Human ears are capable of perceiving frequencies from roughly 20 Hz up to 20 kHz, at least when new. Correspondingly, our audio hardware is designed more or less to target these frequencies. However, there’s often a little extra capability at the upper edges, which [Jacek] shows can be exploited to exfiltrate data.
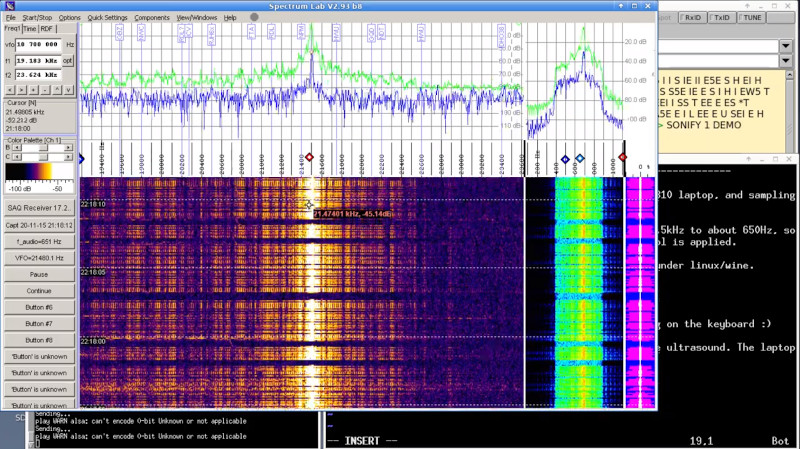
The hack takes advantage of the fact that most computers can run their soundcards at a sample rate of up to 48 kHz, which thanks to the Nyquist theorem means they can output frequencies up to around 24 kHz — still outside the range of human hearing. Computers and laptops often use small speaker drivers too, which are able to readily generate sound at this frequency. Through the use of a simple Linux shell script, [Jacek] is able to have a laptop output Morse code over ultrasound, and pick it up with nothing more than a laptop’s internal microphone at up to 20 meters away.
[Jacek] enjoys exploring alternative data exfiltration methods; he’s previously experimented with Ethernet leaks on the Raspberry Pi. Of course, with any airgap attack, the real challenge is often getting the remote machine to run the exfiltration script when there’s no existing remote admin access to be had. Video after the break.















Also a problem: internal speakers are typically not capable of producing these high frequencies.
So this raises the question: what is the highest frequency that internal laptop speakers can generally produce?
Plenty high, they’re very tiny speakers with low moving mass. I know that the little speakers in my Toshiba Satellite 490 could go up to 19khz – i don’t know if they went any higher or not, but i couldn’t hear that.
My phone’s speaker does 17khz, i can still hear that, but only with one of my ears.
I’ve been using my phone as a tiny test transmitter for a receiver for SAQ Grimeton. The tiny 17,2khz signal radiated by the phone’s speaker can be picked up from 2 meters away, but i still need to improve the receiver a lot.
My phone’s speaker might go higher, but over 15 years, a few festivals and numerous bar shfits later, my ears are slowly starting to get less sensitive to high frequencies.
Man, if someone had a list, table or database with the speaker and microphone specifications of all the laptops and phones… that would be fricken sweet awesome! Wondering if someone can scrape the data off some sites since I want to say there are for sure cell phone info that can be scraped from more than one site? Not certain about laptops.
Do you think the output of these speakers immediately drops to zero at their manufacturer rated maximum frequency?
I suspect that for these sorts of not-as-intended uses experimentation would be better than a stack of datasheets.
I have issues with wanting to iterate through data to find the best specs, or at least try to let the World know, since I worked in a regulated validation setting. Mining data was a past life routine that I still have thoughts instinctualy.
Now that you noted, demonstrating how to measure the response way cost effective home brew would be an awesome video.
Usually they do. Usually the recipe is: the smaller the speaker, the higher the frequency it can produce.
What about infrasound?
Very low bandwidth, and the efficiency drop-off in the speakers are much steeper (more like a wall) than at higher frequencies.
“they can output frequencies up to around 24 kHz” I think you mean sample and decode signals up to that frequency.
Depending on the cut off frequency of the anti-aliasing filter, with 48khz sample rate they’ll be able to output signals up to 20 to 24khz. 44khz ones often go to 20khz, so 48khz ones will likely go just a bit higher.
I was just wondering the same, since I went through this exercise with detection of ultrasonic signals thinking I can detect up to 192kHz with the newest Sound Blaster X G6 384kHz DAC. Well, yes in regards to sampling and decoding analog output seems correct approximately.
Though I was wanting to record up to 192kHz and found the ADC is not the same. The 192kHz ADC can only sample and record approximately 96kHz frequency range without aliasing. Still a nice range to work with if you have a great transducer or MEMS, like last I read the SPU0410LR5H and FG-23629-P16 are the best… I want to say up to 784kHz. The Dodotronics and other portable ultrasonic mics are awesome since self contained with recorders up to 384kHz.
I’ll note while at it, still seems the SB1095 is about the best COTS cost effective external USB device or maybe a Behringer UMC202HD. Plus the SB1095 has the hack to improve the performance even more, that I’m thinking if someone did a disassembly and assessment of the UMC202HD… improved performance may be capable.
Any other ideas? Neat topic!
QRQcw has some really interesting videos on the topic… not so much exfltlrating data… though thinking maybe for inspiration.
Did the same about 5 years ago. This one can have the frequency easily changed.
#!/bin/bash # # txt2morse2ultrasound # # version 0.3 # # licence GPL 3.0 # # A simple demo of leaking data out the speakers in ultrasound morse # On a Debian variant of Linux do: # apt-get install morsegen # xset -led named 'Scroll Lock' INPUT="$1" # test if file name supplied [ $# -eq 0 ] && { echo "Usage: $0 filename"; exit 1; } # test if file exits else warn and exit [ ! -f $INPUT ] && { echo "$0: file $INPUT not found."; exit 2; } # get our file contents as morse ( . -) after converting to hexadecimal to allow any values or chars. m=`cat $INPUT | hexdump -v -e '/1 "%02X"' | morsegen -` # loop through morse sequence for character and toggle LED for (( i=0; i<${#m}; i++ )); do mm=${m:$i:1} case "$mm" in '.') play -q -n synth .005 sine 20500 ;; '-') play -q -n synth .015 sin 21000 ;; ' ') sleep .03 ;; esac doneSome of the comments in the above code are from the previous incarnation which was just for morse on the scroll lock indicator LED, but anyway you get the idea, not much to it realy.
I did this on school laptops in 6th grade. They were blocking lots of sites so I convinced my classmates to run my program that formed a mesh network communicating over ultrasound with laptop speakers and microphones. It was pretty low bandwidth, as you’d imagine, not only because the speakers could only go a few thousand hertz into the ultrasound range. An interesting side effect is that because the lower end of the frequency range I used was about the Mosquito Tone, us kids with young ears could hear messages being transmitted, but not the teachers.
https://github.com/milkey-mouse/UDT
https://hackaday.com/2020/05/11/side-channel-attack-turns-power-supply-into-speakers
This related attack was already covered. As Mikey Mouse says above, this is an old technique that keeps getting re-discovered, part of a family that goes all the way back to at least Van Eck.
The moral of the story: if spies want your data *REALLY* bad, your only solution is unpowered, in a safe with armed guards outside! It’s why TEMPEST-qualified stuff costs so much (besides the obligatory “add a few zeros”).
Libquiet/quietjs have been able to do this for years.
Sound is about all we have for air-gap. Some years ago, there was a PoC using the systems fans to transmit data. https://youtu.be/v2_sZIfZkDQ