Electronics leak waves and if you know what you’re doing you can steal people’s data using this phenomenon. How thick is your tinfoil hat? And you sure it’s thick enough? Well, it turns out that there’s a (secret) government standard for all of this: TEMPEST. Yes, all-caps. No, it’s not an acronym. It’s a secret codename, and codenames are more fun WHEN SHOUTED OUT LOUD!
The TEMPEST idea in a nutshell is that electronic devices leak electromagnetic waves when they do things like switch bits from ones to zeros or move electron beams around to make images on CRT screens. If an adversary can remotely listen in to these unintentional broadcasts, they can potentially figure out what’s going on inside your computer. Read on and find out about the history of TEMPEST, modern research, and finally how you can try it out yourself at home!
 TEMPEST isn’t anything new. This declassified introduction to TEMPEST (NSA, PDF, SFW, FTW) tells the story of a nameless Bell Labs tech working on signals intelligence (radio stuff) during WWII. The story goes that he noticed strange intermittent spikes on his oscilloscope and then managed to track down the source to a piece of unrelated crypto machinery working in a “distant part of the lab”. He then managed to extract enough information from the spikes to read the plain text being fed to the crypto machine. Eureka!
TEMPEST isn’t anything new. This declassified introduction to TEMPEST (NSA, PDF, SFW, FTW) tells the story of a nameless Bell Labs tech working on signals intelligence (radio stuff) during WWII. The story goes that he noticed strange intermittent spikes on his oscilloscope and then managed to track down the source to a piece of unrelated crypto machinery working in a “distant part of the lab”. He then managed to extract enough information from the spikes to read the plain text being fed to the crypto machine. Eureka!
Being engineers, the Bell Labs folks worked out a complete solution. A combination of shielding and filtering the signals coming out of the crytpo mixer in question to completely obliterate any outside trace of the plaintext. And TEMPEST was born. And just a few weeks later, TEMPEST suffered its first death.
To mask all external signals, the crypto mixer had to be completely encapsulated (read: Faraday cage) and this made it overheat. And you couldn’t get at the control knobs. And it made it hard to fix when things went wrong.
Worse still, all of the mixers deployed in the field would have to be recalled and retrofitted, and that was expensive. So the Signal Corps issued a directive to control the area 100 feet around the crypto mixer, and that was that. After all, as the NSA paper notes, there was a war on.
TEMPEST rides again: van Eck Phreaking
After the war was over, the CIA started looking into TEMPEST for its own purposes. Shortly thereafter, it became apparent that the Soviets were doing the same: in 1954 the standards for electromagnetic emissions from teletypes and other communications equipment were much more stringent than those for motors, which are in principle more noisy.
In the 1960’s we discovered that everyone was spying on us, from a high-gain antenna pointed at the US cryptocenter in Tokyo to the discovery of 40 microphones hidden in the US Embassy in Moscow. Spooky stuff, but largely limited to the classified world.
TEMPEST entered popular hacker culture in 1985 through this paper (PDF) by Wim van Eck. The comparatively small logic voltage signals coming out of your computer enter the CRT monitor and are amplified up to hundreds of volts in order to deflect electrons and make the phosphors glow to spell out whatever you’re reading. What soon became known as “van Eck phreaking” was as simple as receiving the radiation from the CRT using a radio, and re-combining that radio signal with locally-generated horizontal and vertical sync signals and then replaying that onto a monitor. Voilá, a perfect copy of a remote screen.
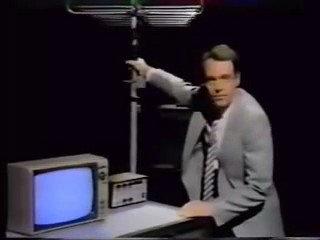 By the time van Eck’s paper came out, the spy world had been phreaking for at least twenty years. Nonetheless, the graphic demonstration (pun intended) of remote surveillance power caught the public’s imagination in the late 80s and early 90s. This retro-spectacular BBC TV Show, “Tomorrow’s World” covered TEMPEST, building up a van Eck rig and pointing it at a BBC Micro computer across the room. Neil Stephenson showed how cool he was by name-dropping van Eck in Cryptonomicon (a must read for any geek). Ominous white vans with telecoms equipment started showing up in movies across the country.
