Unless you’ve got an especially small lap, calling the Toshiba Libretto a laptop is a bit of a stretch. The diminutive computers from the mid-1990s had a lot of the usual laptop features, but in an especially compact and portable case that made them a great choice for anyone with an on-the-go lifestyle.
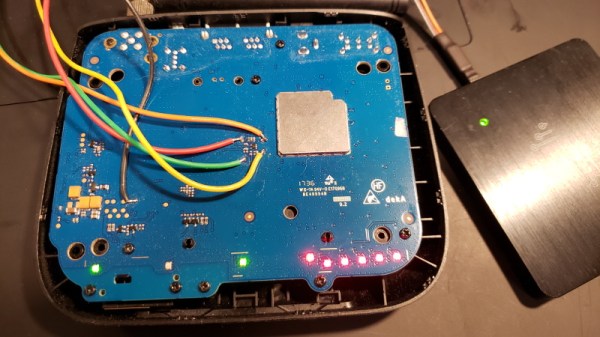
Fast-forward thirty years or so, and the remaining Librettos haven’t fared too well. Many of them have cases that crumble at the slightest touch, which is what led [polymatt] to undertake this meticulous case replacement. The effort started with a complete teardown; luckily, the lower aluminum-alloy shell was in fine shape, but the upper case parts were found to be almost too deteriorated to handle. Still, with a little patience and the judicious application of tape, [polymatt] was able to scan the case pieces on a flatbed scanner and import them into his CAD package. Great tip on the blue-tack for leveling the parts for accurate scanning, by the way.
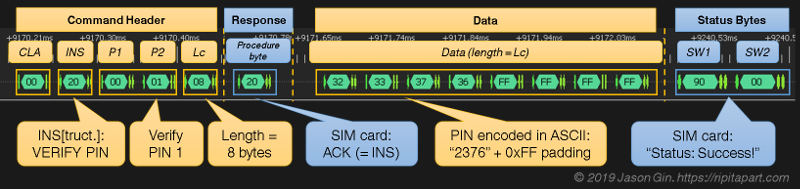
After multiple rounds of printing and tweaking, [polymatt] had a case good enough to reassemble the Libretto. Unfortunately, the previous owner left an unwanted gift: a BIOS password. Disconnecting the CMOS battery didn’t reset it, but a little research told him that shorting a few pins on the parallel port on the machine’s dock should do the trick. It was a bit involved, requiring the design and subsequent bodging of a PCB to fit into the docking port connector, but in the end he was able to wake up a machine to all its Windows 95 glory. Better get patching.
In a time when laptops were more like lap-crushers, the Libretto was an amazing little machine, and thirty years on, they’re well worth saving from the scrap heap. Hats off to [polymatt] for the effort to save this beauty, and if he needs tips on reading data from any PCMCIA cards that may have come with it, we’ve got him covered.
Continue reading “Tiny Laptop Gets A New Case And An Unlocking”