We stumbled upon a story this week that really raised our eyebrows and made us wonder if we were missing something. The gist of the story is that U.S. Secretary of Energy Chris Wright, who has degrees in both electrical and mechanical engineering, has floated the idea of using the nation’s fleet of emergency backup generators to reduce the need to build the dozens of new power plants needed to fuel the AI data center building binge. The full story looks to be a Bloomberg exclusive and thus behind a paywall — hey, you don’t get to be a centibillionaire by giving stuff away, you know — so we might be missing some vital details, but this sounds pretty stupid to us.
Supercon75 Articles
2025 Hackaday Supercon: Two New Workshops, Costume Party, Lightning Talks, And A New-Space Panel
So much news, so little time left until Supercon! We hope you all have your tickets. If not: Workshop and general admission tickets are on sale now. We’re getting down to the last slightly-more-than-two-handfuls, so if you’re thinking of coming, the time for procrastination has passed.
First up, we have two late-addition workshops, and tickets were just made available. Maybe you noticed that Arduino was bought by Qualcomm, and they kicked off the union with a brand-new board? You can get yourself one, and learn how to use it. And not to be outdone, the CEO of Framework, makers of modular laptop computers, is coming with a grab-bag of parts for you to play with.
Leonardo Cavagnis & Tyler Wojciechowicz
Arduino x DigiKey Presents – From Blink to Think: Discover Arduino Uno Q
Explore the power of Arduino Uno Q, the new board combining a microcontroller and a microprocessor. In this hands-on workshop, you’ll learn how to get started with Uno Q and unlock its dual-core capabilities for intelligent and connected projects.
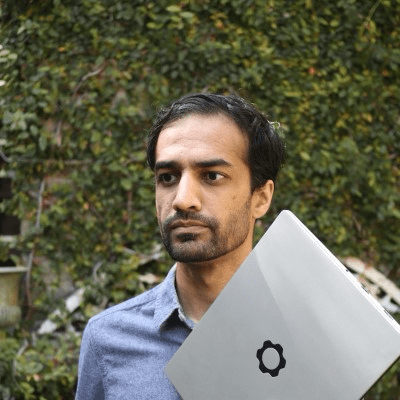
Framework Mystery Boxes: Swap & Build
This workshop is hosted by Framework’s Founder and CEO, Nirav Patel. You’ll receive a box of assorted returned/refurbished Framework Laptop parts at the start of the workshop. You can then trade parts with other attendees and work together to try to build a functioning computer of some kind. You’ll pick up some tips and tricks on debugging and repair along the way.
Last Chance: 2025 Hackaday Supercon Still Wants You!
Good news, procrastinators! Today was going to be the last day to throw your hat in the ring for a slot to talk at Supercon in November, but we’re extending the deadline one more week, until July 10th. We have an almost full schedule, but we’re still missing your talk.
So if the thought of having missed the deadline fills you with regret, here’s your second chance. We have spots for both 40-minute and 20-minute talks still open. We love to have a mix of newcomers as well as longtime Hackaday friends, so don’t be shy.
Supercon is a super fun time, and the crowd is full of energy and excitement for projects of all kinds. There is no better audience to present your feats of hardware derring-do, stories of reverse engineering, or other plans for world domination. Where else will you find such a density of like-minded hackers?
Don’t delay, get your talk proposal in today.
Hackaday Supercon 2025 Call For Participation: We Want You!
We’re tremendously excited to be able to announce that the Hackaday Supercon is on for 2025, and will be taking place October 31st through November 2nd in Pasadena, California.
Supercon is about bringing the Hackaday community together to share our great ideas, big and small. So get to brainstorming, because we’d like to hear what you’ve been up to! Like last year, we’ll be featuring both longer and shorter talks, and hope to get a great mix of both first-time presenters and Hackaday luminaries. If you know someone you think should give a talk, point them here.
The Call for Participation form is online now, and you’ve got until July 3rd 10th to get yourself signed up.
Honestly, just the people that Supercon brings together is reason enough to attend, but then you throw in the talks, the badge-hacking, the food, and the miscellaneous shenanigans … it’s an event you really don’t want to miss. And as always, presenters get in for free, get their moment in the sun, and get warm vibes from the Hackaday audience. Get yourself signed up now!
We’ll have more news forthcoming in the next few weeks, including the start of ticket sales, so be sure to keep your eyes on Hackaday.
