Two months after its surprise reveal at the 2019 East Coast RepRap Festival, the Prusa Mini has started shipping out to the first wave of early adopters. True to form, with the hardware now officially released to the public, the company has begun the process of releasing the design as open source. In their GitHub repository, owners can already find the KiCad files for the new “Buddy” control board and STLs for the machine’s printable parts.
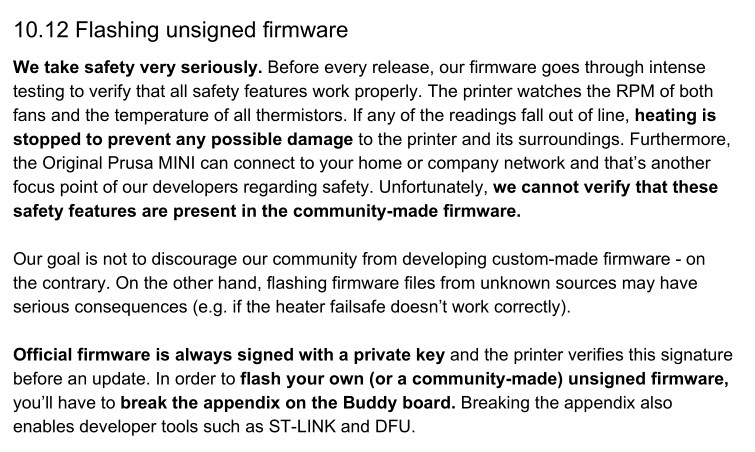
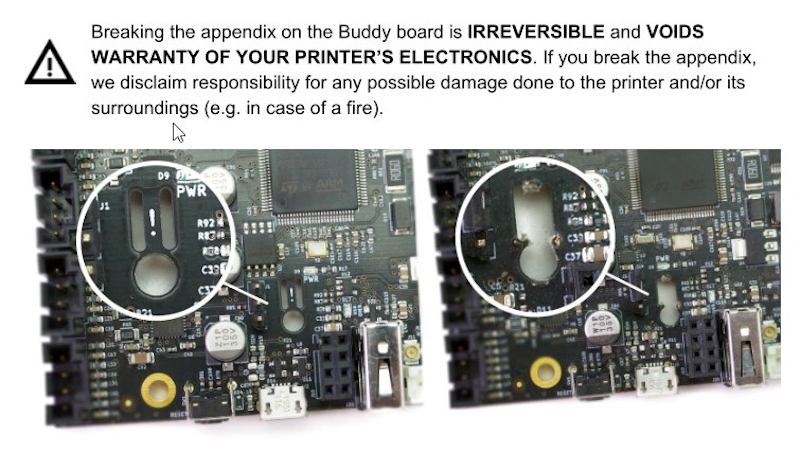
But even so, not everyone feels that Prusa Research has made the Mini as “open” as its predecessors. Some concerned owners have pointed out that according to the documentation for the Buddy board, they’ll need to physically snap off a section of the PCB so they can flash custom firmware images via Device Firmware Upgrade (DFU) mode. Once this piece of the board has been broken off, which the documentation refers to as the Appendix, Prusa Research will no longer honor any warranty claims for the electronic components of the printer.
 For the hardcore tinkerers out there, this news may come as something of a shock. Previous Prusa printers have enjoyed a fairly active firmware development community, and indeed, features that started out as user-developed modifications eventually made their way into the official upstream firmware. What’s more, certain hardware modifications require firmware tweaks to complete.
For the hardcore tinkerers out there, this news may come as something of a shock. Previous Prusa printers have enjoyed a fairly active firmware development community, and indeed, features that started out as user-developed modifications eventually made their way into the official upstream firmware. What’s more, certain hardware modifications require firmware tweaks to complete.
Prusa Research explains their stance by saying that there’s no way the company can verify the safety of community developed firmware builds. If thermal runaway protections have been disabled or otherwise compromised, the results could be disastrous. We’ve already seen it happen with other printers, so it’s hard to fault them for being cautious here. The company is also quick to point out that the installation of an unofficial firmware has always invalidated the printer’s warranty; physically breaking the board on the Mini is simply meant as a way to ensure the user understands they’re about to leave the beaten path.
How much support is a manufacturer obligated to provide to a user who’s modified their hardware? It’s of course an issue we’ve covered many times before. But here the situation is rather unique, as the user is being told they have to literally break a piece off of their device to unlock certain advanced functionality. If Prusa wanted to prevent users from running alternate firmware entirely they could have done so (or at least tried to), but instead they’ve created a scenario that forces the prospective tinkerer to either back down or fully commit.
So how did Prusa integrate this unusual feature into their brand new 32-bit control board? Perhaps more importantly, how is this going to impact those who want to hack their printers? Let’s find out.
A Tale of Two Grounds
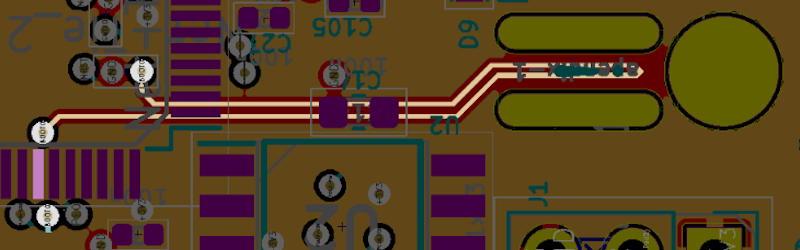
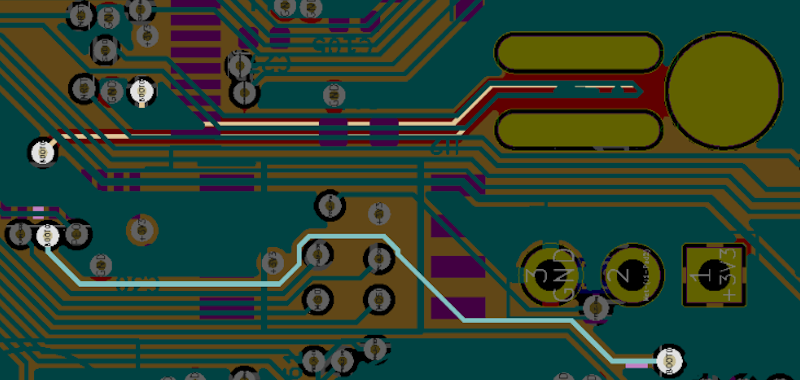
Looking at pictures of the assembled Buddy board, it’s not immediately obvious how the so-called Appendix works. It’s just a small piece of the PCB with no components on either side, there aren’t even any obvious traces running through it. But with a quick look at those aforementioned KiCad design files, we can put the pieces together.
