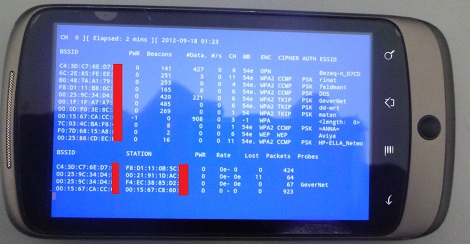
The WiFi adapter in your laptop has a special mode – monitor mode – that can be used to listen in on WiFi traffic and, with a little patience, can be used to crack a WEP password. Surprisingly, this monitor mode can’t be found on any Android device due in part to the limitations of the hardware. A group of three researchers, [Ruby], [Yuval], and [Omri], decided to spend their vacation adding monitor mode to their Android smartphones, allowing for a much more portable version of WiFi pwnage tools.
The phones used by the researchers – the Nexus One and Galaxy S II – used Broadcom chipsets that didn’t support monitor mode. To get around this limitation and allow the OS to see full 802.11 frames the team needed to reverse engineer the firmware of this Broadcom radio chip.
The team has released a firmware update for the bcm4329 and bcm4330 chipsets found in the Nexus One and Galaxy S II. The update may work for other phones with the same chipset, but don’t take our word on that.
There’s still a lot of work [Ruby], [Yuval], and [Omri] need to do. They’d like to add packet injection to their firmware hack, and of course create an APK to get this into the wild more easily.
If you have experience with kernel development and would like to help out, send the team an email. The source can be found at google code if you’d like to play around with it.