
I probably won’t be replacing my giant G-shock watch just yet, but this binary POV watch is pretty sweet. Sure, the POV clock is old hat by now, but it’s also a nice example of adding a Li-ionbattery to an embedded project. It uses a MAX1555 li-ion charger and throws caution to the wind and doesn’t bother with any external capacitors. Battery life is several days or several hours if the watch is put into flashlight mode.
Month: February 2008
Cheap DIY Acoustic Guitar Pickup

I stumbled on this simple, but effective and cheap diy guitar pickup in my rounds for interesting hacks. Piezo elements haven’t failed to amaze me. They’re usable for electronic drum kit, underwater microphones, running shoes and musical greeting cards.
(I’ve only found an old, out of print book on hydrophones, so if you’ve got a good reference, send it in.)
HackIt: Better Project Documentation

Today’s hackit is devoted to everyone who enjoys a good project write-up. I’m on the verge of upgrading my photo gear (Digital Rebel XTi) with some new lighting and a better lens to improve my work and found myself wondering what the community likes to see in a good how-to. What can be done to make them better for the community. Decent photography? Better parts lists? I prefer good photos and reproducible work.
So, got a better idea? Lets hear it.
SitesCollide Podcast

Internal Bluetooth For 5th Gen IPods
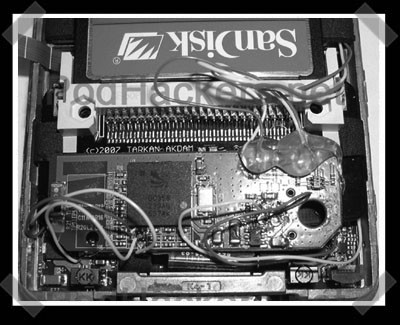
[Ed] sent in his latest iPod modding effort. Previously he did this on a 4th gen, and now he’s following that up with a 5th gen version. He found an even smaller bluetooth module for the mod, but it requires replacing the hard drive with a compact flash card to make room inside the case if you want to keep the original back cover.
Breaking Disk Encryption With RAM Dumps
If you haven’t gotten a chance yet, do watch the video of this attack. It’s does a good job explaining the problem. Full drive encryption stores the key in RAM while the computer is powered on. The RAM’s stored data doesn’t immediately disappear when powered off, but fades over time. To recover the keys, they powered off the computer and booted from a USB disk that created an image of the RAM. You can read more about the attack here.
How can you reduce this threat? You can turn off USB booting and then put a password on the BIOS to prevent the specific activity shown in the video. Also, you can encrypt your rarely used data in a folder on the disk. They could still decrypt the disk, but they won’t get everything. I don’t think this problem will truly be fixed unless there is a fundamental change in hardware design to erase the RAM and even then it would probably only help computers that are powered off, not suspended.
The potential for this attack has always been talked about and I’m glad to see someone pull it off. I’m hoping to see future research into dumping RAM data using a USB/ExpressCard with DMA access.
Tin Hat Bonus: Jetlag Got Me.
Update: Sorry guys. I hadn’t seen it before, but apparently this dell keylogger junk is a rather delicious hoax. To keep from confusing the RSS readers, I’m leaving a post stub up. If I wasn’t travel-beaten I would have paid attention to the fact that the supposed keylogger wasn’t on a flexible flat cable. I pulled the image since it was originally stolen.
It’s probably totally BS, but supposedly this guy found what seems to be a keylogger inside his new dell 600m laptop. He submitted a FOIA request to the DHS, only to have his request denied. It’s a bit tin-hat, but the idea that a three letter agency might be adding extra hardware to your laptop is very disturbing indeed. I guess it’s time to start auditing any new hardware purchased for bonus parts. [via]











