So first off, remember the Unc0ver vulnerability/jailbreak from last week? In the 13.5.1 iOS release, the underlying flaw was fixed, closing the jailbreak. If you intend to jailbreak your iOS device, make sure not to install this update. That said, the normal warning applies: Be very careful about running out-of-date software.
Apple Sign In
An exploit in Apple’s web authentication protocol was fixed in the past week . Sign In With Apple is similar to OAuth, and allows using an Apple account to sign in to other sites and services. Under the hood, a JSON Web Token (JWT) gets generated and passed around, in order to confirm the user’s identity. In theory, this scheme even allows authentication without disclosing the user’s email address.
So what could go wrong? Apparently a simple request for a JWT that’s signed with Apple’s public key will automatically be approved. Yeah, it was that bad. Any account linked to an Apple ID could be trivially compromised. It was fixed this past week, after being found and reported by [Bhavuk Jain].
The Cursed Wallpaper
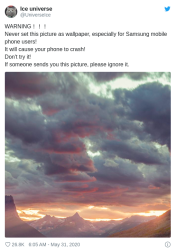 So when someone posts an image on twitter, and warns everyone to *never* use it as your phone wallpaper, what’s the logical thing to do? Apparently it’s only appropriate to immediately set it as your phone’s wallpaper, and then complain that it renders your phone unusable. So what’s going on?
So when someone posts an image on twitter, and warns everyone to *never* use it as your phone wallpaper, what’s the logical thing to do? Apparently it’s only appropriate to immediately set it as your phone’s wallpaper, and then complain that it renders your phone unusable. So what’s going on?
The image in question uses a special color-space that the Android UI isn’t equipped to handle. That particular picture has a color value over 255, which is out of bounds, causing a crash in the UI. Once the Android UI has crashed, it’s impossible to change the wallpaper, leading to a crash loop. A few users were able to switch out their wallpapers in the few moments between crashes, but the surest way to clean up the mess is to manually remove the image using something like TWRP.
Exim and CVE-2019-10149
This vulnerability is one that keeps on giving. We talked about CVE-2019-10149 just about a year ago. This week, the NSA published a warning (PDF) that certain state actors are actively exploiting this Exim bug.
For a quick refresher, the Exim mail server is the most popular mail server on the net. CVE-2019-10149 is a clever exploit that tricks a vulnerable server into trying to send an email to a specially crafted address, hosted at a malicious mail server. When the target machine tries to send a bounceback message, the malicious server sends a byte every four minutes, forcing the connection to stay open for a week. This strategy ensures that the vulnerable code is hit. When the message is finally sent, the payload embedded in the email address is evaluated and executed.
The NSA warning specifies the Russian GRU as the culprit, acting under the name Sandworm. There’s likely quite the story behind how the current attacks were discovered to be of Russian origin. As none of the indicators of compromise are directly tied to the GRU, we’ll just have to take the NSA’s word for it, but of course they’re not going to make public how they get their counter-intel either.
In further GRU news, the UK has officially attributed to them a series of attacks on the country of Georgia. These attacks shut down the Georgian power grid, encrypted hard drives (ransomware), and directly damaged financial systems. And just last month, the German government attributed hacks on their parliament to one particular GRU officer: Dmitriy Badin.
Attributing cyber attacks to a particular actor is always tricky, especially when savvy foreign intelligence agencies which don’t want to get caught are behind the work, but the fact that multiple government agencies are converging on the same conclusions is more persuasive. The German evidence, collected over five years and pointing to a particular agent, is particularly so.
Stolen Nuclear Missile Secrets?
Our final story comes from Sky News, who breaks the news that Westech International was hit with a ransomware attack. As you may have guessed, this section’s title is Betteridge’s Law in action, albeit ironically.
So what really happened, and why is the “nuclear secrets” angle almost certainly bunk? First off, Westech isn’t a huge engineering firm, and they haven’t worked on designing any nuclear weapons systems. Go to their website, and look at the contracts they have and services they offer. Telecommunications, maintenance, and logistics planning.
Secondly, we know that the ransomware attack hit the machines doing their payroll. Classified information is subject to a strict set of rules in the US. It’s only to be kept and used in a Sensitive Compartmented Information Facility (SCIF). Computers containing classified information are never to be connected to the unsecure network. There is even a dedicated Secret Internet Protocol Router Network (SIPRNet) that is only for secure communications and only accessible from a SCIF. All this to say, if a ransomware attack can ex-filtrate data back to an attacker, then somebody royally messed up in a way that often leads to jail time. It’s a long way from payroll to nuclear secrets.
Rooting Your AT&T Gateway
[Andrew Dupuis] had an Arris Fiber Gateway provided by AT&T, and like many a hacker, he wasn’t satisfied. Before we dive all the way into the rabbit-hole, we should point out that AT&T is charging $10 a month for this device, and refuses to let their customers use their own hardware instead. [Andrew] believes that this probably violates FCC rules. In any case, he wanted to run his own gateway instead of being locked into AT&T’s. The fiber connection uses 802.1x security on the physical connection, which also serves to lock customers into the official hardware. If a user could extract the 802.1x certificates, they could replace the official AT&T gateway with their own hardware, which is the point of the writeup.
The exploit itself starts with a firmware downgrade, back to a version that still contains the vulnerability. The vulnerability? A REST server intended for troubleshooting and debugging. A bit of work later, and the hardware is rooted, with a telnet server just waiting for you. It shouldn’t be very surprising, the OS under the hood is a standard embedded Linux. The first order of business is to disable the auto-update function, to avoid getting locked back out of the device.
[Andrew] explains how to properly secure the gateway, and re-tune it for better performance, good ideas if you intend to continue using it in your network. The real goal here is extracting the certificates. I’m not sure how much of a surprise it should be, but it seems that every device uses the same security certificates, and [Andrew] was kind enough to share the copy he extracted.
[Andrew] sent this in on the Hackaday Tipline. If you have research to share, or came across something you think we should cover, be sure to let us know about it!
















Dang!
Now I want to use that image as my phone’s wallpaper!
Go ahead! Tell us what happens!
You can get wallpaper on a Nokia 3310?
“Classified information is subject to a strict set of rules in the US. It’s only to be kept and used in a Sensitive Compartmented Information Facility (SCIF).”
That’s not strictly true. If it were you’d never see a “Classified Copying in Progress” sign on the copy room. Paper still exists.
I think that turns the copy room into a SCIF, doesn’t it? :P That’s how this works, right?
Yeah, no. The Coast Guard Academy spent $250,000 on one and the room was already there. But think of the savings if the “put up a sign” method actually worked. The President’s Daily Brief, which is born classified, is transported to the White House by car. No “Classified Stuff on Board” sign. :)
Security by obscurity 😁
Wouldn’t that case issues with the copier? As many modern one’s have found to store copied files on the internal hard drive for considerable time.
Very much so. They are also often improperly configured. I recall many many moons ago our IT dept came around looking for the smarty pants running edonkey eating up bandwith but found someone had set up a servlet remotely on a copy machine to distribute warez lol. We were all a little impressed.