As we can see, there’s a trace on one of the internal copper layers that loops through the Appendix. One side is connected to ground, and the other to the BOOT0 pin on the STM32F407VGT6 MCU. Consulting the datasheet for the chip, we can see that holding BOOT0 low like this disables DFU mode. So that explains why it has to go.
But the documentation says that to enable DFU mode you need to bring the BOOT0 pin high, and breaking the Appendix only leaves it floating. That’s where the second trace comes in. This one runs from BOOT0 to the center pin of a nearby three pin header. With pins for ground and 3.3 V on either side, a jumper can be used to switch BOOT0 between low and high. The Appendix is essentially a “safety” that prevents this jumper from having any effect.
The attentive reader may be wondering what would happen if you moved the jumper over to 3.3 V with the Appendix intact. It looks like Prusa considered this possibility, as the circuit diagram actually shows a 4.7K resistor between the header and BOOT0 pin to avoid a dead short.
Prusa Developer Program
While we’re certainly approaching the point where the average 3D printer owner is no different than the sort of person who owns a drill press or a table saw, a good chunk of them still spend as much time tweaking and modifying their machine as they do actually printing with it. So it’s little surprise that the possibility of firmware hacking being off the table has lead to some backlash.
But if there’s anyone who understands the desire to hack, modify, and improve 3D printers, it’s Josef Průša. The very real dangers of unchecked firmware modification forced him to act, as much to protect his customers as his brand, but he’s made it clear that the intent was never to block the more technically inclined users from getting their hands dirty.
In a recent blog post, Josef explained the company’s plan to introduce a “Developer Program” that is aimed specifically at those who want to get involved in unofficial firmware development:
Also, we plan to launch a community developer program in the upcoming months. You’ll get extra resources from us and in case you break something during development, you will get new parts (no matter whether you broke the “appendix” on the mainboard). We’ll publish more information soon, so stay tuned!
Such a program sounds like it would address essentially all of the concerns currently being voiced by users, though undoubtedly some will resent needing to register themselves as “developers” if all they want to do is modify a few lines of code in their printer’s firmware. It’s also unclear if a cost will be associated with this program, but it’s somewhat difficult to believe that the company will completely foot the bill for expanded customer support and access to replacement parts.
The End-Hacker License Agreement
Hacker-friendly companies like Prusa Research are in a difficult position. On one hand, they don’t want to do anything that prevents more technical users from modifying their products. But at the same time, it’s unreasonable to expect a manufacturer to replace hardware that was damaged while the user was performing unsanctioned modifications. As hackers, we need to acknowledge that there’s a certain level of personal responsibility that comes with the territory.
At the end of the day, the introduction of the Appendix should be seen as a net positive for the hacking community. It provides a clear line in the sand for anyone who wants to explore their hardware, and ensures both parties clearly understand the paradigm shift that happens when the user decides to take matters into their own hands. The fact that it even exists shows the hardware was not designed to restrict the user’s rights, but rather to acknowledge and respect them.
With any luck, the next time a manufacturer does something like this they’ll put “REMOVE BEFORE HACK” right on the silkscreen.















I don’t understand the uproar, this is a warranty and safety issue, not an open source problem.
YUP, i wonder if they ever plan to reach some sort of UL type of certification.
The certification labs don’t just trust the word of the manufacturer. They are old fashion EE types that look at design for weakness and intentionally break things to see if a failure could cause a fire.
Good luck getting UL certified using firmware as protection device. :P There are UL recognized protection devices that could have been used.
“Good luck getting UL certified using firmware as protection device.”
This is actually possible, but certification of software is so damn nasty it’s never done if it can be avoided. Have fun updating your firmware. Oh, it’s claimed as a safety feature, and now you are going to modify it? Oh no. Not so fast.
We have encountered this exact thing at my work place. We could use a motor driver to detect a fault condition, but that would make it a safety device, and therefore we would not be able to develop the firmware with the freedom we currently do. We implemented other safety sensors instead.
I agree, totally normal for a company and in fact pretty clever I believe
And a clear FTC warranty violation. It’s no different than the warranty void stickers, illegal.
breaking off the appendix isn’t what they say puts your warranty at risk, it’s running your own firmware. so if push came to shove and you sent them back a board with the rom mysteriously fried, they might just placate you with a board .. while quietly beefing up firmware testing options they provide to the customer, be those another hw revision, or just sw. no?
The problem is he can’t just void the warranty because the uploaded different firmware. The uploaded firmware actually has to lead to damage. It’s exactly why the FTC sent letters to Sony and Microsoft about Warranty Void If Removed Stickers. The removal of the sticker didn’t lead to damage, the person actually has to do damage attempting to open it or after opening it. This is not legal in the US. A better example is the FTC ruling on Apple jailbreaking not violating warranty. https://www.vice.com/en_us/article/yp3nax/jailbreaking-iphone-rooting-android-does-not-void-warranty
Does it matter though? You are not buying it from a USA vendor. You are purchasing it from a foreign country that is shipping it to the USA.
Argh, mods, I accidentally hover-cliked ‘report post’ on this, please don’t ding him for it!
No worries. We’re good.
Agreed. I don’t understand what the whining is about. I am totally with Prusa on this. Nicely done.
I agree. Drives home the “you flash this and it breaks, it’s your fault” point. I expect there are some out there they don’t like it because it forces them into being responsible for their own actions. Most normal hackers will understand they are on their own and take killing the printer as a learning exercise. Unfortunately there are some think that they can do no wrong.
It’s the same kind of debate which eventually led to the release of GPLv3 in favor of GPLv2. One of the major points of Open Source is hackability. A hardware lock prevents this, making the design less open.
Implementing safety mechanisms independent from the firmware would be a much better choice. Not only for more openness, but also for more safety. A hardware thermal fuse to avoid thermal runaways, for example.
It’s still open – you just have to opt in first.
If you look at it the *other* way around, this simply allows people who *don’t* modify their firmware to certify that fact.
Openness isn’t an on/off thing, there are levels of openness. Hardware prevention of updates reduces this level. This board with its firmware no longer qualifies for GPLv3, it’s now GPLv2, only.
At least here in the states you can’t copyright a piece of circuitry. Just cover process or application through patent. So GPL anything would be moot.
Copyright is for.. well.. copy.
“This board with its firmware no longer qualifies for GPLv3, it’s now GPLv2, only.”