By the time van Eck’s paper came out, the spy world had been phreaking for at least twenty years. Nonetheless, the graphic demonstration (pun intended) of remote surveillance power caught the public’s imagination in the late 80s and early 90s. This retro-spectacular BBC TV Show, “Tomorrow’s World” covered TEMPEST, building up a van Eck rig and pointing it at a BBC Micro computer across the room. Neil Stephenson showed how cool he was by name-dropping van Eck in Cryptonomicon (a must read for any geek). Ominous white vans with telecoms equipment started showing up in movies across the country.
More great TEMPEST information can be found at cryptome.org’s collection of TEMPEST documents.
… in a Teapot
So does TEMPEST really matter these days? If you have to ask, the answer is “probably not for you”. This comprehensive resource on TEMPEST reports on a US military consensus that there’s not that much risk of TEMPEST-related breaches within the US to warrant the expense. For instance, the National Reconnaissance Office got rid of its domestic TEMPEST requirements in 1992. At the same time, CRTs have been phased out for LCD screens and computers have all become generally less radiative for non-spying interference reasons.
On the other hand, TEMPEST is too cool to die. Our favorite TEMPEST researcher at the moment is Markus Kuhn, who essentially did his dissertation on TEMPEST. (He also proposed a great hack where you look at the reflected light in a room with a CRT monitor at high frequency and back out what the image on the screen would be that generated that time series.) In his “soft-TEMPEST” project, Dr. Kuhn proposes using slightly smudged-out fonts to take the high-frequency edges off your radiated signal, solving the previously-hardware TEMPEST problem in software.
Post-TEMPEST and EMSEC
SANS wrote a whitepaper on TEMPEST that’s a great read for the security professional. (Although the use of Comic Sans makes it looks like a bad cartoon! Yes, SANS, we get the joke, but really.) According to SANS the codename TEMPEST is outdated, and it was never clear whether TEMPEST referred to the problem or the solution anyway. Those in the know now refer to the field as Emission Security (EMSEC), which covers much more than the direct reception of the emitted signals of CRT monitors.
 And viewed more broadly, TEMPEST is just one of many side-channel attacks where the attacker tries to gain information about the device’s internal state from things like radiation, power usage, response latency, etc. This recent paper uses emitted TEMPEST-like radiation and software-defined radio to determine where the encryption routine in GPG is spending its time, and by sending certain keys to the GPG routine and monitoring the response, they can break the encryption.
And viewed more broadly, TEMPEST is just one of many side-channel attacks where the attacker tries to gain information about the device’s internal state from things like radiation, power usage, response latency, etc. This recent paper uses emitted TEMPEST-like radiation and software-defined radio to determine where the encryption routine in GPG is spending its time, and by sending certain keys to the GPG routine and monitoring the response, they can break the encryption.
There are rumors (for instance at “The Complete, Unofficial TEMPEST Information Page”) of new and improved codewords: HIJACK And NONSTOP. These appear to be TEMPEST-like exploits where a device is brought in with the target computer and essentially re-broadcasts the emissions in order to make a stronger signal.
 In that vein, the Snowden leaks brought us RAGEMASTER (warning: leaked classified document — do not click that link if you have security clearance and hate filling out paperwork) which is a re-transmission bug that gets embedded into the monitor’s video cable. Pretty slick. Open-source work on similar technologies takes place at NSA Playset.org. Michael Ossmann’s CONGAFLOCK gets you halfway there.
In that vein, the Snowden leaks brought us RAGEMASTER (warning: leaked classified document — do not click that link if you have security clearance and hate filling out paperwork) which is a re-transmission bug that gets embedded into the monitor’s video cable. Pretty slick. Open-source work on similar technologies takes place at NSA Playset.org. Michael Ossmann’s CONGAFLOCK gets you halfway there.
So maybe you do want to buy that expensive TEMPEST laptop after all.
Hack the TEMPEST!
