Wi-Fi cameras are everywhere these days, with wireless networking making surveillance systems easier to deploy than ever. [CiferTech] has been recently developing the RF Clown—a tool that can block transmissions from these cameras at some range.
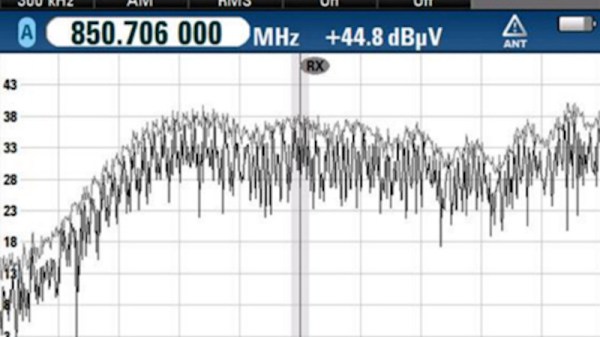
The build is based around an ESP32, with three tactile switches and an OLED display for the user interface. The microcontroller is hooked up to a trio of GT—24 Mini radio modules, which feed a bank of antennas on top of the device. Depending on the mode the device is set to, it will command these modules to jam Bluetooth, BLE, or Wi-Fi traffic in the area with relatively crude transmissions.
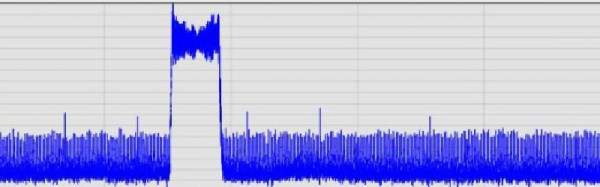
The use of multiple radio modules isn’t particularly sophisticated—it just makes it easier to put out more signal on more bands at the same time, flooding the zone and making it less likely legitimate transmissions will get through. Specifically, [CiferTech] demonstrates the use case of taking out a Wi-Fi camera—with the device switched on, the video feed freezes because packets from the camera simply stop making it through.
It’s perhaps impolite to interfere with the operation of somebody else’s cameras, so keep that in mind before you pursue a project like this one. Files are on GitHub for the curious. Video after the break.
Continue reading “Simple Device Can Freeze Wi-Fi Camera Feeds”