Nope. It’s both. Just have to break the tab, to get GPLv3 openness. Nothing is hidden, no proprietary things, it’s all open. The hardware lock is even completely open. I don’t see what you are trying to imply. It’s open. As in: completely.
Only if you don’t have hands, legs and teeth, is it closed. Because then you wouldn’t be able to break the tab.
On second thought, maybe the tab could even be broken with an arse if it’s tight enough… :P
(I’m making a joke, not offense.)
Except there is no prevention. You just have to break the appendix and off you go. And it’s even in the official documentation for the device.
The sole purpose of the appendix is to be able to see that this printer has been running an unofficial firmware, therefore voiding any warranty claims.
Even on a commodity PC one can install open source software without cutting the hardware and without voiding warranty. Same for many routers. Now guess what’s more open.
The GPLv3 says you have to give the user a way to install their modified software. The way is “break this tab, then get out your firmware flashing tool, then …” No violation.
@Traumflug:
Yes, but a commodity PC won’t catch fire and burn your house down if you install different software. And there is also no warranty/support for that piece of software. Apples and pears.
Here’s some reading for you https://www.vice.com/en_us/article/yp3nax/jailbreaking-iphone-rooting-android-does-not-void-warranty
> a commodity PC won’t catch fire and burn
> your house down if you install different
> software. And there is also no warranty/
> support for that piece of software. Apples
> and pears.
Yes, apples and pears, like those who understand how technical stuff works and those who cheer on restrictions.
PCs don’t catch fire because their safety mechanisms don’t rely on the software running on it. Prusa’s new printer could implement such safety mechanisms, but deliberately doesn’t and prefers to lock down the firm-/software instead. And this on a product which trumpets the Open Source horn…
> At least here in the states you can’t
> copyright a piece of circuitry.
It’s not about the circuitry, it’s about the firmware. Looking at
https://github.com/prusa3d/Prusa-Firmware
it claims to be GPLv3, but actually no longer is when delivered with this circuitry board. Which obviously makes this board a GPL violation.
This doesn’t prevent hackability. In fact, it preserves it while also protecting the company.
Well in this case it doesn’t. It however makes the owner more responsible for that openness* than they’re traditionally use to.
*Freedom to pass their mistakes onto someone else.
“A hardware lock prevents this, making the design less open.”
A hardware lock does make a design less open. Black boxes and intentional lack of documentation makes designs less open.
* doesn’t
A hardware lock doesn’t make a design less open. Unless it is undocumented and meant to keep the design closed.
Absolutely and this is a great way to ensure that people are accepting responsibility for their actions. Prusa hasn’t made it impossible to put other firmware on it – rather quite an easy mod to do – but with the layers of lawyers out there laying in wait like snakes in the grass, if Prusa wants to stay in business, they have no choice but to do something like this. Fire risk comes with the chance someone can die from it and who can blame them for doing this to help take the heat off of them lest it come to that? I think this is a great way to draw the line in the sand. I would have absolutely no problem grinding out this spot in the board and accepting full responsibility for my actions.
Unfortunately, it’s also illegal. It’s the same as warranty void if removed stickers. They can’t void the warranty on all electronics. They are begging for a class action lawsuit.
if you break the fuel nozzle restrictor on your new car, you will void the warranty, with good reason. This is the exact same thing.
The difference is that there is no ‘option’ to defeat the fuel restriction nozzle. Give people an option and you may be legally encouraging it. I wonder if this is a failing on the maker’s part to understand American legal culture. He may have made his situation even more culpable.
There is most certainly an option, just do it. Do you need someone to tell you that you can do it? OK, you can do it. They do not prevent you from removing the restriction, you can just go in there wirh a big screwdriver and rip it out.
Do you understand American legal culture? Americans were the first to require safety standards for electrical devices. Americans are the ones who first decided that you should not be able to buy unsafe products that will burn down your house.
The FTC rules on warranty stickers is probably why. We have been fighting for the right to repair for years. They can’t justify voiding the warranty on all electronics. They are in clear violation (so is Sony, Microsoft, and Apple to be fair), they have to actually damage the electronics for the warranty to be void. Josef really should have looked at US warranty law if he wants to keep on everyone’s good graces. It’s the same reason Sony can’t void a PS4 just for you removing a sticker and looking around. The action has to actually lead to the damage.
The damage being a broken off part of a PCB.
You’re not as smart as you think you are. Moreso, you’re not smarter than Josef. My guess is, he went through all warranty laws before deciding how exactly to implement the appendix.
If someone decides to break off a piece of the PCB, causing physical damage to the PCB, the warranty will be void. And it’s all perfectly legal according to US warranty laws, since literally breaking the PCB does not fall under “normal home use”.
They are forcing you to break the part to update firmware. That’s not legal, in the US at least. https://www.vice.com/en_us/article/yp3nax/jailbreaking-iphone-rooting-android-does-not-void-warranty You definitely aren’t as smart as you think you are. Try actual research next time.
They are not FORCING you to break it in the course of normal use. You must CHOOSE to break it if you want to use it abnormally. The difference is important – the ability to flash custom firmware is not part of normal use of the product. This is the same as removing the seat belts from your car – you can do it, and you might even be fine, but the manufacturer wont have your back if you do.
> You’re not as smart as you think you are. Moreso, you’re not smarter than Josef. My guess is, he went through all warranty laws before deciding how exactly to implement the appendix.
Why are you so rude in the way you put this?
First of all, chances are you do not know Josef Prusa, and you don’t know that commenter either. It kind of damages your argument to be making judgements about their relative intelligence.
Second, Prusa Printers is a company that employs many people; so it’s kind of weird that you’re implying that this idea is something Josef Prusa personally came up with.
Third, while I agree with the idea that they’ve probably done a fair amount of due diligence to make sure that this would actually be enforceable, it’s not outside of the realm of possibility that even having done so they might actually be wrong. Much larger companies, ones big enough that they probably have lawyers on retainer in the country in question, can and have been mistaken (or in some cases, deliberately wrong) about this very issue. That’s why there had to be an FTC ruling stating that a sticker was not enough.
I agree with what you said though, this does seem designed specifically to be enough to void a warranty. It’s definitely not as “clear” as that commenter said. But it seems to be designed to meet to the letter of the law and not the spirit of the law. That’s what bothers me, even though I totally understand where they’re coming from, and I’ll freely admit that I don’t have a better idea.
you are confusing the “right” to a warranty (they don’t have to offer any explicit warranty, only the required implicit ones) with the right to repair.
And the unit _is_ damaged if you do this, it no longer possesses the ability to block firmware updates. This is a stated feature of the unit.
