You probably don’t think about it much, but your PC probably has a TPM or Trusted Platform Module. Windows 11 requires one, and most often, it stores keys to validate your boot process. Most people use it for that, and nothing else. However, it is, in reality, a perfectly good hardware token. It can store secret data in a way that is very difficult to hack. Even you can’t export your own secrets from the TPM. [Remy] shows us how to store your SSH keys right on your TPM device.
TPM13 Articles
Embedded TPM: Watch Out!
Today’s PCs are locked up with Trusted Platform Module (TPM) devices so much so that modern Windows versions insist on having a recent TPM to even install. These have become so prevalent that even larger embedded boards now have TPM and, of course, if you are repurposing consumer hardware, you’ll have to deal with it, too. [Sigma Star] has just the primer for you. It explains what TPM does, how it applies to embedded devices, and where the pitfalls are.
The TPM is sometimes a chip or sometimes secure firmware that is difficult to tamper with. They provide secret storage and can store boot signatures to detect if something has changed how a computer starts up. The TPM can also “sign off” that the system configuration is the same to a remote entity. This allows, for example, a network to prevent a hacked or rogue computer from communicating with other computers.
Embedded systems, usually, aren’t like PCs. A weather station at a remote location may have strangers poking at it without anyone noticing. Also, that remote computer might be expected to be working for many more years than a typical laptop or desktop computer.
This leads to a variety of security concerns that TPM 2.0 attempts to mitigate. For example, it is unreasonable to think a typical attacker might connect a logic analyzer to your PC, but for an embedded system, it is easier to imagine. There is a session-based encryption to protect against someone simply snooping traffic off the communication bus. According to the post, not all implementations use this encryption, however.
Motherboard has a slot for TPM, but no board? We’ve seen people build their own TPM boards.
Title image by [] CC BY-SA-4.0
Forced E-Waste PCs And The Case Of Windows 11’s Trusted Platform
Until the release of Windows 11, the upgrade proposition for Windows operating systems was rather straightforward: you considered whether the current version of Windows on your system still fulfilled your needs and if the answer was ‘no’, you’d buy an upgrade disc. Although system requirements slowly crept up over time, it was likely that your PC could still run the newest-and-greatest Windows version. Even Windows 7 had a graphical fallback mode, just in case your PC’s video card was a potato incapable of handling the GPU-accelerated Aero Glass UI.
This makes a lot of sense, as the most demanding software on a PC are the applications, not the OS. Yet with Windows 11 a new ‘hard’ requirement was added that would flip this on its head: the Trusted Platform Module (TPM) is a security feature that has been around for many years, but never saw much use outside of certain business and government applications. In addition to this, Windows 11 only officially supports a limited number of CPUs, which risks turning many still very capable PCs into expensive paperweights.
Although the TPM and CPU requirements can be circumvented with some effort, this is not supported by Microsoft and raises the specter of a wave of capable PCs being trashed when Windows 10 reaches EOL starting this year.
Continue reading “Forced E-Waste PCs And The Case Of Windows 11’s Trusted Platform”
Beating Bitlocker In 43 Seconds
How long does it take to steal your Bitlocker keys? Try 43 seconds, using less than $10 in hardware. Encrypting your hard drive is good security. If you’re running Windows, the most popular system is BitLocker, which has come with Windows since Vista. We’ve known for some time that Bitlocker could be defeated with direct access to the hardware. Microsoft claims that the process requires an attacker with skill and lengthy access to the hardware. [Stacksmashing] wanted to define lengthy, so he gave it a try. The result is a shockingly fast attack.
Anyone who uses Windows has probably run into Bitlocker. Your hard drive is encrypted, and Bitlocker runs silently in the background, decrypting data on demand. The problem is key storage. In a simplified sense, encryption keys are stored in the Trusted Platform Module (TPM). When your computer boots, it reads the key from the TPM over the LPC (low pin count) bus, which is one of the last remnants of the original ISA bus.
This Week In Security: Not A Vulnerability, BGP Bug Propogation, And Press Enter To Hack
Curl was recently notified of a CVE, CVE-2020-19909, rated at a hair-raising 9.8 on the CVSS scale. And PostgreSQL has CVE-2020-21469, clocking in with a 7.5 severity. You may notice something odd about those two vulnerabilities, but I promise the 2020 date is only the tip of the iceberg here.
Let’s start with PostgreSQL. That vulnerability was only present in version 12.2, which released in February of 2020, and was fixed with the 12.3 release in May of that same year. The problem is a stack buffer overflow, which doesn’t seem to enable code execution, but does cause a denial of service situation. To trigger the bug? Repeatedly send the PostgreSQL daemon the SIGHUP signal.
If you’re familiar with Linux signals, that might sound odd. See, the SIGHUP signal technically indicates the end of a user session, but most daemons use it to indicate a restart or reload request. And to send this signal, a user has to have elevated privileges — elevated enough to simply stop the daemon altogether. Put simply, it’s not a security vulnerability, just a minor bug.
And now on to curl — This one is just bizarre. The issue is a integer overflow in the --retry-delay argument, which specifies in seconds how often curl should retry a failing download. The value is multiplied by 1000 to convert to milliseconds, resulting in an overflow for very large values. The result of that overflow? A smaller value for the retry delay.
[Daniel Stenberg] makes the point that this tale is a wonderful demonstration of the brokenness of the CVE system and NVD’s handling of it. And in this case, it’s hard not to see this as negligence. We have to work really hard to construct a theoretical scenario where this bug could actually be exploited. The best I’ve been able to come up with is an online download tool, where the user can specify part of the target name and a timeout. If that tool had a check to ensure that the timeout was large enough to avoid excess traffic, this bug could bypass that check. Should we be assigning CVEs for that sort of convoluted, theoretical attack?
