[CNLohr] needs no introduction around these parts. He’s pulled off a few really epic hacks. Recently, he’s set his sights on writing a simple, easy to extend library to work with the HTC Vive VR controller equipment, and in particular the Watchman controller.
There’s been a lot of previous work on the device, so [Charles] wasn’t starting from scratch, and he live-streamed his work, allowing others to play along. In the process, two engineers who actually worked on the hardware in question, [Alan Yates] and [Ben Jackson], stopped by and gave some oblique hints and “warmer-cooler” guidance. A much-condensed version is up on YouTube (and embedded below). In the links, you’ll find code and the live streams in their original glory, if you want to see what went down blow by blow. Code and more docs are in this Gist.
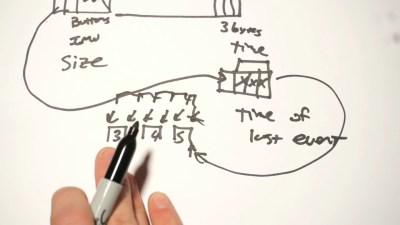 In the end, it all ended up being a lot of hard work because the Watchman controller needs to send its orientation and accelerometer data wirelessly, and this means compressing a lot of data down into a tiny trickle. All possible tricks were used, including variable-length fields where one bit indicates whether the next byte still belongs to this sample or the next, and packing the data into a frame from both ends. We see why figuring out the protocol drove [Charles] nuts! His dissection begins ten minutes into the summary video.
In the end, it all ended up being a lot of hard work because the Watchman controller needs to send its orientation and accelerometer data wirelessly, and this means compressing a lot of data down into a tiny trickle. All possible tricks were used, including variable-length fields where one bit indicates whether the next byte still belongs to this sample or the next, and packing the data into a frame from both ends. We see why figuring out the protocol drove [Charles] nuts! His dissection begins ten minutes into the summary video.
Besides the hints, the community involvement, and sheer persistence, [Charles] was also helped by being able to generate his own data. Instead of relying on the placement of the device in space, an AVR blinked IR LEDs into the controller to generate known timing deltas. Remember this general technique if you’re reverse engineering anything.
We think the Vive is very cool, and we’ve covered hacks into it before. From [Trammell Hudson]’s early hacks to this recent jaw-dropping drone orientation demo, hackers have been figuring out how to use the Lighthouses on their own. Now [CNLohr] (and the community) have decoded one of the last remaining parts of the OEM hardware. Woot!















Great video, I always find it fascinating looking at how protocols overcome practical limitations of the systems they are running on. I wonder how extensible the protocol will be in the future.
I promise I’ll watch the video later. Right now I’m just drooling about all the empty space behind him in that header picture. I wish I had that!
===Jac
I can’t wait to find the time to eventually watch this. The maddeningly frustrating warmer-colder hints promise to be hilarious.
That face when he finds out someone who helped with the firmware is in the chat.
The ears of someone who got blasted on headphones, when that ‘helping someone’ blew cnlohr’s mind with bidirectional coding.
Blizzard file format for replays actually stores integers in a similar or I think identical way. It’s a great way of compression considering so many different integers fields or unknown size are stored in a replay. The file formats in there actually use bitpacked streams, for even more craziness.
Search github for heroprotocol from the Blizzard guys, and look in decoders.py for function _vint:
Or the URL if allowed here: https://github.com/Blizzard/heroprotocol/blob/master/decoders.py#L195
Variable-length integer coding pops up all sorts of places. Some other places are string encoding (UTF-8) and many of the fields in an EBML (Matroska/WebM) file. In the latter case tag IDs, field lengths and the contents themselves (for integer payloads) are all packed in this way.
I’d love to see a build using the technology behind one of those controllers! (has anyone more details about them?)
Did you check the links at the bottom of the story for starts? Or http://hackaday.com/tag/htc-vive/?
That said, I would bet that we’re just at the beginning of a few years’ worth of seeing sweet Vive hacks. Woot!
I’ve been wanting to get a Vive or Rift for as long as they have been in development. Knowing the companies behind it support community hacks/development could really swing me towards the Vive, even though I would more than likely only care about the display portion of the system (I am sans left foot and the right side doesn’t get around like it used to after a car wreck, so I’m not going to be jumping around my cluttered lack of space with a couple hands in controllers rather than holding my cane), making the Rift a cheaper alternative.
I’m willing to pay extra, though, if I know that there is support for community improvements. Actually, many of the games Valve creates have good support for community mods, and this has worked out well for them in the past. Community mods for their games have extended their games’ lifetimes long past what it would have been otherwise.
https://www.youtube.com/watch?v=dVXpHKktbzM