Modern cellular networks are built to serve millions upon millions of users, all while maintaining strict encryption across all communications. But earlier cellular networks were by no means so secure, as [Nostalgia for Simplicity] demonstrates in a recent video.
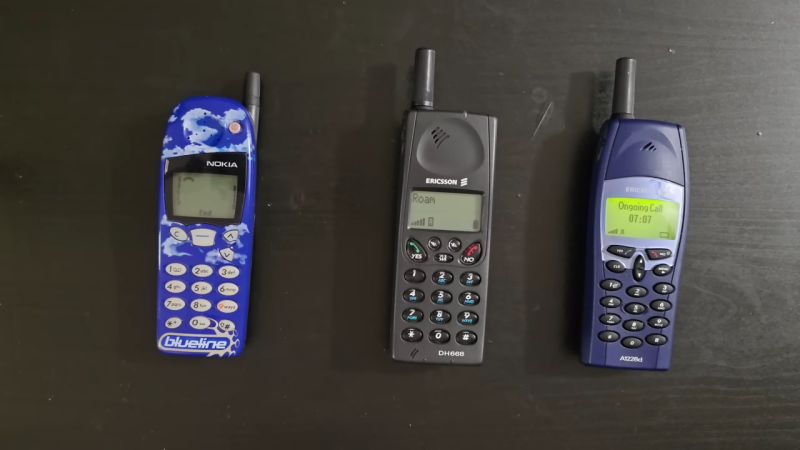
The video begins with an anecdote — our narrator remembers a family member who could listen in on other’s conversations on the analog AMPS phone network. This was easily achieved simply by entering a code that would put an Ericsson handset into a test mode, in which it could be switched to tune in any desired AMPS channel. Since the communications were transmitted in a purely analog manner, with no encryption of any sort, any conversation on such a network was basically entirely open for anyone to hear. The video shows a recreation of this method, using a software-defined radio to spin up a low-power, very local AMPS network. A phone call is carried out between two handsets, with a third handset able to listen in just by using the special test mode.
If you’re particularly keen to build your own first-generation AMPS phone network, just know that it’s not really allowed due to rules around spectrum allocations. Still, it’s entirely possible as we’ve covered before. It doesn’t even take much hardware in our modern SDR era.















Back in the day all one needed to listen on cellular conversations was an old TV with a UHF tuner.
The FCC took UHF channels 70 to 83 and divided it between the Trunked radio service (806-869 MHZ and the new analogue cellular phone service (870-896MHZ).
Even before that RCC and IMTS mobile phones had no security, all analogue, all the time.
I had that exact Ericsson 1228d in blue shown in the header in high school and yes, it was that easy, whenever I got bored i just tuned into other people’s conversations. As you had to try a different channel each time and each part of the conversation was on a different channel the eavesdropping was one way only.
The analog landline of the 20th century had no security, either.
In my home country, in the 90s, the T-Online Classic online service (aka BTX, Datex-J) had no encryption, either.
That wasn’t added until about the 2000s, I think.
(The service remained in use until late 2000s, mainly for online banking without requiring the unsafe internet.)
So at the time, tapping the line was possible,
a hacker in the cellar of the building could read the raw data with a modem and a terminal program.
A hacker could write down the data, re-establish the connection to the online service
and re-send the altered information of, say, a bank formular.
The only security was the obfuscation of the login data via using different
baud rate/polarity during log-on.
And the user wouldn’t even been suspicious in most cases,
because modem disconnects due to bad line quality happened sometimes.
There’s a video of a news reports.
https://www.youtube.com/watch?v=Sr62RbKPy6U
German B-Netz (1972-1994) was unencrypted. 27.000 users (peak & max. limit) on a silver plate.
I don’t remember B-Net anymore,
it was before my time, but I recall that the C-Netz was still in use.
One C-Netz auto telephone, Siemens C5, was known for being modded for amateur radio use.
It could be used as 70cm band two-way radio.
http://www.oebl.de/C-Netz/Geraete/Siemens/C5/C5.html
The D-Netz (GSM) was the rising star from 1992 onwards or so.
I remember how the Motorola MicroTAC was commonly seen, as well as the old Hagenuk phones.
One had Tetris, I remember. Model MT-1200 or so. We had an MT-900..
I can imagine how the conversation went, “How do you stop people from tapping the line?” – “But you can’t do that.” – “Yes, but how do you stop people doing that?” – “You can’t do that. It’s illegal!” – “Yes, but what if somebody….” – “NO! It’s illegal! You can’t do that!”.
I’ve had this conversation with Germans before.
It’s clear no German ever tapped a line, they are physically unable to
As a German, I have to say that’s pretty accurate. 🤣
Not sure if I should laugh or cry, though. 🥲
Fair play for being a good sport :-)
Similar story from my English Boss at a Swedish university examiners meeting. It goes that the departments get paid based on the number of students that pass – so my boss pointed out that isn’t that going to cause issues whereby those who set the grades are those who get paid for good grades? The look on the Swedes faces was just shock that anybody would think of such a dishonest plan!
NMT phones. If you parked close to the mast then you could pick up various calls on your car radio.
When the first Generation cell phones were becoming very popular I was debugging a relitively secure spread spectrum TxRx connection that was losing sync. This was taking place at about 915 megahertz. On the spectrum analyzer I could see lots of signals pop-up communicate for a minute to 10 minutes, then go away.
I moved the pointer, dropped in on one of those signals, and heard somebody giving their banking information, all access numbers, everything.