But here’s the thing, that attack scenario should rate something like a CVSS of 4.8 at absolute worst. NVD assigned this a 9.8. There’s no way you can squint at this bug hard enough to legitimately rank it that severe. At the time of writing, the NVD lists this as “UNDERGOING REANALYSIS”.
Continue reading “This Week In Security: Not A Vulnerability, BGP Bug Propogation, And Press Enter To Hack”
Bypassing Bitlocker With A Logic Analzyer
Security Engineer [Guillaume Quéré] spends the day penetration testing systems for their employer and has pointed out and successfully exploited a rather obvious weakness in the BitLocker full volume encryption system, which as the linked article says, allows one to simply sniff the traffic between the discrete TPM chip and CPU via an SPI bus. The way Bitlocker works is to use a private key stored in the TPM chip to encrypt the full volume key that in turn was used to encrypt the volume data. This is all done by low-level device drivers in the Windows kernel and is transparent to the user.
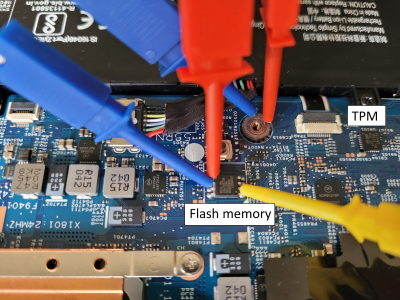
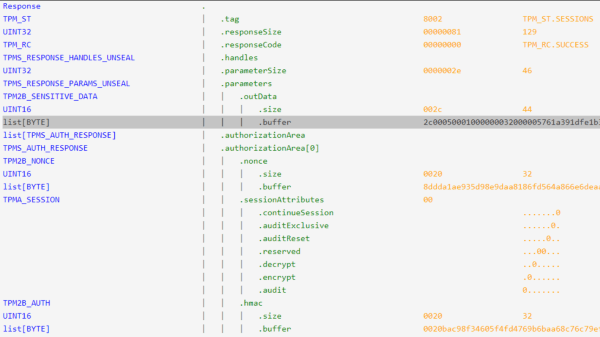
The whole point of BitLocker was to prevent access to data on the secured volume in the event of a physical device theft or loss. Simply pulling the drive and dropping it into a non-secured machine or some other adaptor would not provide any data without the key stored by the TPM. However, since that key must pass as plaintext from the TPM to the CPU during the boot sequence, [Guillaume] shows that it is quite straightforward — with very low-cost tools and free software — to simply locate and sniff out this TPM-to-CPU transaction and decode the datastream and locate the key. Using little more than a cheapo logic analyser hooked up to some conveniently large pins on a nearby flash chip (because the SCK, MISO, and MOSI pins are shared with the TPM) the simple TIS was decoded enough to lock onto the bytes of the TPM frame. This could then be decoded with a TPM stream decoder web app, courtesy of the TPM2-software community group. The command to look for is the TPM_CC.Unseal which is the request from the CPU to the TPM to send over that key we’re interested in. After that just grabbing and decoding the TPM response frame will immediately reveal the goods.
Continue reading “Bypassing Bitlocker With A Logic Analzyer”
This Week In Security: TPM And BootGuard, Drones, And Coverups
Full disk encryption is the go-to solution for hardening a laptop against the worst-case scenario of physical access. One way that encryption can be managed is through a Trusted Platform Module (TPM), a chip on the motherboard that manages the disk encryption key, and only hands it over for boot after the user has authenticated. We’ve seen some clever tricks deployed against these discrete TPMs, like sniffing the data going over the physical traces. So in theory, an integrated TPM might be more secure. Such a technique does exist, going by the name fTPM, or firmware TPM. It uses a Trusted Execution Environment, a TEE, to store and run the TPM code. And there’s another clever attack against that concept (PDF).
It’s chip glitching via a voltage fault. This particular attack works against AMD processors, and the voltage fault is triggered by injecting commands into the Serial Voltage Identification Interface 2.0 (SVI2). Dropping the voltage momentarily to the AMD Secure Processor (AMD-SP) can cause a key verification step to succeed even against an untrusted key, bypassing the need for an AMD Root Key (ARK) signed board firmware. That’s not a simple process, and pulling it off takes about $200 of gear, and about 3 hours. This exposes the CPU-unique seed, the board NVRAM, and all the protected TPM objects.
So how bad is this in the real world? If your disk encryption only relies on an fTPM, it’s pretty bad. The attack exposes that key and breaks encryption. For something like BitLocker that can also use a PIN, it’s a bit better, though to really offer more resistance, that needs to be a really long PIN: a 10 digit PIN falls to a GPU in just 4 minutes, in this scenario where it can be attacked offline. There is an obscure way to enable an “enhanced PIN”, a password, which makes that offline attack impractical with a secure password.
And if hardware glitching a computer seems to complicated, why not just use the leaked MSI keys? Now to be fair, this only seems to allow a bypass of Intel’s BootGuard, but it’s still a blow. MSI suffered a ransomware-style breach in March, but rather than encrypt data, the attackers simply threatened to release the copied data to the world. MSI apparently refused to pay up, and source code and signing keys are now floating in the dark corners of the Internet. There have been suggestions that this leak impacts the entire line of Intel processors, but it seems likely that MSI only had their own signing keys to lose. But that’s plenty bad, given the lack of a revocation system or automatic update procedure for MSI firmware. Continue reading “This Week In Security: TPM And BootGuard, Drones, And Coverups”