Dude, you account for over 10% of the comments on this post right now – stop spamming, we get your (incorrect) point!
Well, as someone who does not yet have a Prusa but has spent time modifying the two printers I do have to improve their performance, the biggest issue that I see is that its not just preventing you from flashing your own firmware, but preventing you from changing any of the precompiled settings at all. Think about things like calibrating e-steps, calibrating xyz, performing PID autotunes, things like that. All of those ususally require you to store the settings to EEPROM, or youll have to re-enter the values every time you turn your printer back on. This means if you ever upgrade your extruder or even just your hotend, youre going to have to find a work around to make sure your prints always use the correct settings. I feel like it might not have been that big of an issue if the tab only prevented you from flashing custom firmware and didnt prevent you from changing settings to the official firmware to suit your needs. Im not sure if that is possible, as I am not an expert on EEPROM and firmware and everything, but if it were possible, I feel like that should have been what they did
rather pointless when there is an SWD connector on the board ….
There’s 3 levels of protection, you can (and have to) go from level 1 to level 0 but it requires a mass erase, you’d lose whatever key that was in there, and I guess Prusa can check for that easily if the MCU still works. (simply check if it accepts an officially signed firmware, or they probably have a dedicated way to do it quickly already)
It’s hard to tell if there’s an exploit that allows you to read out the flash (and thus, read out the key) even though protection level 1 is on. The last time I did something like that, I had a custom Pebble watch face dump hex codes onto the screen and you had to video record the screen. This new PCB has some attack vectors like gcode files, the ethernet interface, and optional WiFi. Maybe they left an unbounded strcpy in there or something?
Wait a few months and the clones will be out with bootloader always available. Swap it out with a clone, start a fire, put the old board back in, return under warranty.
Or buy the OpenWRT equivalent of a 3D printer.
The question is: Do you want a tool or do you want another project that’s never going to be finished?
I can’t find the source code yet, but I imagine reading out the key won’t help you. (In fact they can include it in the source code when they publish it.) The private key that signs the official firmware downloads must be kept secret, but it is verified by the public key in the bootloader of the system. Maybe someone with more STM experience can fill in the details about the offiical ST way to do things but this is generally how these things work.
The official ST way to do these things is to publish an encrypted binary, download it while-encrypted to the embedded ST microcontroller and… These two use different keys. So they decrypt and re-encrypt it in the upgrader tool on the user’s PC. /that’s/ how ST does it….
I *may* have a ton of experience doing exactly this. STM’s protection doesn’t really protect the flash from executing code. If we know the VTOR address (which we would from the code), building a sketch to dump the bootloader to RAM is easy, and RAM is not protected by SWD, so the usual method I use is to memcpy the whole bootloader into ram and then enter an infinite loop so I can pick up the contents via SWD. At that point, mass erase and reprogram is easy.
If they use public-key encryption, then the key used to validate the digital signature is indeed public, but you don’t have the private key needed to sign your own firmware. So: knowing the full source code to the bootloader is not helpful by itself – knowing the public key is not a solution to anything, except maybe if the public key was generated using a bad random number source. The only other attack avenue left to bypass this is to look for bugs in the bootloader code that would allow you to bypass the check, or to use electrical disturbance injection to steer the microcontroller around the checks (perhaps combining some bug that by itself is insufficient to do the bypass, with a disturbance that leverages the bug).
I consider the whole PCB brouhaha to be unnecessary. All they need is to write into the one-time-programmable area and set their “software fuse” to enable booting unsigned firmware. Many MCUs have one-time programmable area that survives a mass erase.
+1 this.
The SWD wont allow access to Flash(0x0 or 0x800000) only ram(0x200000). There is a attack vector that allows you to step through the code(in turn reading it) but I cant disclose much on that. any changes to the Boot cycle always involves blanking the on-cpu flash and in turn deleting the code you want to view. If this is anything like the OBDII readers out there that use the read-back protection on stm chips then the key is not stored in the source/flash but written to another location of the system, there’s a routine you pipe data through and it comes out decrypted but only for internal use of the cpu/flash. for more info on the STM read back system then check our the stlink reverse engineering blog (was on here some time ago). If you can write code to the chip then yes you can read out the code but not the key. thats not to say there is not another attack vector that can read the key but by default the key is written not read.
I’am very new to stm so this conjecture is based on my experience in reverse engineering OBD readers & other stm devices for fun.
The Fraunhofer cold boot stepping hack?
There’s no problem with the bootloader being completely open source if public key cryptography is used: the knowledge of public key is only enough to validate the signature on the firmware, but not to sign your own. That’s iff they’d instead use some OTP area in the microcontroller (first choosing a microcontroller that has it): that way the “fuse” would need no board modification, and Prusa could always check if the OTP “fuse” was “blown”.
Alas, knowing life, I’m 100% sure that their bootloader or crypto implementation have an exploitable bug or two. Perhaps their PC-side infrastructure (the source of the private key, etc.) is butchered – e.g. if they don’t use a hardware module to do the signing, they’re SOL, as the private key will eventually leak. Nobody in this line of business gets it right the first time.
They have that covered as well. There is a second track on the appendix that grounds the SWDIO pin in the same way as the boot0 pin
If that’s the case then I’ll be curious how they programmed the chip. Did they do it before soldering the chip on the board?
If there’s an official update route, then likely they had the IC’s pre-programmed from the supplier (at least with their bootloader).
Has anyone posted a review of the Prusa mini yet? Given the history of producing decent printers, I’m guessing this one is going to be no exception, but it would still be nice to hear a few other opinions before pulling the trigger and ordering one.
Best review I can imagine is they Prusa is moving all their production line printers to Minis and phasing out the MK3. If they expect it to function well enough to be a production workhorse it should handle the average benchy hobbyist.
“he average benchy hobbyist.”
B^)
Neat. I always thought that dedicated BOOT0 pin was sort of annoying; it’s cool to see a use for it.
But one of my favorite improvements to the new STM32G0 line is still that they made it an “opt-in” feature on one of the pins. It’s amazing how often STM32 design troubleshooting boils down to asking, “how is the BOOT0 pin connected?”
The problem is that there are consumer protections in America which prevent nasty behavior like this. If I flash my firmware, and the ball-bearings go bad – Josef Prusa still has to honor his warranty and replace those bearings. If I flash the firmware and say – the heater _does_ malfunction, but then some other component on the board goes bad, like the ADC on the microcontroller, that’s garbage.
There’s no state in which you can put firmware that should damage components on the board. It’s a garbage excuse. Voiding the entire warranty for the machine like this is actually not legal in practice. At least in America.