And credit card numbers. That was an eye opener. How could we have done that? It was just so easy to pick up.
I spread the word, but not everybody believed me. They said it would be too stupid to do anything that non-secure and not inform your customers.
And if you ever want to design a spread spectrum system that can latch on and synchronize to your spread spectrum sequence make sure the transmitter and the receiver are using the same type of logic chips at the same voltage when generating the analog voltage that drives the transmitter and receiver frequency tuning. The experts that designed that system totally missed that basic requirement. And they went out of business a little bit later.
Another clickbait.
AMPS was literally 1980s brick-phones so it’s not surprising it had no encryption.
https://upload.wikimedia.org/wikipedia/commons/7/74/DynaTAC8000X.jpg
But I suppose some dumb pajeets will still type those codes on their smarthphones, hoping to hear voice of a female neighbour for the first time in their designated incel life.
AMPS was still available in dual(Tri) mode phones into the 2000s. And rural areas in the US still used it for coverage
I had AMPS in a pocket Sony, CM-R111. Last time I used it was in HK, around 1996. I didn’t have a subscription there but it still picked up the cells. It’s so old you can barely find it o the internet (AI doesn’t know about it lol)
The 90’s were great. I had a friend that used to purchase the BT/Cellnet Philips C12 from Boots for 50 quid. Shove a 12C508 PIC inside, then sell them for 100 quid. helped fund a year of university. Those old phones stored credit on the phone, so using a PIC to copy and erase the EEPROM prior to making a call allowed the phone to stay topped up when it dumped the EEPROM back in on boot.
Yeah – when Vodafone introduced pay as you go, it caught Cellnet off guard so they did this stupid quick fix of storing credit on the phone & were too dumb to see how bad an idea that was…
Also, the only thing authenticating a phone to the network was the phone number and serial number ( ESN). The latter was a 32 bit number, 16 bits of which would be known if you knew the country,make & model of someone’s phone.
So much dodgy stuff went on back then.
Apparently….
There was a channel 4 program about hackers/hacking back in the 90’s and the frequencies for the deed were transmitted on the TV program which might or might not have worked on 0800 numbers. I’ll never know.
Walk on the Wild Side – Hackers / Phreakers. One of the subjects was a friend who is sadly no longer with us. There was a big stink on several BBS at the time that they’d aired functioning clear/seize tones and several vulnerable trunks reachable via 0800 numbers.
TACS security was a separate matter but equally trivial to crack. ESN/MIN pairs used to change hands by the hundreds.
I uploaded to YouTube about 15years ago but it was taken down. I was good friends with Chris B from their group, used to hang out with them on conf calls (what a novelty back in the early 90s). Amiga was a great tool for that scene, with Robbox (thats not right, R-somerhing, did the same as ToneLoc on PC) and Ncomm my choice of tools. And a list of 0800s of course.
Happy happy days. But yeah, the issue afterwards. And BT changing the low level codes afterwards. Somewhere i have a copy of a voice call ofmthe guys trying to social engineer new codes out of a BT engineering manager.
What happened to my reply….?
I seem to remember being able to occasionally tune in to some audio communications with my VCR by adjusting some sort of thumb wheel potentiometers- I don’t know WHAT they were, but they were interesting, back in the day!
I simply used a radio scanner to tune into the old analog cell channels. Lots of steamy calls and illicit relationships going on. Same with cordless phones, also analog in the early days. Why? Just being able to was a no empty which I soon got bored of!
Anyone remember the OKI-900 ? Can’t recall the alias of the fellow that made a custom chip you’d swap into it, and the program you run on a pc to monitor AMPS calls and even the hand offs.
Or how about the late great Bill Cheek – who the fucking feds really jacked up because he exposed some corrupt politician’s convo’s on their cell – leading to a new law banning the cellular bands from scanners.
I remember tuning my 2m/440MHz radio to receive in the 900MHz cell phone band. Plain as day, but only one side at a time.
” any conversation on such a network was basically entirely open for anyone to hear ” That’s not accurate.
I was a repair tech back in that day, and though partly true, any phone could be put into test mode, and you could listen on a channel but you could NOT hear the conversation. One channel was for one party, and another channel for for the other party. So basically you could only hear one half of 2 people talking.
FREE KEVIN!
In the 90’s I copied the ESN EEPROM (9346) and had 5 3W Nokia/Technophone cells on one service (none ever on at the same time). Service from LA Cellular was US$20/month for 20 minutes. Hacked my scanner to listen to others. Had a couple of OKI 900’s and played with the 5X ESN F/W.
I went the route of unblocking the analog cellular bands on my Radio Shack handheld scanner via a well known fix involving a single resistor. Great fun while it lasted.
The Nordic Mobile Telephone (NMT) network was in use for decades from the 1980’s until 2010. Besides in the Nordics it was also deployed in various countries around the globe. According to Wikipedia it’s peak userbase was around 50 million. It had no encryption whatsoever and if the user wasn’t in a moving car the call most likely didn’t even hop between towers/channels.
The only way that eavesdropping was mitigated (At least in Finland) was the import restrictions for scanners that could tune into 450 and 900MHz bands but there was virtually no oversight.
I remember ordering a scanner from the US and happily tuned into those bands as a teenager until I heard my classmate having a conversation with his mum, which was a bit awkward…
Isn’t the Nokia phone on the left a GSM (2G) phone? I have one (but not in blue) and it takes a SIM card. Unless they reused the case from an earlier analogue model.
Cue Princess Diana leaked cellphone conversations in 1990, and early nineties Mitnick and his OKI 900.