Hackaday Europe 2025 Tickets On Sale, And CFP Extended Until Friday
We’re opening up shop for Hackaday Europe, so get your tickets now! We’ve managed to get the ticket price down a bit this year, so you can join in all the fun for $145. And if you’re reading this right now, snap up one of the $75 early bird tickets as fast as you can.
Hackaday Europe is going down again in Berlin this year, on March 15th and 16th at MotionLab. It’s going to be a day and a half of presentations, lightning talks, badge hacking, workshops, and more. This is where Hackaday hangs out in person, and it’s honestly just a great time – if your idea of a great time is trading favorite PCB design tricks, crafting crufty code, and generally trading tales of hardware derring-do.
In short, it’s the best of Hackaday, live and in person. Throughout the weekend, all the meals are catered, we’ve got live music at night, and the soldering irons will be warmed up for you. It’s going to be great!
If you’re in town on Friday the 14th, we’ll be meeting up in the evening to get together over some pre-event food and drink, sponsored by Crowd Supply. It’s a nice opportunity to break the ice, get to know the people you’re going to be spending the next 48 hours with, and just mingle without missing that great talk or wonderful workshop. Continue reading “Hackaday Europe 2025 Tickets On Sale, And CFP Extended Until Friday”
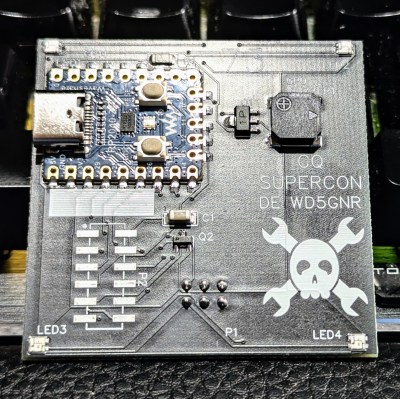
An SAO For Hams
Generally speaking, the Hackaday Supercon badge will always have a place for SAO (rebranded as “Supercon add-ons”), and that makes sense. We did originate them, after all. This year, though, we’ve gone all in on SAO, and, in particular, we’ve asked to see more SAOs with communication capabilities. The standard has always had an I2C bus, but few people use them. I decided I wanted to set an example and cook up a badge for Supercon. Was it hard? Yes and no. I’ll share with you a little about the board’s genesis and the issues I found. At the end, I’ll make you a special offer, if you are going to Supercon.
The Idea
I’ve been a ham radio operator for a very long time. In fact, July was my 47th anniversary in the radio hobby. Well, that’s not true. It was my 47th year with a license. I had been listening to shortwave long before then. So, I wanted to do something with Morse code. You don’t have to know Morse code to get a license these days, but a lot of hams enjoy it.
I set out to do a simple board that would play some Morse code messages. But that’s just another blinking light LED with a buzzer on it, too. So, naturally, I decided it would also provide Morse code output for the I2C host. That is, the SAO could be used to convert ASCII to Morse code. Sounds simple, right? Sure.
Getting Started
I wanted to use a Raspberry Pi Pico but didn’t want to violate the SAO size requirements. Luckily, there’s an RP2040-Zero module that is quite tiny and looks more or less like a normal Pico. The two big differences are plusses: they have a reset button, and instead of a normal LED, they have a WS2812b-style LED.
Breaking News: 2024 Supercon SAO Contest Deadline Extended
More than a couple folks have written us saying that their entries into the Supercon Add-On Contest got caught up in the Chinese fall holidays. Add to that our tendency to wait until the last minute, and there still more projects out there that we’d like to see. So we’re extending the deadline one more week, until October 22nd.

If you’re just tuning in now, well, you’ve got some catching up to do. Supercon Add-Ons are another step forward in the tradition of renaming the original SAO. One of our favorite resources on the subject comes from prolific SAO designer [Twinkle Twinkie], and you can even download PCB footprints over there on Hackaday.io.
Don’t know why you want to make an SAO? Even if you’re not coming to Supercon this year? Well, our own [Tom Nardi] describes it as a low barrier to entry, full-stack hardware design and production tutorial. Plus, you’ll have something to trade with like-minded hardware nerds at the next con you attend.
We’ve already seen some killer artistic entries, but we want to see yours! We know the time’s tight, but you can still get in a last minute board run if you get started today. And those of you who are sitting at home waiting for boards to arrive, wipe that sweat from your brow. We’ll catch up with you next Tuesday!