TEMPEST isn’t just for spooky uses. You too can use unintentional emissions for fun at home. Tempest for Eliza is a quick Linux hack that plays music over the radio of your choosing by displaying alternating black and white pixels on your monitor at just the right frequency. This plays music for the feds pointing their TEMPEST-sniffer antenna at your monitor. If you’re not currently being spied on, you can play the music for yourself using a handheld AM radio.
To use Tempest for Eliza, you’ll need to know some things about your monitor’s refresh rate and pixel layout and such. For our LCD monitor, for instance, xrandr --verbose outputs a line like:
1280x1024 (0x4d) 108.000MHz +HSync +VSync *current +preferred
h: width 1280 start 1328 end 1440 total 1688 skew 0 clock 63.98KHz
v: height 1024 start 1025 end 1028 total 1066 clock 60.02HzThe numbers you’ll need are the pixel clock (108 MHz), the height and width (1280×1024), and the total pixel count including the dead time at the edge of the screen (1688). You then pick a frequency that you’d like to transmit on. 1000 kHz = 1 MHz, which is right in the center of the AM dial on a normal radio, or try other frequencies if you’ve got a ham radio that can do AM demodulation at higher frequencies.
 For 1 MHz, with the parameters above, the command looks like:
For 1 MHz, with the parameters above, the command looks like: ./tempest_for_eliza 108000000 1280 1024 1688 1000000 songs/forelise. Here’s a YouTube demo of what it looks like.
Now you can use Tempest for Eliza as a rough TEMPEST-leakage gauge. Where you hear the music best, that’s where you’re radiating from. The back of our trusty old LCD monitor broadcast loud and clear, although it seemed to emit through a very small hole on one side only. Our guess: there’s shielding everywhere, but cables have to get out somehow. We also noticed that “Für Elise” played louder behind the monitor than in front.
In line with Dr. Kuhn’s conclusions in this paper on LCD monitors (PDF), we got some signal out of the DVI cable, though it wasn’t as strong as the near-field on the back of the LCD monitor. We also noticed some periodic clicking-type noise coming from the cable, which we take to be a factor of the pixel clock mixed with the tuned frequency (1MHz). Or something like that.
Our laptop (a Thinkpad X220) seemed relatively quiet in comparison. You can still hear the music, but it’s even quieter on the laptop’s display than the larger monitor, and you have to place the antenna right up to the screen. We’d read somewhere that the hinges, where the monitor cables pass through, are particularly noisy, but we couldn’t back that up empirically. It seemed pretty much the same everywhere.
Feedback
From the very beginning, TEMPEST was a great hack. The van Eck method of receiving the signal and reconstructing the sync signals is awesome and very low-tech. But with the significantly cheaper computing power at our fingertips today, including advances in open-source software-defined radio, even more sophisticated TEMPEST-like attacks could be within reach. Finally, there are still a lot of leaking electronic devices out there, and we’d bet that they’re mostly under-researched.
So download and run Tempest for Eliza, and have fun with the radio emissions coming out of your monitor. If this pushes you on to the next level, have a look at this video on SDR TEMPEST-like ideas that you can try out on the cheap. Or get inspired by the spooks; after all, they’re professionals at this sort of stuff. When you get something cool, let us know on the tips line. Get yer phreak on!
















“TEMPEST” is an actual acronym:
Tempest = Transient Electromagnetic Pulse Emanation Standard
It’s actually just a code word, but has many backronyms, such as Tiny ElectroMagnetic Particles Emitting Secret Things :)
Not an acronym: http://www.cesg.gov.uk/servicecatalogue/TEMPEST/Pages/What-is-TEMPEST.aspx
“S2H”, actually I was going on the official title and acronym given to me in the first TEMPEST class I took in the late 1970’s, while in the US Army. It was on all of the training documents we used.
Only at a later date, when TEMPEST became known in the public domain, did it become a ‘buzzword’. (That was about the same time the US Government went acronym crazy with names for programs and technology.)
Back in the early 80s, I managed a TEMPEST-shielded computer room, and the DoD TEMPEST standards documents were all quite clear that it’s just a codeword, not an acronym. (And “transient electromagnetic pulse” doesn’t really make sense for what TEMPEST gear was used for; it’s outbound signal leakage protection, not inbound EMP protection.) The choices were either to use regular computers in a big shielded room, or small computers in shielded boxes, which were pretty expensive and not that powerful (since PCs were new), and dealing with monitors was pretty annoying.
