Back in the early dawn of the GUI age, cathode ray tubes were the dominant display technology for the personal computer. In order to avoid burn-in of static display elements, screensavers were devised to help prevent this problem. Out of love for the software of yesteryear, [Greg Kennedy] has put together a bot that posts Windows 3.1 screensavers on Twitter.
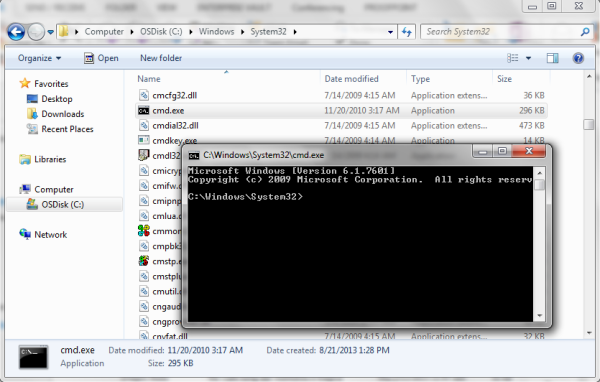
A Perl script runs the show in this case. Screensavers are packed into “units”, which are loaded by the script. A basic Windows 3.1 environment is then configured, and loaded into a specially patched DOSBOX that allows automated demo recording in a headless environment. Once up and running, video is recorded of the desktop and subsequent triggering of the screensaver. After a couple of minutes, the recording is stopped, and FFMPEG is used to transcode the video into a Twitter-suitable format. It’s then a simple job of Tweeting the video using the standard API.
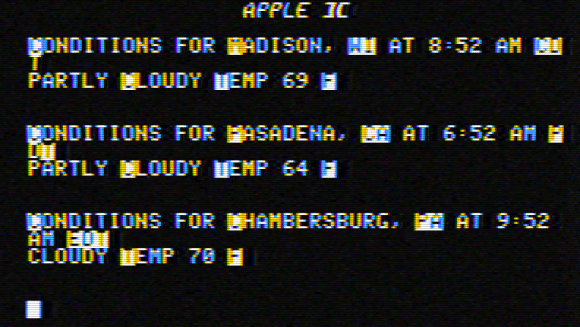
It’s a fun project that makes sharing old screensavers easy. Be sure to check out the Twitter feed @dot_scr. If you’re addicted to the vintage aesthetic, try this Apple ][ screensaver hack on your Linux boxen. Video after the break.