Even though the very concept of an ‘unpickable lock’ is as plausible as making water not be wet, this doesn’t take away from the intellectual thrill of devising solutions to picking attacks and subsequently circumventing those solutions. Case in point the ‘unpickable’ traveling key lock that [Works by Design] recently featured and sent a few copies off to lock pickers such as [Lock Noob] who gave picking it a shake.
Many of the details and reasoning behind [Works by Design]’s lock design can be found in the original video, with [Lock Noob] going over the basic summary before getting to work trying to pick it.
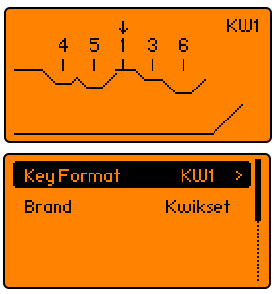
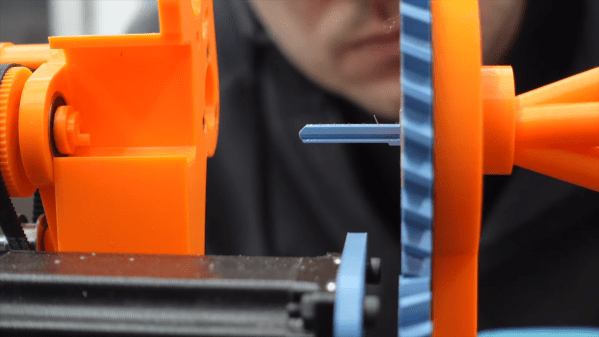
Rather than trying to bump the tumbler lock mechanism or another indirect approach, the focus is here on an impressioning attack. Although in this traveling key mechanism the physical key is moved inside the lock, the pins of the tumbler lock will leave impressions on the brass blanks when the lock is gently forced to rotate, indicating that there’s still too much material there.
The approach here is thus to slowly file away these sections, with interestingly the plastic pin that [Works by Design] had added to dodge impressioning attacks not being too much of an issue. Thus after over an hour of turning-filing-turning-filing ad nauseam, the lock mechanism rotated, confirming that it had been defeated.
In the subsequent teardown of the lock it can be seen that a plastic pin is indeed rather fragile, with part of its top having been torn off. After replacing this damaged plastic pin with a fresh one, a foil-based impressioning attack is attempted by putting aluminium foil over a skeleton key, but this didn’t quite work out as the pins come in sideways and thus do not leave a useful impression.
Theoretically the pins would press down onto the soft foil, creating an almost immediate impression of the required key. Perhaps that leaving a solid side on the blank would make it work, but this is an approach that would have to be refined.
Either way, it shows that ‘unpickable’ depends on your definition, as ‘1+ hour of filing with knowledge of bitting depths’ would be considered ‘unpickable’ by some. At least it’s not as dramatic as a 2020 [Stuff Made Here] ‘unpickable lock’ hack that we covered, before it got shredded by the [LockPickingLawyer] with resulting list of potential fixes of multiple easy exploits before even having to resort to impressioning.
Considering that traveling key designs generally require at least a tedious impressioning attack, with potential ways to address this in a more substantial way, a redesign featuring these changes would be rather interesting to see picked. If it can defeat the average lockpicking enthusiast including those practicing the legal profession, it’s probably as close to ‘unpickable’ as can be before the bolt cutters and angle grinders are used against any vulnerable parts that aren’t the lock itself.
Continue reading “Defeating The [Works By Design]’s Unpickable Lock”