Now, the way you _can_ damage a board, is by fiddling with it in the physical space. Inverted power input, wrong components, etc. Really the only thing that flashing firmware can do to these machines is keep the heater on when it shouldn’t be…and ram axis to their limits, which typically doesn’t harm anything. So why? Why disallow people from flashing the software? Why is that such an egregious offense that it requires voiding the warranty?
As a sweeping generalisation, people are stupid and dishonest.
Prior to this, some person that broke something could attempt to claim warranty.
Now, they break something electrical , they can’t
Suggest you read the T&C regarding the mechanical parts
They’re still covered!
“Prior to this, some person that broke something could attempt to claim warranty.
Now, they break something electrical , they can’t”
In the US, they still can make a warranty claim and Prusa needs to prove whatever that person did was directly responsible for what broke.
What written in the T&Cs is irrelevant. Having a broken PCB “appendix” instead of a tamper sticker is irrelevant. Consumer rights are protected by federal law to prevent this kind of thing.
I’m not an expert on this but I’ve done a decent amount of reading on the subject. Please correct me if I’m wrong. I think you’re confusing the right to repair with warranty coverage. https://www.consumer.ftc.gov/articles/0252-warranties Seems to state that you are at the mercy of whatever the manufacturer warranty states, if they have one at all. This could also be supplemented by a state level implied warranty. So unless you MUST break the appendix to fix your machine then you you’d probably have to prove your case, and not vice versa.
It’s actually not limited strictly to repair in the ‘something broke’ sense. If you break the sticker just to see what’s inside, you are still good. Do it to put something extra in and you are still good so long as that extra thing doesn’t cause the failure.
There is an issue with enforcement of this law. If the manufacturer refuses, you have to sue them. In the us courts, you pay for your own legal fees even if you win. So you may win the entire cost of the sub-$500 printer, but spend $5k on legal fees doing it.
Physically breaking something may also throw a wrench in the works. It’s not a sticker after all; you are intentionally damaging a circuit board.
I wouldn’t really mind for this particular printer; it’s almost price competitive with Chinese models that essentially have no warranty… except I feel like if it doesn’t get enough backlash it will spill over to their more expensive printers where things like the mmu spend years in beta and you actually need to modify the firmware just to get it to actually work. I suspect the core xy they keep teasing will need firmware hacks for at least a few years after release, just as the earliest i3’s did.
he’s likely talking about magnuson moss https://en.wikipedia.org/wiki/Magnuson%E2%80%93Moss_Warranty_Act
It’s one thing to peel back a sticker because you want to see what’s inside, but another to start fiddling with the firmware or literally snapping pieces of the board off.
Sure you can open your Xbox now without the warranty being void, but if you brick the thing because you were trying to JTAG your way to some emulators, Microsoft certainly isn’t going to help you. So why should Prusa be any different?
Yeah, but they can’t claim “the printer failed to detect a thermal runaway and burned my house down” after literally and willfully damaging the printers electronics.
Which is the point of the whole ordeal.
Doesn’t matter. They can’t void the warranty for all electronics. It’s a clear FTC warranty violation. No different than the warranty void if removed stickers. The action HAS to lead to the damage. Just doing something that MIGHT cause damage isn’t enough. I can’t believe so many people are trying to justify this. I can’t help but feel the response would be vastly different if it was any company other than Prusa, the printer the majority of commenters probably own.
Willfully breaking a PCB is most certainly going to lead to damage.
Given that FTC has no jurisdiction in EU, this is all moot. It’d only affect a reseller in the US.
He can still be sued in the US and have any US banking seized or incoming units impounded by customs as a bad actor. I wouldn’t be so sure there is no mechanism to at least cut off US sales.
Is he selling products in the US? If so, he sure can get sued.
unfortunatley, the FCC are trying to legislate for Dumb…Idiocracy is a movie everyone should watch…
As for your CLEAR VIOLATION…
Define ‘damage’
i’d define damage as
idiot not able to understand non prusa firmware
ugrades printer
printer no longer works
spends 6 months whinging about how Prusa is crap
no actual damage is done, BUT, prusa no longer has to waste resources supporting the previously mentioned idiot.
So, before you jump on your high horse, re-interpret this way
As of now
IDIOT – Upgrades board with custom firmware, printer doesn’t home, do stuff it shoud
Prusa – 2 weeks later….So, after 30 hours of support calls, several mailed out spares, NOW you tell us it was a custom firmware and was your own fault?
IDIOT…MWAHAHAHA
OR, with the new PCB feature
Idiot – Breaks the appendix thingy, cocks up the upgrade….calls prusa
Prusa – Have you broken the appendix thingy? – Yes, K, you’re on your own, #Hangs up
Multiply the first scenaro by several thousand idiots and you can soon see how a company can go bankrupt trying to do the right thing
I just say that the appendix allows Prusa to do the right thing by people that do the right thing. it removes a significant amount of mistruths on the IDIOT’s part…
I guess if you switch off the fans and set the heating to permanent on you can start a nice fire. Simce the machine is internet connected you could do this remotely given there is a malicious/buggy firmware flashed
Fire hazard i think. Somebody mentioned there is a SWD connector on the board. If so, it is possible to reflash without breaking the “fuse”. You just need “specialized” equipment.
Looks like they want to deter the kind of people that watches youtube video how to flash whatever “better” firmware downloaded who knows where knowing very little what they are doing and than be left with a printer in unknown dangerous state.
The reflash would be safe if and only if some kind of physical thermal fuse is present, which is not. All safety mechanisms of this kind of a printer are firmware based.
I still may be completely wrong, but looks like they try to deter mainly people, who don’t know what they are doing with “Beware, this is VERY dangerous” sort of “sign”. I thinks (just my guess) if the bearing or something similar goes bad, they will not ask about the Appendix, but if you will claim, that your extruder into molten blob by itself, they very well can ask about that.
they don’t void the warranty on everything just the electronic component so i guess just the board everything else should be fine. also i have a very hard time to believe this would be illegal in the US since almost all consumer electronic come with similar safeguards. if you dismantle some electronics you will notice that there is almost always a “warranty void if removed” sticker exactly on the thing you need to open to access the inside or in some case like in phones you have some moisture indicators so they can void your warranty because you got it wet/dropped it in water.
i really don’t see the difference here and if the developer program is any good that will be a non issue anyway.
“there is almost always a “warranty void if removed” sticker”
Those stickers carry no legal weight in the face of Magnuson-Moss.
It’s enough to stop a lot of people from tinkering, but it makes no difference to the legal responsibilities of the manufacturer.
