You probably don’t think about it much, but your PC probably has a TPM or Trusted Platform Module. Windows 11 requires one, and most often, it stores keys to validate your boot process. Most people use it for that, and nothing else. However, it is, in reality, a perfectly good hardware token. It can store secret data in a way that is very difficult to hack. Even you can’t export your own secrets from the TPM. [Remy] shows us how to store your SSH keys right on your TPM device.
We’ll quote [Remy] about the advantages:
The private key never leaves the device, you yourself can’t even extract it, neither can malware. It does not live on your filesystem or in an ssh-agent (in memory)…
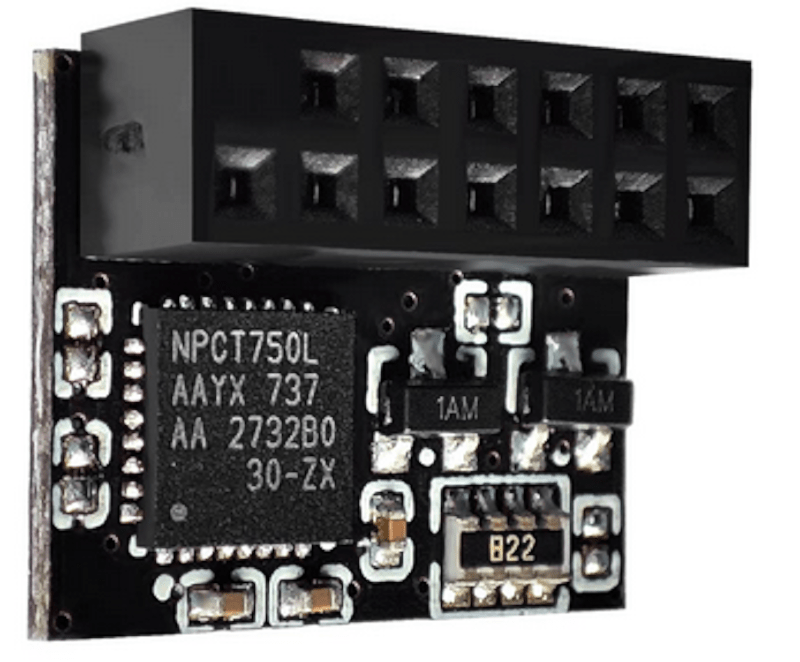
Unlike a hardware token, the TPM is locked to your machine. In fact, in many cases, it is soldered onto the motherboard, although sometimes it is plugged in. The post notes that because of this, the TPM is not quite as secure as a hardware token that you can pull out of a USB port and lock up. But it is still more secure than just having your keys sitting on a hard drive.
One caveat: some computers wipe your TPM when you update the BIOS. The post mentions how to get around this. You’ll need some tools, of course, and it won’t work with Windows Subsystem for Linux, unsurprisingly. Once you have the tools installed, the process is pretty straightforward.
We’ll add this to our set of ssh tricks from now on.















There are quite a few free and open source HSMs you can build yourself for cheaper and that offer more safety (removable, USB form factor) that cannot be extracted either and have not 4 extra dependencies and work on stock packages of Debian and Ubuntu.
such as? sounds great in theory, but if it’s a network appliance + USB form factor…
being able to store in TPM seems to have its own advantages, despite not being appropriate for 100% of high-security scenarios. there’s always a balance of security and convenience/pragmatism.
Finally, a sane reason to have a TPM! Full disk encryption always struck me as a bit paranoid, signed bootloaders as DRM, but this seems more like a reasonable precaution.
Windows 11 copies protected keys into the cloud, and Intel management engine also has a access to the area. Best of luck with that…
Curious as to how this could work on windows. Maybe adding support in to putty cac’s agent?
TPM offers mostly an illusion of security. Since its specification and actual chips are made in the US, it’s 100% likely they are backdoored by the NSA.
Shall come the need for me to ever visit the US (which is VERY unlikely) I’d only do this with laptop using an Elbrus CPU because it offers actual security and privacy against government-mandated snoopage.
Remembmer. The man who gives up his rights saying that he has nothing to hide is the man who became an eunuch and has no rights anymore. الموت لأمريكا. الموت لإسرائيل.
The TPM in the image is from Nuvoton, a Taiwanese company.
I’ve used TPMs (in boards of my own design) from STMicroelectronics, a European company. Those TPMs were designed in India.
Companies such as Microchip design and make TPMs in USA.
Yeah the GRU is much more cool about things lol…. They have never spied on their own people nor do they have nearly every wifi in their pocket. The good news is they are pretty busy right now and probably can’t get to you at the moment.
I just want that black plastic bit for model greebles
once again the lack of accuracy in the article, I have to play a game of malice or incompetence: the quote you have is not even remotely related to TPMs but HSMs, which a TPM is not,
the key material is loaded at run time and stored at rest encrypteed on the harddrive of the computer, only crypto functions are handled by the TPM, it’s basically a glorified crypto accelerator.
this doesn’t really provide any coverage, and you’d be better off just forking out $50USD for a yubikey or similar device