB device itself using a 128-bit key to generate the passwords, which are physically detached from the computer. Password requests are made by the computer to the USB device, but the user must push a button on the snopf in order to send the password to the computer. It does this by emulating a keyboard, keeping the password information off of the computer’s clipboard.
Of course, snopf isn’t perfectly secure, and the project’s creator [Hajo] goes into detail on the project’s page about some of the potential vulnerabilities. For most use cases, though, none of these are of serious concern. Upgrading your password keeper to a physical device is likely to be a huge security improvement regardless, and one was actually developed on Hackaday a few years ago.















Can this install on a digispark for example? I realize I would need to add a button, but I would prefer a remote button anyway
I would think so, both are ATTiny85 talking USB. The Digispark is even simpler in hardware design though, it lacks the external crystal, freeing up two more pins for I/O
> it lacks the external crystal, freeing up two more pins for I/O
You could alter the snopf design to use the chips’ oscillator too but personally I feel better using a crystal for the USB stuff.
The USB is the whole reason the internal oscillator is preferred. None of the common crystal speeds are perfect for USB, but the internal oscillator in the ATTiny85 is very accurate and precisely tuneable. It is not comparable to the more typical case of using an internal oscillator. That feature is a major part of why the `85 exists and why it is used in USB devices.
this would be nice too, the attiny85 lives within the USB. For a snopf, the buzzer should be replaced by a button. https://mitxela.com/projects/silly_synth
Take a look at Tomu (or Fomu) development boards: https://tomu.im/
There already is a basic dispark version of this, available on github 🙂
link?
I think this should be possible, all you really need is an ATtiny85. And it looks as if the digispark board uses software USB for communication too? No idea though how much space is left on the board (I guess there is a bootloader on the chip already?) and you’d have to adjust the V-USB driver to use the chip’s oscillator etc.
On some microcontrollers you can use the ADC to get capacitive touch detection with no extra hardware: you can detect the user just touching the pin. There are Arduino libs for this. I think I saw an online discussion that you can do this on a Digispark, too.
I like the way my Yubikey approaches the button issue. It’s a flush, touch design. Not easily damaged.
It’s a capacitive touch button I guess?
I agree, that’s a good idea and also makes a casing design much easier.
a bit like a YubiKey but since it emulates a keyboard it probably needs far less software installed. Although I must admit once you have all the plugins for chrome and ssh installed Yubi is very slick.
Some Yubikey models can also emulate a keyboard.
I don’t remember the details anymore but I didn’t like the password generation / storage details for the yubikey. (IIRC it was pretty restricted in number of passwords etc.)
Apart from that, it kinda resembles a yubikey for services that don’t allow for 2FA / FIDO2..
Cool idea. You can do this with an ESP32 using a bluetooth keyboard emulation. Total cost = 4$
I would encourage you to go that route, but I have no idea whether your passwords get into anything interesting.
Any PC or smartphone accepting bluetooth HID…
No I meant I don’t know whether it’s worth prodding you into making it, then lugging a bluetooth sniffer on a yagi out to your neighbourhood and following you around for hours, because you might only be using it for instagram and tumblr :-D
In the Olden Times it was more dangerous, but these days you’d have to catch them during the pairing process, after that it is more secure.
Well the modern protocol design is like a $1000 super lock, that everyone uses with a rusty chain and a gate that can lift off it’s hinges.
I just finished it. When lit the device tries to pair – you can check on your computer if it does or not and you need a pin to confirm. Then you can send the password.
It is just like a rusty chain; people look at it and worry, but the rust is only on the outside surface and the strength of the chain hasn’t changed.
As for lifting the the gate of it’s hinges, if you found that, tell a security researcher so they can credit you when they publish, you’re going to be famous!!!
Yes, I was thinking about that do, especially for smartphones. But bluetooth and security is another can of worms! 🙂
I don’t think it is that easy, because the way this password keeper works is, that the computer/browser plugin sends a request for a certain account/website to the password keeper via usb. The password keeper than looks for the password for that account and only send it after the user pushes the button. I don’t know if the request part is that easy via bluetooth.
Well, I didn’t dig into this so far but I don’t see a general problem doing the same stuff using bluetooth.
My version is simpler : I have a two buttons device. The first one is a “mode” button allowing you to select different password options. The second one is a “log” button sending the code as a bluetooth keyboard. As simple as that !
Onlykey is another option, hardware password manager and 2FA
Yes, there are some other options as well, Mooltipass is another example. And I think 2FA/FIDO2 is a nice development. But so far there are still many services that still just rely on passwords only.
TBH I built snopf because for every product I found there was something I wasn’t happy with (tech, not open source, handling..). But I guess that also includes NIH syndrome. 🙂
Hope you have a good way to back up as the key can be lost,ESD, damaged etc. Also might want to consider a way for your next of kin/estate to get to some of your accounts.
Yes there is a good way to back up the key!
You should set the key on the device yourself anyway and you can get the key as a 12 word mnemonic to safely store it somewhere (or write it to a second device)
Great ubtil you need to login anywhere ln your phone.
if you would read on the github page, there is an app for that, and for my android with USB C at least, I have an USB 2.0 A to USB C adapter on my key chain. I use it for my typical usb stick (USB 2.0 A) and my FIDO stick if I need it on my phone.
Well, for that I wrote a (rudimentary so far) android app. So you can use it with your (android) phone already!
The FinalKey still seems like a viable option, though I’ll admit this is smaller, I prefer having a wire on mine so I don’t stress the usb port
Never mind the technical details; I’m going to lose that tiny thing in a week!
I really like this one and hope this will become a mature product/project