Seems like companies put those on there and then deny warranty coverage because they know that your average Joe isn’t going to spend thousands on a lawyer to strongarm them into repairing their device that’s worth a fraction of that. Until someone with deep pockets that gives zero fucks about how much it costs takes them to court over it….
So? Last time I checked, Prusa wasn’t a US company…
The FTC has said those stickers aren’t legal
Unless they have some hardware protections for it, you can blow the nozzle heater if you upload two lines of code that just set the correct pin to output and turn the heater on… Perhaps you could drive stepper coils into electrical resonance where the voltage on them will rise up enough to blow the drivers out. There’s perhaps enough reactance and Q in the bed heater circuit that you could drive it into resonance too. And so on. It’s not inconceivable that one could let a lot of smoke out of that thing with judiciously engineered “firmware”.
I find it somewhat ironic that the burnt Anet A8 was linked to as an example of a disastrous user modification when the fault was with the original “as shipped” software configuration which was subsequently corrected by a user modification of the configuration.
that doesn’t make a lot of sense. if the user “corrected” the problem then why did the machine burn?
Others were fixed after the picture got around.
it didnt. the original firmware had no thermal runaway protection. the modded firmware did.
I like this solution as a whole. If we see a charred garage and a charred printer and a charred board with the tab still in tact it is a different conversation than if we see the charred board without the appendix. Many failures are tried in the press long before a court can review it. Prusa enables and encourages the hacks, but has found a way to win the press trial, so they can stay in business making great open source stuff.
Liability is real when you make something open source that has a heater attached. Insurance fraud is easy, but if you have to have a bit more technical expertise to turn your printer into a golden ticket out of a dumb mortgage, then it just has to be harder than the next available option for Prusa insurance to not have to buy houses.
I see it as similar to the sort of nod to the community that Rigol gives us with unlockable features that you buy, but have well documented hacks that they are not fixing. They are not the same, for sure, but a welcome mat outside the door to the hard work of engineers gives us an inviting place to call home.
But if you think about it, it makes sense.
Yes, in that circumstance the manufacturer was the one with the faulty firmware, but it does prove their point that you can have real-world implications of bad firmware.
It seems like a reasonable compromise — they give you the ability to flash your own firmware, but you don’t get any love from them if you do manage to break something.
I much prefer this idea vs some sort of secure-boot proofed SOC.
The problem is that it will have a chilling effect on development.
Potential developers may decide ‘damaging’ the board is not an option.
I wish someone would have posted the Prusa comment that 3D printers were not suitable for experimenters, and the reply that thankfully that wasn’t true, because Prusa originally only got involved in printer development because he wanted to make knobs for his DJ kit.
Rights and responsibilities..
Makers are vocal about “right to repair” and “right to modify”. Along with those come the potentiial to screw things up, and the responsibility to accept the consequences of your own actions. Any would-be Maker who can be put off by the last two would do well to spend some time thinking about how much they really want the first two.
When did voiding warranties stop being something Makers respected?
In a world raised on “I’m a victim” and “it’s all their fault” should we really be surprised it’s came down to this?
It’s not, it’s what they are try to void. They shouldn’t have to break the board to change the firmware. It’s very much against the law. The firmware change has to actually lead to damage to void the warranty.
Using the word “break” in this situation isn’t quite so cut and dry. Physically, yes, a user is breaking the board. But functionally, nothing on the board is breaking, ceasing to work, reduced in functionality or otherwise affected. To use the ever popular car analogy, that’s like saying you should be able to add disk brakes to a car originally equipped with drum brakes without having to cut a single hydraulic line to install different fittings, and still retain full warranty and hold the OEM liable for damages even if those damages were a direct result of an improper install of the disk brakes.
I’m sorry, but we don’t live in a fantastical utopia where companies have unlimited resources to be responsible for anyone modifying their product in any and all ways, nor a world in which people are universally honest and take full responsibility for their own actions.
This isn’t a right to repair issue, since breaking that tab isn’t done to *repair* the board. If a component on the board breaks, a user is free to replace it with a component of comparable specifications. Breaking that tab serves one, and only one, function – to replace the firmware and change the operation of the product.
In any case, it would be mostly trivial to lift the leg of the ucontroller that connects to that trace, thereby enabling custom firmware to be written, without having to break the tab on the board.
It’s not against the law in the US, and is not against the law in the EU. Period. Why are people repeating this nonsense?
Cite your source.
Let’s be honest, it will only put of those who don’t have a machine to lose, i.e. borrowed or shared or for work or just broke (financially).
I’d be hesitant to break the pcb tab on a work machine without serious thought and discussion, but if I was flush with cash and bought one of course it would get snapped, maybe not straight away but as soon as I felt I needed to.
“chilling effect” ??!!?!? LMAO!!! Chill out dude. If you are willing to get into your electronics and flash custom firmware on a device that could burn your house down, but not do a little snip snip on a circuit board, you need to reevaluate.
What happens if you break the appendix off but the two broken ends of the inner ground trace short at the point of the break – do you have a warranty claim? :-D
No, then you just have a board without warranty AND you can’t even flash it.
Then it’s time to attack the edge with a knife.
This solution of cutting paieces of multi-layer PCB is stupid and against good engineering practises.
Agree. What happens when the ‘feature’ lifts a trace. Shorts the board, causing a fire, and after $150k in legal fees, the case is thrown out. You still are out $150,000 in the USA.
Shots fired:
https://cdn.discordapp.com/attachments/456266386675728385/654766636217401348/unknown.png
He is still right, 3d printer is not a good FIRST project in embedded programming. Simple boards with some diodes are better. Then you move to some stepper control boards, then printers. But not printer as a FIRST project. Of course no one will stop you, but still, there are better options for first project.
Who is making a fuss here?
Briefly followed the link to reddit, but I could not find anyone complaining.
Just some confirmation and discussion about this nice method of leaving some evidence of tinkerering.
I like this (free) method of adding hardware jumpers to a PC, but with a small note:
Snapping of a piece of the PCB like this always has a risc of ripping of long parts of the tracks.
This can easily be prevented by making the adherence to the PCB stronger just next to the snap off point.
This can easily be done by widening the tracks significantly, or adding via’s on strategic places.
I’m not so into 3D printing, but if the whole electronics board can be replaced for a reasonable amount of monetary units (Which I suspect it is) then the whole subject is moot anyway.
In contrast to this, Today I saw a video of replacing some electronics board on a bobcat skid steer loader on youtube: watch?v=s_Ro4MnTXe8
It was a completely potted unit, which is somewhat understandable for stuff designed for such a rough environment, but USD1400 for a replacement board seems completely redicilous. I doubt that the board has more then USD50 in parts on it.
