If you work in a secure facility, the chances are pretty good that any computer there is going to be stripped to the minimum complement of peripherals. After all, the fewer parts that a computer has, the fewer things that can be turned into air-gap breaching transducers, right? So no printers, no cameras, no microphones, and certainly no speakers.
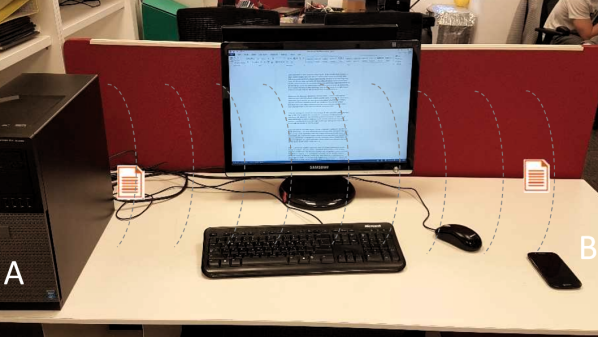
Unfortunately, deleting such peripherals does you little good when [Mordechai Guri] is able to turn a computer power supply into a speaker that can exfiltrate data from air-gapped machines. In an arXiv paper (PDF link), [Guri] describes a side-channel attack of considerable deviousness and some complexity that he calls POWER-SUPPLaY. It’s a two-pronged attack with both a transmitter and receiver exploit needed to pull it off. The transmitter malware, delivered via standard methods, runs on the air-gapped machine, and controls the workload of the CPU. These changes in power usage result in vibrations in the switch-mode power supply common to most PCs, particularly in the transformers and capacitors. The resulting audio frequency signals are picked up by a malware-infected receiver on a smartphone, presumably carried by someone into the vicinity of the air-gapped machine. The data is picked up by the phone’s microphone, buffered, and exfiltrated to the attacker at a later time.
Yes, it’s complicated, requiring two exploits to install all the pieces, but under the right conditions it could be feasible. And who’s to say that the receiver malware couldn’t be replaced with the old potato chip bag exploit? Either way, we’re glad [Mordechai] and his fellow security researchers are out there finding the weak spots and challenging assumptions of what’s safe and what’s vulnerable.
Continue reading “Side-Channel Attack Turns Power Supply Into Speakers”