
When I checked it out, only two teams had appeared for the cooling contest. The method of choice? Rubbing alcohol and dry ice. The dry ice cools the alcohol, but doesn’t freeze it. [Team Hebrew] was my favorite – they used a vinyl hose to carry the beer into the cooling liquid. They managed a 45 second run at one point, and used a simple electric blower to evacuate the beer from the cooling line. They found that it was a bit easier to just blow it out the old fashioned way.
Month: August 2007
Hack-A-Day Meetup (T-Shirts!) On Sunday

Yes. Free T-shirts. Free stickers. At Defcon 15. (No virtual begging.) We’ll have skybox 206 on sunday, but we’re only planning to be set up around noon for an hour or so. Come get em.
The swag is free, but we’d like it if you’d toss us a buck or two to donate to the EFF.
Mod Chip Crackdown In The US.
I got quite a few emails about this, but didn’t have a chance to check it out until now. It seems that the feds have been raiding various mod shops and individuals who’ve been doing mods for others. I’m a fan of open, moddable and repairable hardware, so this is sad news to me. There’s a first hand account from one of the raided individuals along with a decent commentary on the issue sent in by [xantium].
This might sound a bit strange, but take the time to let your congress critter know what you think about this issue. Don’t expect them to understand the technical background, but letting them know that you’re unhappy with the execution of the DMCA and that labeling legitimate uses for mod-chip technology as illegal is the equivalent to outlawing home car repair might make a difference.
The Defcon Badge

I made it over to pre-registration earlier and scored my badge. It’s a pretty interesting piece of work by [kingpin]. It’s got 95 SMD leds forming a matrix display. The top and bottom icons on the badge are touch sensitive buttons. It’s got selectable modes, programmable text scrolling, a pre-set POV mode and adjustable scrolling speed.
Update: I started digging through the CD they’re handing out at registration and found the schematics, BOM, layout, everything. I’ll have it posted as soon as it finishes uploading over my evdo connection. The board has provisions for wireless, 3 axis accelerometer, serial interface and it’s using a Freescale QF16 processor. (I tried looking up the chip number earlier, but utterly failed)
Update 2: I’m putting interesting defcon files up here. All the badge info I have is online. I noticed a confidentiality notice on one of the files, I’m assuming that it’s ok to distribute since they’re distributing this freely on the conference CD. If I hear otherwise, I’ll have to pull it.
Black Hat 2007 Other Wireless

Luis Miras presented “Other Wireless: New ways of being Pwned”. Instead of common con topics like Bluetooth or WiFi, this dealt with the cheap radios used in wireless keyboards, mice, and things like the wireless remote pictured above. These RX/TX pairs are found in 27MHz, 900MHz, and 2.4GHz versions. The devices all use the same main components: a microcontroller, an EEPROM for storing the serial number, and the transmitter. The dongle is nearly the same only with a receiver.
Black Hat 2007 Premature AJAX-ulation

Billy Hoffman and Bryan Sullivan from SPI Dynamics gave one of the more entertaining talks today. The title is an allusion to peoples willingness to apply new technology before they fully understand it. Instead of laughing at silly web 2.0 developers they decided to build their own AJAXified website by consulting the resources that any programmer would: AJAX books, blogs, and forums. What they ended up with was hackervactations.com… a security hole riddled gem built on good intentions.
Black Hat 2007 No-Tech Hacking With Johnny Long
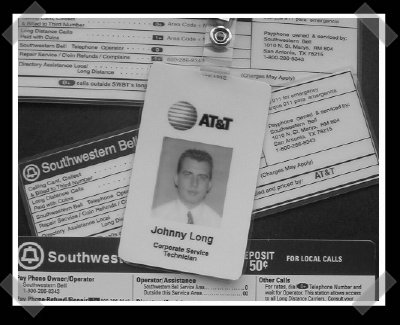
[J0hnny]’s at Blackhat and Defcon this year with his talk on “No-Tech Hacking”. It’s a fun talk that boils down to this: loads of information can be gathered using low tech methods. A small digital (or film) camera is ideal for shoulder surfing, identifying weaknesses, and assessing strengths.
The talk is pretty amusing – the commentary on the example shots is priceless. The concept has gone over so well at the cons that [J0hnny] has contributed a chapter to a book on risk management. You can grab a sample chapter here. It looks like he’ll be running his talk at 8pm on Friday at Defcon. From the sample chapter, I’d say that the book should be pretty good. It looks like a good introduction to social engineering and using your wits to defeat obstacles (like corporate security).