They’re trying an end run around the FTC’s rule. If a Prusa printer starts a fire, they can say to a courtroom “This wasn’t merely removing a sticker – they intentionally damaged the board in accordance with the manufacturer’s expressly documented instructions that clearly made it known that the printer’s safety features had been disabled, and safety was no longer under control of, nor the responsibility of, the manufacturer.”
Firmware should not be the only thing that protect a product from a fire or injuries. If that were the case, then every rev. of official firmware releases would require some safety re-certification. There are UL (or similar agency) recognized devices that could have been used.
https://users.csc.calpoly.edu/~jdalbey/SWE/Papers/THERAC25.html “Death and Denial: The Failure of the THERAC-25, A Medical Linear Accelerator”
Safety certification? Marlin code?
Come on. Certifying anything is man year count, certifying a software team is the same ballpark. I don’t think Prusa inc. have done that except basic ISO 9001 crap.
*cough* 737MAX *cough*
Ugggh, just no. FTC doesn’t affect anything Prusa does because, um, Prusa is not a US company. The worst that could even happen is if Prusa traveled to the US and there was an arrest warrant on him. And that won’t happen either, because he’d surely lawyer up if FTC tried to do anything that there’s no case law to back up.
and a savvy lawyer will shoot that down saying the MFGer left that door open intentionally allowing for harm. It is no different than leaving a hot tub or pool ungated in many municipalities. It doesn’t matter that the neighbor’s 4 year old trespassed. He drowned. The owner still has legal responsibilities to promote safety. I think we have a lot of EU-centric people here in for a shock how terrible US law can be (or beneficial depending on perspective).
You could just lift the pin and pull it high?
Sure, but that leaves a lifted pin with a bodge wire as evidence that you’ve altered the board *and* tried to circumvent the ‘take responsibility for your own mods to the device’ tab. That won’t look good if you try to push a warranty claim in court.. if anything, it will look like you were planning to damage the machine from the start.
Of course you can try to remove the wire and solder the pin back if you need to make a warranty claim, but speaking from experience, SMT pins don’t stand much flexing. I’d ballpark it at about a 10% chance that the pin will break off when you try to lift it, and a 30% chance that it will break when you try to bend it back down.
If anything, Prusa is showing faith in the people who do want to mod the firmware by assuming they’ll be honest enough to break the tab.
You can’t solder the pin back neatly if your house burnt down, which is probably the scenario they’re most worried about.
The physical damage to the board should be fairly evident even after the thing catches fire.
I also thought about it, or even desoldering the micro, reflashing it and resoldering again (which is not hard at all for LQFP packages), but from what I understood this appendix pin is just disabling the hability to enter in ROM DFU / SWD mode, and when you enter there and reflash a new firmware thru SWD or ROM bootloader, the original bootloader containing their key and the hability to flash signed bootloaders will be erased, and you will lose the warranty anyway..
I think this PCB feature is more about physically showing that it was “violated”, and make the user understand it.
But everything changes if they provide the code or HEX of the original bootloader, with the public key used to sign the official FW, then the desoldering-reflashing-resoldering of the chip would allow you to restore the original FW without breaking the appendix, and would be impossible to assess if any unofficial FW was ever flashed.
IIRC you can still just use the JTAG interface to program the device, BOOT0 is not involved. In fact, it’s how I do all my STM32 series development.
This is a great idea as while warranty void of stickers removed stuff is as I understand pretty weak legally.
Literal board modification is a lot more clear (I’d imagine).
I expect it to work the same way. If you DIDN’T break the board / remove the sticker then that proves you haven’t modified the device so whatever went wrong is the manufacturer’s fault. If you DID, that doesn’t prove you broke it, only that you could’ve.
If you want warranty service for damage that could have been damaged by your bogus firmware then they would most certainly be justified in denying you. In case you missed the point, this is not the same as a sticker on a playstation, in this situation bad firmware can cause physical damage. “Prove” is in the eye of the manufacturer, not you. They wrote the contract and you agreed to it when you bought the printer.
All this effort when really they could have just put thermal fuses on all their heaters and solved the problem that way without the technical complexity that having signed firmware brings and without upsetting the modding community.
it’s fake news no one is really upset by this.
It’s a sensible practice for manufacturers to make people realise that modifying firmware isn’t necessarily safer than modifying hardware.
Just like “warranty void if removed” stickers are paper tigers this is just a pcb tiger.
Your solution won’t prevent mechanical damage from crashing into stops or improper motor driving. If their firmware does this, it’s a bug and they want you to get warranty service so they can fix the bug. If your firmware does this, you’re an idiot. How do we distinguish these cases?
You realize that the new prusa mini and MK3 don’t have endstops and detects the ends of the axis by crashing into the end, skipping a step and then calling it homed? It can do this since the new TMC drivers have skip detection.
If your machine is getting damaged from ramming a endstop on a hobby grade 3d printer, you’re doing it wrong. Its not like on a CNC machine.
the mods people want to do is strictly in the pictures on the lcd screen everyone always stands up for prusa when in reality they are looking for ways to make their Cheaper printer cost more for the longevity of the company they knew before releasing any printer everyone will modify their printer when you give tinker’s a 32 bit board and lcd screen from an 8 bit bort you can only change words on now you can alter colors and icons on the lcd and that’s prusa looping back to make more money off a printer that they are streaming as budget if your not a tinker or understand anything about what could have been done to make this not like this DONT comment
I couldn’t follow that long ramble due to lack of punctuation or capitalization. But I see “DONT comment” so naturally I want to comment.
No big deal, just Prusa covering themselves from liability should a user load some firmware that does something stupid like try to burn down your house. The thing is if some enterprising hacker were to reverse engineer the encryption key from valid firmware released by Prusa (not saying it would be easy, just technically possible) it would be possible to sign any firmware and pass it off as a legit update thus bypassing all the effort they went through to tie firmware tinkering with a permanent hardware modification (removing the appendix). Similar things have popped up for hacking game consoles to run unofficial code/homebrew by patching them before native exploits to supplant the original firmware with cfw are developed.
I think it’s a smart way to do it. Keeps the companies warranty and liability intact, and doesn’t stop people from hacking it. A physical indication that “I’m taking personal responsibility for my health and safety”. It melts plastic at 240C and is left unattended for hours – hell yeah I’d want some liability protection from that as a company.
I smell a cheaper chinese clone coming in fast and with no such “protection”.
well of course you can. it’s on fire.
^ Why I read the comments.
Why would this protection be a reason to avoid buying a printer?
