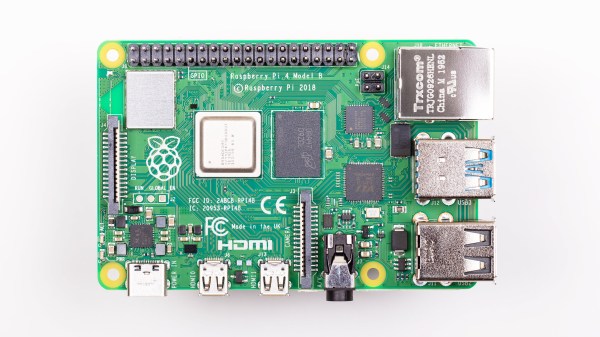
We’re all familiar with a typical configuration sequence for a new mass-market IoT device. Turn it on for the first time and it exposes a temporary Wi-Fi network, connect to that network and open a Web page for device configuration. Wouldn’t it be useful to be able to incorporate that functionality into your own projects without having to write it yourself! Happily now thanks to [Peter Walsh] you can, with his AppDaemon project for the Raspberry Pi.
At its heart is a set of Perl scripts that run whatever your software is, then monitor a GPIO. A button press toggling the GPIO stops the application and fires up the access point and web server. Handily the code can all be found in a GitHub repository, and there is a run-through of the features in a video that we’ve placed below the break. It’s not something that will appeal to everybody, but for anyone who has to pass their work onto people who can’t dive into a config file and break out the editor, it should be a particularly useful addition to the armoury.
Continue reading “Easy Device Configuration For Your Pi Projects”