All of us have seen our share of phishing emails, but there are a lot more that get caught by secure email gateways and client filters. Threat actors are constantly coming up with new ways to get past these virtual gatekeepers. [BleepingComputer] investigated a new phishing attack that used some old tricks by hiding the malicious script tags as morse code.
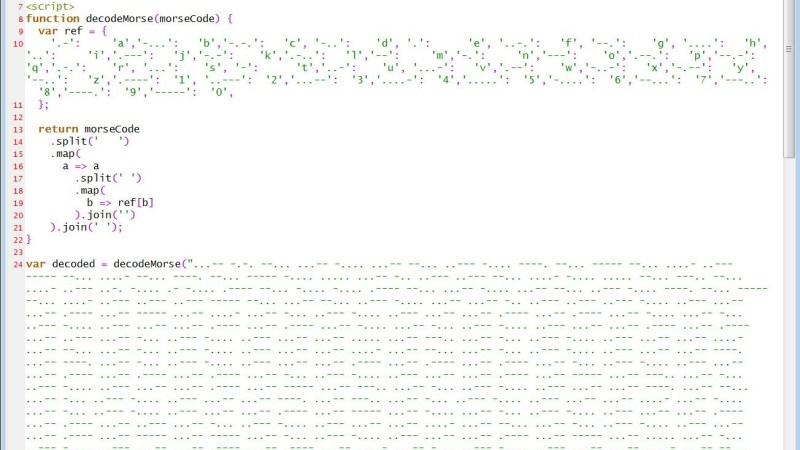
The phishing attack targets Microsoft account login credentials with an HTML page posing as an Excel invoice. When opened, it asks the user to re-enter their credentials before viewing the document. Some external scripts are required to render the fake invoice and login window but would be detected if the links were included normally. Instead, the actor encoded the script links using dots and dashes, for example, “.-” equals “a”. A simple function (creatively named “decodeMorse”) is used to decode and inject the scripts when it runs in the victim’s browser.
Of course, this sort of attack is easy to avoid with the basic precautions we are all familiar with, like not opening suspicious attachments and carefully inspecting URLs. The code used in this attack is simple enough to be used in a tutorial on JavaScript arrays, but it was good enough to slip past a few large company’s filters.
Phishing attacks are probably not going to stop anytime soon, so if you’re bored, you could go phishing for phishers, or write some scripts to flood them with fake information.















“carefully inspecting URLs” this sounds so easy and technically speaking this is so completely true.
However, if you do not know the exact URL (because, hey.. many people enter a site via a search engine or a given link even more people don’t even know what the word URL means but that’s a different topic). Or how about a fake URL being almost completely identical to what it should be. Well then you are screwed.
It is all most exactly like a police officer showing you an ID-card or badge when you ask for identification.
How the @#@$# should you know how such a badge should look like, how are you supposed to know how the real thing looks if you never seen a real one before?
Only unless the fake URL (or ID-card) is so horribly faked that it sticks out like a sore thumb then you might be able to detect the problem. Otherwise, you can’t! So in short… “carefully inspecting URLs” is true in many ways, but in real life this “advise” would not protect you from real harm in serious scams. This doesn’t mean that you shouldn’t check, nope, always do and hope for the best.
Also, some browsers actually hide the full url path and only show the tld…w..t..f (chrome on win10).
The LA Times recently had an in depth article on this…
https://www.latlmes.com/tech/url-phishing-at-epidemic-levels-say-security-researchers-1
+1
+1
+1
Interesting that they use Morse code now! However, it’s important to remember that there’s an infinite number of ways to encode such an email and I’d go as far as to suggest that you could easily make a (somewhat complex but workable) script generating a novel way for encoding a page for every single request – making non-convoluted “spam filters” quite useless. Well, especially these spam filters that can’t notice there’s an attachment literally with “.xlsx.hTML” extension =D
At that point you’d probably have to just render the page and use OCR and automation to find links and simulate a user clicking on them and see what it does. Simply blacklisting specific keywords and code snippets can only take you so far…
“Or how about a fake URL being almost completely identical to what it should be.”
Uh, yeah… That’s kinda *how you make a fake URL*.
I’m against phishing in general because it’s just wrong, but this approach is pretty cool.
Next time you need a web search, go to goggle.com
B^)
root@…:~# cat /etc/postfix/blocked_attachments
/name=[^>]*\.(pdf|doc|txt|xls.?|doc.?|ppt.?)\.(zip|exe|rar|lha|ace|7z|r[0-9][0-9]|html)/ REJECT Deceptively named file
/name=[^>]*\.iso/ REJECT ISO image: Anything small enough to send by email, please send in another format or consider using a file hosting service.
root@…:~# grep -F blocked_attachments /etc/postfix/*
/etc/postfix/main.cf:mime_header_checks = pcre:/etc/postfix/blocked_attachments
That might help those who are responsible for Postfix-based mail servers. That filter has been protecting my workplace for some time now… but this article made me consider the {xls?,doc?,ppt?}.html case (added this evening).
Where’s the orbital bombardment from space? You need to add that.
var -> const damn’ it!