The Kindle Paperwhite, Amazon’s newest e-ink reader featuring a touch interface with a higher contrast display, is now officially jailbroken.
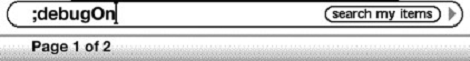
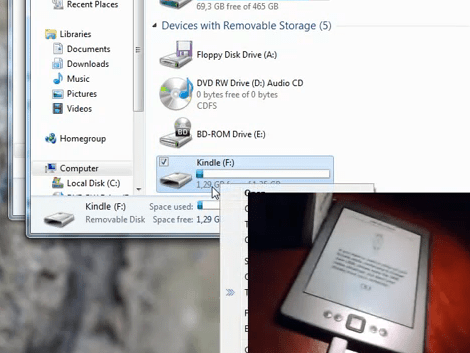
[geekmaster], the geek master behind this hack, based his jailbreak off [Yifan]’s previous hack to jailbreak the Kindle Touch. Installation is a snap, and only requires you to upload the data.stgz file to the root directory of the Paperwhite and restart the device. On the next boot, the Paperwhite will be jailbroken, allowing you to do tons of cool stuff with a tiny Linux device connected to an e-ink screen.
We’ve already seen a few really cool uses for jailbroken Kindles including a weather station display and a serial terminal for your Raspberry Pi. Cracking the newer and better Kindle Paperwhite means those e-ink projects you’ve been thinking about building just became much more attractive.
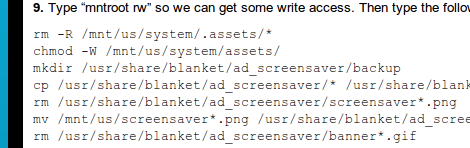
One word of warning from [geekmaster], though: USB downloader mode isn’t yet enabled. If you brick your device, you’ll need to connect your Kindle to a serial port. This shouldn’t be a problem for Hackaday readers, but it is something to watch out for.