 If all you want is just a basic WiFi extender that gets some level of network connectivity to remote parts of your domicile, then it might be tempting to get some of those $5, 300 Mbit extenders off Temu as [Low Level] recently did for a security audit. Naturally, as he shows in the subsequent analysis of its firmware, you really don’t want to stick this thing into your LAN. In this context it is also worrying that the product page claims that over a 100,000 of these have been sold.
If all you want is just a basic WiFi extender that gets some level of network connectivity to remote parts of your domicile, then it might be tempting to get some of those $5, 300 Mbit extenders off Temu as [Low Level] recently did for a security audit. Naturally, as he shows in the subsequent analysis of its firmware, you really don’t want to stick this thing into your LAN. In this context it is also worrying that the product page claims that over a 100,000 of these have been sold.
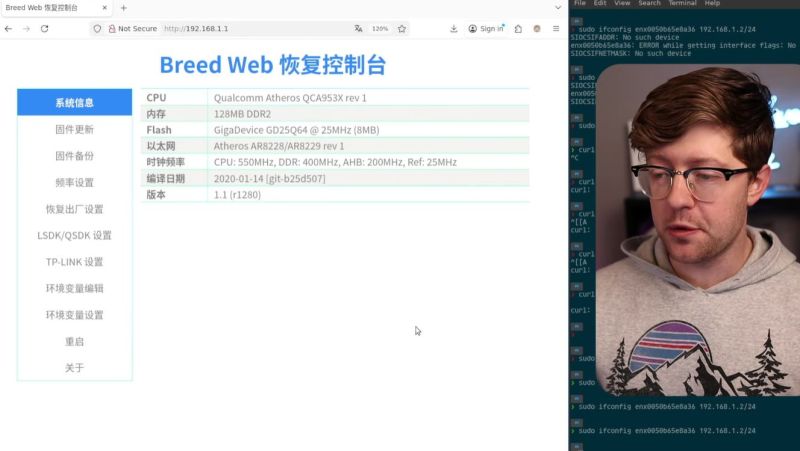
Starting the security audit is using $(reboot) as the WiFi password, just to see whether the firmware directly uses this value in a shell without sanitizing. Shockingly, this soft-bricks the device with an infinite reboot loop until a factory reset is performed by long-pressing the reset button. Amusingly, after this the welcome page changed to the ‘Breed web recovery console’ interface, in Chinese.
Here we also see that it uses a Qualcomm Atheros QCA953X SoC, which incidentally is OpenWRT compatible. On this new page you can perform a ‘firmware backup’, making it easy to dump and reverse-engineer the firmware in Ghidra. Based on this code it was easy to determine that full remote access to these devices was available due to a complete lack of sanitization, proving once again that a lack of input sanitization is still the #1 security risk.
In the video it’s explained that it was tried to find and contact a manufacturer about these security issues, but this proved to be basically impossible. This leaves probably thousands of these vulnerable devices scattered around on networks, but on the bright side they could be nice targets for OpenWRT and custom firmware development.















I really can’t understand someone wanting to conume a ‘security analysis’ as a youtube video. Anyways, there’s always the risk of it becoming part of a botnet, but the disclosures in the hackaday article don’t bother me at all, right? Someone gets access to the admin page and then can own the device…first, duh? Second, yay! I love how cheaper imported Chinese devices are almost never locked down!
For the exploit in the post, you actually need to be authenticated as Admin already. So it is more of a happy jailbreak opportunity than a regrettable flaw.
But it is a “code smell” that suggests there are bigger concerns lurking elsewhere.
The video kept going 14 minutes beyond that so I have no idea if he found serious issues later.
Sometimes it’s interesting to see the process.
The headline should be changed though. “Cheapo” is faux Spanish, a shorter form of the more obvious “el-cheapo”, a stereotype about poor quality goods from Mexico and the like.
I’m 66 years old and have never before encountered the idea that Cheapo is a slur against Mexico. I think the word has pretty much become part of the English language without ethnic meaning.
“Old,” in the manner you just used it, is an age-ist slur. This is a bad look for a virtue-signaler. Looking forward to the post where you express disgust with yourself.
I guess we need to be more sensitive about words like hobo, homo, gestapo, banjo, piano, lotto, to name a few. You just never know how someone from Mexico might take it.
We don’t mean anything like that, of course — and the product isn’t from Mexico anyway. We certainly hope nobody is offended.
It’s harmless to change the title, so we did.
I’d guess the only reason for this needing even cursory security is that it has an Ethernet port. If its just used as a repeater then there’s not a whole lot you can do with it — except use it as a repeater. If you want to hack it then you could just for fun but since just about every processor board on today’s market has a wireless interface there’s lots of cheap platforms for you play with (and they likely all use the same chipset/driver combo).
It’s got wifi, so anyone nearby can exploit security issues.
As it’s a device which you give logical access to your network, I’d be a bit more careful than just buying random gadgets like these. But as for the severity, the exploit shown is a neat way to get root, but not yet something which can be exploited over the internet.
fundamentally it can’t do anything but send packets on your local wifi network, which, in order to exploit it, you must already have that ability (more or less). Which seems like it’s not an escalation, but…the threat can go away, and the device can keep sending packets. So that’s the potential escalation. A temporary packet source can escalate to a permanent one.
(i don’t care about it and i think it’s a feature not a bug, but)
I love these cheap QCA953x devices, it’s easy to put mainline openwrt on it which I did a few years ago here (although I did not update for a while): https://github.com/biemster/funpeater-openwrt.
These were covered earlier on these pages as well https://hackaday.com/2024/09/05/getting-root-on-cheap-wifi-repeaters-the-long-way-around/, and have an even earlier project on had.io: https://hackaday.io/project/192859-fun-with-wifi-repeaters.
How much RAM and storage does it have? I just bought one at a thrift store for $6. No firmware download URL on the device, box, or instruction sheet.
breed author: https://blog.hackpascal.net/
breed code releases: https://breed.hackpascal.net/
breed is, aparently a recovery tool for openwrt. https://openwrt.org/docs/guide-user/installation/recovery_methods/breed_web_recovery
Memories from the cheap Zsun device exploit with
rebootas ESSID:http://www.zoobab.com/zsun-sd11x-wifi-card-reader
There was even a HaD article about it:
https://hackaday.com/2016/01/27/cheap-wifi-devices-are-hardware-hacker-gold/