Audacity is an extremely popular open source audio editor, with hundreds of millions of downloads on the books. But due to some controversy over changes the Muse Group wanted to implement when they took ownership of the project back in 2021, the userbase has fractured somewhat. Some users simply stick with an older version of the program, while others have switched over to one of the forks that have popped up in the last couple of years.
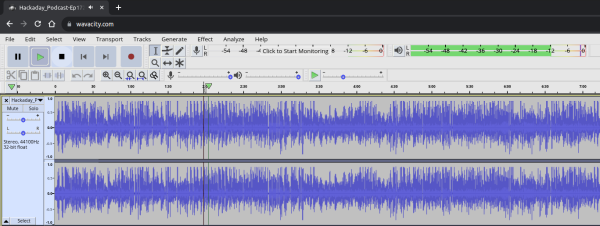
The Wavacity project by [Adam Hilss] is a bit of both. It looks and feels just like an older version of Audacity (specifically, 3.0.0). But the trick here is that he’s managed to get it working with WebAssembly (WASM) so you can run it in your browser. Impressively, it even works on mobile devices. Though the Audacity UI, which already carries the sort of baggage you’d expect from a program that’s more than 20 years old, is hardly suited to a touch screen. Continue reading “Audacity Runs Surprisingly Well In Your Browser”