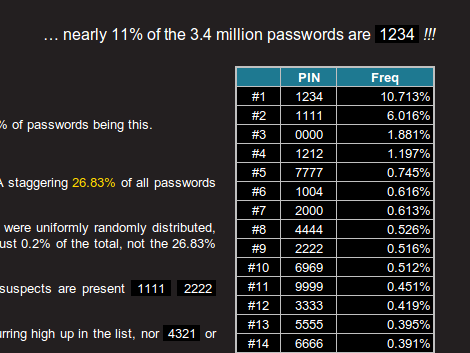
If we wanted to take a look at the statistics behind 4-digit pin numbers how could we do such a thing? After all, it’s not like people are just going to tell you the code they like to use. It turns out the databases of leaked passwords that have been floating around the Internet are the perfect source for a little study like this one. One such source was filtered for passwords that were exactly four digits long and contained only numbers. The result was a set of 3.4 million PIN numbers which were analysed for statistical patterns.
As the cliché movie joke tells us, 1234 is by far the most commonly used PIN to tune of 10% (*facepalm*). That’s followed relatively closely by 1111. But if plain old frequency were as deep as this look went it would make for boring reading. You’ll want to keep going with this article, which then looks into issues like ease of entry; 2580 is straight down the center of a telephone keypad. Dates are also very common, which greatly limits what the first and last pair of the PIN combination might be.
We’ll leave you with this nugget: Over 25% of all PINs are made of just 20 different number (at least from this data set).
[Thanks Awjlogan]