Maybe you would buy the cheaper one anyway, but that will be because of the price, not because of the tab.
Now someone will just remove the 4.7k resistor to hack and reclaim their warranty status by putting it back.
The resistor is on the header side. So even if you remove it, the appendix will still be grounding the pin.
Like somebody said above, lifting the pin seems only reasonable physical “attack” against this, but if you’re handy enough with the iron to pull the pin up without damaging anything, you probably aren’t scared of breaking the tab either.
It wouldn’t be a bad idea to have microcontroller-independent safety features on board. Something like one-time-programmable GreenPAK devices. It wouldn’t apply quite as strict limits as the firmware but still enough to prevent it catching fire.
So they’re moving to a 32bit chip? I wonder if they’ll apply the same to the other models. I was thinking about splurging out for a MK3S but I might wait a few months and see if they’ll use a new board for whatever upgrade they have next.
yeah its just 50 but the whole machine is under 400 so they don’t have a high margin to fund lots of costumer support and replacement parts. They are directly competing with the chines who don’t offer any real warranty and often don’t even care that they use opensource code in there closed platforms.
If they are not trying to bankrupt themselves, then the parts for this thing are about 35% of the price you pay. Their direct costs shouldn’t be above another 30%. The rest is to cover indirect costs, R&D and profits. So if you bought the parts from Prusa’s suppliers, in similar quantities, you should be able to put one of those printers together for $140 in parts :)
but also no real warranty and support anyway …. so why bother
maybe have dual firmware
1. firmware just for the temperature control and safety.
2. firmware to handle the data to get the model to 3d object
The hypocritical double standards are fun to read.
Same commenter (paraphrased):
“Prusa’s stance is understandable because stupid users could burn their home down and hold Prusa liable….”
“Panasonic rejecting the warranty of a toaster oven because the firmware has been modified is just greedy BS. They should take it back if there’s an obvious mechanical or electrical defect like the heating elements burning out.”
Amazing how the mind warps reality to match our desired ‘truth’.
got eem
This is very much illegal. The action of the owner actually has to lead to damage to void the warranty. Until the firmware change damages something, Prusa has NO right to void the warranty! NONE!
Prusa doesn’t void the entire warranty; this is basically a way to ensure that the person that wants to flash unofficial firmware is fully grasping the magnitude of their decision. 3D printers aren’t just some harmless widget, then can and have burned down houses.
Prusa Research is a czech company. Good luck trying to enforce american law against them.
Customs can seize their product and prevent US sales.
I don’t understand what the issue is?
Just lift the Pin directly at the MCU. It will be floating and won’t snap off I can assure you.
If you mess it up just replace the mega2560 (or even flash it externally).
I feel like a lot of folk angry at this move have never tried to run a small business. I sympathize with prusa in how they have supported people who took their product and modded it and expected prusa to still support them.
I frankly can’t wrap my head around how they can afford to work with / give warranties to parties who have been messing around with their product, especially with folk like me out there (fix it till you break it…).
I can see the reason why they have supported folks for so long but this still seems like it’s their right to change.
I also like the style of “do this if you know what you are doing”, it adds a bar to entry that will hopefully be a wake up call to anyone following a youtube tutorial that doesn’t understand the risk.
This is a great feature to boost the resale value because you know that previous owners have not messed with it.
I agree.
Warranty or not they still can’t just leave you hanging if they sell you a device that fails from “manufacturing defects” (or whatever), even if you have modified the firmware. Atleast where i live in northern europe, there are consumer protection laws.
Still, getting justice could be difficult.
I wouldn’t touch that printer, if i had any expectation of modifying it, which i do.
here is a cut and paste from PUBLIC LAW 93-63:
“neces- sary to keep any consumer product performing its intended function”
if the consumer fails to perform the necessary steps to keep the product performing its intended function, then the manufacturer has no obligation to honor the warranty. In this case the consumer fails by breaking the appendix because its intended function is to prevent damage from untested firmware.
There is no chilling effect. In any court of law the question of product safety (with possibly criminal consequences) is going to override any warranty considerations (strictly civil consequences).
Consider the alternative if they don’t do this and some nobody random jerk sues Prusa into oblivion for damages after purposefully messing with the safety without leaving a trace (pun intended).
This is a great compromise.
I think the biggest upset to people is from the fact that they can no longer mess up their printer and then get a free replacement under warranty by pleading innocence. There are far to many unscrupulous people who do this! All this appendix does is prove that the the damage is caused by your own stupidity and now a design flaw. Simple and perfectly understandable! If you are an honest person you will find no fault with this appendix, simple as that. It doesn’t stop you doing anything with your printer, it just makes sure the blame lies where it should if it all goes t**s up!
I think you’re flagrantly mischaracterizing them. You’re making basically the same argument people use to dismiss concerns with DRM, privacy, etc. It’s hard for me to even process that a reader of this site could seriously make this argument.
“If you are an honest person you will find no fault with this appendix” – this line is so on the nose I’m really not confident I’m not just taking the bait here.
If you are serious: About half the people are arguing that they don’t think this would be legally enforceable. Another portion are arguing that they don’t like being told they have to cause permanent damage to the device (no matter how trivial).
I am a person who has bought their previous printer (MK3) and have never even installed any sort of custom firmware on it. I would still be pissed if I had to rip a portion out of the middle of the PCB to do so even though I never have and don’t expect to ever do so. I don’t know why they made it an ‘appendix’ instead of a ‘tail’
i thought theres a simple solution, if your planning on going full on open source make your rambo or printer hardware
but guys lets be nice to the mini. anyone here looking foward to an xl
I don’t know the legality of this (I’m not going to pretend to), but I totally understand where they’re coming from liability-wise.
I’m a bit skeptical of the implication that many bogus warranty claims result from use of custom firmware as opposed to during carelessness during assembly or (mis)using a program like pronterface to issue a bunch of commands that result in damage.
My biggest problem here is that it requires cutting this portion out of the inside of the board- they couldn’t find a way to move it to the edge of the board or *at least* make the piece have only one point connecting it to the rest of the board? Really?
One thing that really bothers me whenever there’s negative talk about Prusa printers is the weird cultish devotion some people have, as demonstrated in this comment section. (For the record, I own a MK3, I think it’s great, and my experience with customer service has also been great, so I’m not trying to bash the company)
For example: People talking about the developments of the company and attributing then directly and solely to Josef Prusa himself, or referring to him by just his first name as if they have any sort of familiarity with him. Others in here also argued “Prusa shouldn’t be liable for damages caused by the user” as if anyone was arguing they should in the first place.