The room was about 50×50, and the wall panels were basically plywood with sheet metal on both sides, joined together by fancy metal joints, with copper-wool padding in the spaces. Air vents used metal grating with small holes in it. Power cables had big filters on them. Fiber-optic communication circuits went through penetrations that had 1/8″ waveguide holes about 2″ long. Our maintenance test equipment ran at 450 MHz, which was a reasonably high frequency compared to our 10-20 MHz minicomputers, and the room was tight to about 110dB. Even at that frequency, though, we’d occasionally have small leaks we’d have to patch with copper tape, and if you put a paperclip through one of the waveguide holes, the meter would peg about halfway through.
Shielding a modern computer would be a lot harder, because higher frequencies penetrate much smaller holes, and monitors run at much higher frequencies.
Sounds like I dealt with something similar.
The whole wing of the building was designated as the SCIF, and within that area were several shielded rooms. Each one had a double door entry (man-trap), where only one door was ever open at a time.
One room was strictly the RED/BLACK telco, telex and fax. Another room was for the computers (PC’s, printers, tape drives, etc.). The third room I had no clue what they were doing in that one (Not my job. Didn’t know, didn’t care).
The way the instructor explained it… TEMPEST was to keep anything from ‘sneaking’ out. EMP hardening was to keep anything from ‘sneaking’ in!
All the power was run through the “conditioner” boxes. Ditto with the telco circuits. Building got torn down in the 90’s and something purpose built replaced it. Several times bigger. Retired by then.
Wow, I was working in a TEMPEST R&D lab building the test equipment and designing shielding various equipment for Gov’t use right about the same time.
I was there once when they assembled what was on the IBM terminal in the screen room on an oscilloscope outside. That was 1980. (obviously the shielding leaked).They had been doing it for a long time at that point. I always thought it was so classified because just about any HAM with the slightest hint could figure the whole thing out. BTW, the power line, and the serial com line was easy to tap and the hard to shield.
The Navy used the shielding tech for their equipment to control the EMI between sensitive listening equipment on board.
There is an EMP tie in. There was a lot of discussion about tying the two together since they are basically the same type of shielding, when EMP protection was first being discussed
Wouldn’t the tin (Aluminum these days) foil hat be used to prevent TEMPEST from snooping on you? Not the hat itself.
But yeah, I mean you could infer what someone’s CRT was showing back in the day, but radiation from modern devices is terribly lower and also way more complex at the same time, and now that everyone is radiating everything all the time, picking a target of interest out of all that clutter is probably damn near impossible.
You’d be surprised, a former employer had a demo doing this attack on a modern LCD laptop. Video data (VGA or otherwise) can radiate from the motherboard or video hardware and be picked up in the same manner as was described in the article, it just requires more specialized (read: VERY expensive) hardware and software.
You need a wideband capture, but otherwise it’s not dissimilar from what people are doing with hobbyist SDR these days. I’m nearly sure that there’s some more clever hacks out there that’ll bring it down to the realm of the reasonable.
VERY expensive isn’t what it used to be. My guess is you could get the laptop LCD capture down under $3000 with one of the Ettus USRP boxes and a good antenna. The rest, as they say, is just software. :)
You’re probably right with the SDR stuff, I hadn’t thought of that!
I’ve captured laptop video signals with much cheaper equipment – a TV. And no, not on purpose :-)
It was about 20 years ago, the laptop probably ran 640×480 VGA (maybe EGA?), and of course it was an analog CRT TV. It wasn’t particularly in sync, so it scrolled vertically while it was doing it, and there were about three partial copies of the computer screen on the TV screen, but you could vaguely read it. Our guess was that it was mostly leaking from the VGA monitor port on the back of the laptop, rather than the LCD screen’s circuitry.
