With so many online messaging services to choose from it’s almost as though the daddy of them all, email, has faded into the background as something you only use for more formal contacts. But it’s still the underpinning of much of the business world’s electronic communication and is likely to stay so for the foreseeable future. The BBC Archive takes us back to a time when email was relatively new, when in 1986 [Lesley Judd] takes a very chunky 1980s laptop on a plane from London to the Netherlands, and sends an email to her colleague at home using a payphone and an acoustic coupler.
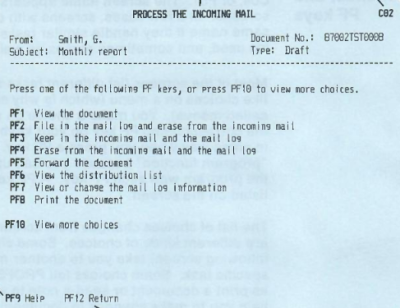
There are so many of-their-era quirks in this film it’s difficult to pick, but little things like the aircraft still having smoking and non-smoking areas, there being no sign of a mobile telephone, or the payphone operating in Guilders rather than Euros make it from a different time. Perhaps most interesting though is the email system in use, because this isn’t an internet based service. Instead it’s using Telecom Gold, which was the UK telco BT’s online service offering to businesses, and part of the international Dialcom network. This was a commercial service which hung on until some time in the 1990s when the Internet finally displaced it.
The British writer L. P. Hartley used the phrase “The past is a foreign country; they do things differently there” as the opening sentence of one of his books, and the film below the break certainly brings that to mind. It’s a time that’s within reach, yet the changes in information technology over even the next decade or so would make the tech depicted not just obsolete but almost unrecognizable. Most of us today could sit at a 1996 laptop and send an email, but few of us would be as immediately at home with Telecom Gold.
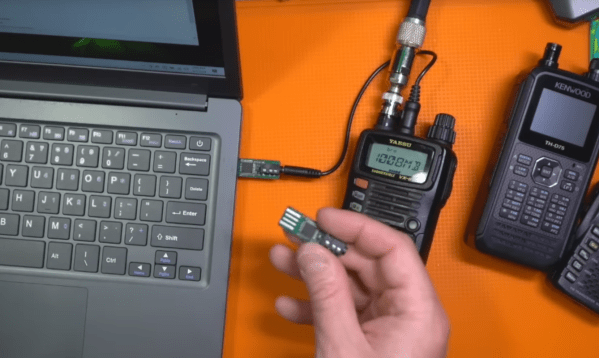
It’s still possible to use an acoustic coupler today though.