Back in the mid-70’s, I worked for a firm [Q1] that made a series of desk [built into] computers. When the military looked at using them for word processing, they discovered that the way our display [multi-line plasma] worked, they could not get any intelligence from the signals from the display, as opposed to the CRT’s that were in common use at the time. We used a daisy wheel printer, and even that was almost impossible to get info from while it was printing, due to the x & y paper/print head motions, as well as that of the daisy wheel occurred at the same time, with the print hammer firing only when the 3 other operations had all completed – effectively randomizing the wheel position of the character being printed.
The best part was when they asked about a ‘core-clear’ program [needed in magnetic core memory computers] to remove any classified content in the memory, and I told them it was DRAM, and disappeared as soon as power was turned off to the unit.
With physical access to the hardware, DRAM data can be recovered. https://en.wikipedia.org/wiki/Cold_boot_attack
True, but this was in the days of the 8080/Z80 and 4K DRAM, and that type of attack was far in the future.
That is true, but cutting edge technology for most people could be 10 to 20 years behind what is going on right now behind closed doors at some three letter agencies.
If you were a bit more enterprising (and possibly dishonest), you could have sold them special hardware (ie a power switch!) to do just this.
In all seriousness, a former employer of mine leased office printers, and whenever we returned one, we would pull out the printer’s memory hardware and destroy it. Not entirely sure if this memory was volatile or not, but it was just part of the security procedure.
Who needs TEMPEST when you can just read Hillary’s email?
Elliot, should you really be helping protect people who are helping perpetuate illegal spying on the general public?
Just goes to show why proper shielding in products is necessary!
I’ve often wondered if you could get a TEMPEST equivalent by filling a office with identical computers, with most doing random activities. Would they generate enough noise to mask what the others were doing?
And for passive devices being stimulated by outside radio transmissions, how well would a series of corner reflectors mounted on the outside of the building work. It strikes me that they’d bounce back on much modulated signal, whatever its frequency, that the return from the passive device would be swamped.
An interesting suggestion to be sure…if you had a super tightbeam antenna you might be able to get around that, but if you stuffed your most secret computers in the middle of a cubicle farm it would be even harder to find the good stuff from the noise.
Imagine how fun it would be to pick silly images on those dummy computers with the anticipation of a hacker seeing them.
Or sit a monkey at each as see what gets interpreted first, works of Shakespeare or Game of Thrones…
I was told by a TEMPEST engineer masking does not work.
Well, that’s two Neal Stephenson book references in one week (rod logic/Diamon Age, “Van Eck Phreaking”/Cryptonomicon)…. methinks a trifecta is in play.
I discovered a secret ‘backdoor’ into the Cherry Master 8-line gambling game by Dyna using the TEMPEST method.
Here is a video of it in operation for those not familiar with the game.
https://www.youtube.com/watch?v=k3V9PHlEYFA
I used to freelance service, video and pinball games, for several amusement vendors.
I would have never gone down the path of pursuing this ‘backdoor’ if it wasn’t for one day when testing a game board after repairing it, when I noticed that several of the game panel lamps were acting suspiciously.
Every technician that I know of who services these these boards, makes a test bed using the existing wiring harness and front panel buttons containing incandescent lamps.
I on the other hand had built a custom test jig with small buttons and LEDs, that I could test a number of boards from different manufacturers, without the need for a bunch of jigs taking up space.
Some LEDs would go dim instead of shutting entirely off, like they were supposed to do.
After puzzling over this for some time, I began to suspect that the software developer of this game intentionally added this ‘feature’ for illegal/unethical financial gain.
Instead of simply turning the lamps on and off, the developer made the extra effort to use PWM to control the intensity from full-on to barely-on, but not having enough voltage to light the incandescent lamps.
I had literally stumbled into a goldmine!
It is safe for me to tell you this story now since these games are no longer operated in the state where I live.
As seen in the video at time 0:51, when you enter into the Double-Up screen, is when all the magic occurs.
With the card on the right being face down, you are to choose whether it is going to be Big (higher than 8) or Small (less than 8). This is when the LEDs act weirdly and go dim, but should instead be turned off.
During this time, if you place a pocket-sized AM radio next to the buttons on the front panel of the game, and have previously tuned it between strong broadcast stations, you can detect a distinct sound generated by the game, which will indicate whether to press HI or LO, or bail out because the next card is an (8) eight, and you will lose.
If you plan of implementing this, you might want to use an earbud, since the static from the radio will draw attention. You might also want to build a squelch circuit, like I did, to keep yourself from going insane from all that noisy static.
–
I’ve always been in to embedded financial machines and poker. This seems cool. I bet things like this are still out there on modern machines like those worn out illegal backroom video poker machines.
https://www.cl.cam.ac.uk/~mgk25/ieee02-optical.pdf
Here is another interesting TEMPEST attack.
Reflected light used to see whats on a hidden screen.
Just a headsup, Cryptome.org implants a malware tracker and maybe worse, courtesy of the NSA.
From one of the Snowden dumps, and discussed a bit over at Schneir on Security
I can’t even remember when I first read about this. I seen a live demo in 2006 I think.
In britain you have to pay a tax for using a TV, to pay for public broadcasting, and back in the CRT days they actually had government people drive around in vans using the CRT pickup method to determine if a house had a TV and then they check if the person was paying the license, and if not you’d get fined and forced to pay.
And if you think that’s extreme, in some european countries they have a law when you can put the trash out, and if you do it too early (even on the right day) city/county special cops will sometimes take the garbage bag, go through the garbage to find any letter or some such with a name/address and then go to the person and present that as evidence. But imagine the job of rifling through garbage to bitch about putting trash out too early, what a… ‘dedication’. And what a ‘dream job’.
We had the cable company here going around monitoring RF to see who was tuning in a station that was within a range of stations they hadn’t subscribed to.
I am so GOD DAMN TIRED of hearing that INCORRECT term.. TIN has not been used to make foil sense the end of World War 2… The term you’re looking for is.. “Aluminum Foil Hat”. And considering the term was actually coined for people who were questioning how the BBC in London was able to broadcast details about the JFK assassination before the FBI even released the detail, events that took place LONG after the end of World War 2, It should have been Coined “Aluminum Foil Hat” right from the start.
Old habits die hard. Have you ever heard someone refer to a refrigerator as an icebox? How about a video recording as videotape?
If you’d had your hat off when the broadcast went out, you’d have heard we’re supposed to keep the details secret and refer only to “TIN”.
I’m curious, does anyone think about using TEMPEST -esque EM as a beacon, rather than carrier signal? [Attribution of future inspired work is not required]
TEMPEST attack on pendrives?!
Actually this might be a way to prevent someone copying classified data, if you can detect something strange that isn’t authorized (ie admin guard key) then its possible to modify the victim machine so that it writes garbage data and then intentionally blows the USB D+ line and regulators in the drive upon removal without valid password thus rendering any efforts in vain.
Also modify optical drive to use non standard wavelengths so an off-the-shelf DVD/BRD/etc disk will read fine but not write.
Special disk will work fine but not read on any drive, also encrypts data using the admin guard key so it won’t work on any *other* special drive.
Another method: non standard Bluetooth by replacing the usual 26 MHz dongle with a slightly lower frequency unit so that even with an SDR you will be unable to get anything coherent because the USB data bus is also modified to hash D+ and D- with a PRNG so that without an identical unit nothing will happen.
As Crypto Museum we would like to add a short note about TEMPEST for everybody interested. The Russians had very good knowledge of it. The power supply of their Fialka Cipher machine demonstrates this:
https://www.cryptomuseum.com/crypto/fialka/psu/tempest.htm
So, TEMPEST is not only about shielding and so, but also about obscuring.
Another nice story is about ‘the thing’, a hidden passive device in the U.S. ambassador ‘s room in Moscow. The Russians implanted the device inside a wooden carved object that was given by a Russian scout group to ‘welcome’ the ambassador:
https://www.cryptomuseum.com/covert/bugs/thing/index.htm
Therefore, in each serious embassy today there is a shielded room where most secret discussions take place. This today is a pure TEMPEST measure.
And not to forget: Apart from this there is spying and bugging. For one of the most nice artefacts we came across see these pages: Bugs do not have to be small ;-)
https://www.cryptomuseum.com/covert/bugs/ec/srt52/index.htm
Enjoy !
Marcus