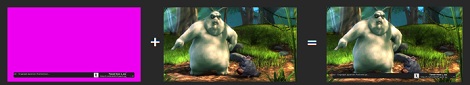
[bunnie] is up to his old tricks again. He successfully implemented a man-in-the-middle attack on HDCP-secured connections to overlay video in any HDMI video stream. There’s a bonus, too: his hack doesn’t use the HDCP master-key. It doesn’t violate the DMCA at all.
HDCP is the awful encryption scheme that goes into HDMI-compatable devices. Before HDCP, injecting video overlays or even chroma keying was a valid interpretation of fair use. [bunnie] thinks that HDMI devices should have the same restrictions analog devices have, so he decided to funnel his own video into his TV.
The build uses the NeTV, a handy and cheap FPGA board with an HDMI input and output. [bunnie] got the FPGA to snoop the HDMI bus and decide if a pixel needs to be changed or not. This isn’t much different from what researchers in Germany did a few months ago, but unlike the academic security researchers, [bunnie] gives you a shopping list of what to buy.
As an example of his work, [bunnie] implemented something like a ‘tweet ticker’ on HDCP-encrypted video. There’s very little the NeTV setup can’t do from chroma keying, filters, or simply dumping the HDMI stream to a hard disk. Check out the slides from [bunnie]’s talk to get better idea of what he did.
[PAPPP] found a video of the talk in question. Check that out after the break.
[youtube=http://www.youtube.com/watch?v=37SBMyGoCAU&w=470]














Just throwing it out there, not only a shopping list, you can buy the thing too https://www.adafruit.com/products/609
Yeah I missed that link my bad. The wording made me think it was a BOM, so i didnt bother to click it till after the post.
Actually, IIRC it _does_ use the master key, but it _never_ decrypts the incoming pixels, only re-encrypts the replaced pixels.
That means no alpha-blending between the injected video and the original, but also that this cannot be declared circumvention of copyright.
Also, bunnie didn’t just _use_ the NeTV, he (and a team) _created_ the device specifically for this purpose.
Check out his 28c3 talk: http://www.youtube.com/watch?v=37SBMyGoCAU
>There’s a bonus, too: his hack doesn’t use the
>HDCP master-key
this hack DOES USE master key and DOES violate DMCA, ift would help to READ the slides before publishing Brian.
This article completely misunderstands the point of this project. Part of why this project is awesome is because it *requires* the HDCP master key, which means that, and I quote from the abstract you linked to, “Significantly, the attack enables forging of video data without decrypting original video data, so executing the attack does not constitute copyright circumvention. Therefore, this novel and commercially useful application of the HDCP master key impairs equating, in a legal sense, the master key with circumvention. ”
I can’t see how this could be any more clear. This project means that distribution of the HDCP master key is not illegal because it is not clear that the only use of the HDCP master key is to circumvent copyright. The project doesn’t violate the DMCA in the sense that distribution of the master key has a legal defense now.
As usual, the typical Internet-lawyering disclaimers apply. I am not a lawyer, nor do I play one on TV. No legal counsel is intended by the above message.
It’s a little clearer in the video of the talk (or the text preceding the slides at the first link…), but it DOES use the HDCP master key. It is, however, designed very specifically to use it in a way which is NOT technically infringing under the DMCA – part of the point of the hack is to establish a substantial non infringing use for the master key.
i thought the DMCA and use of the encryption keys only causes trouble when trying to sell the equipment
This is an amazing and important hack and Adafruit is selling some pretty powerful hardware for a reasonable price to play with this.
@biozz – it also includes some efforts of intentionally reverse-engineering an encryption mechanism [and publishing the results].
Snatched up an NeTV from Adafruit the day they were available – mines sitting in its box waiting for me to play with it. gonna be fun!
never bought a blu-ray, never will I expect.
but unfortunately they use that HDCP crap left and right even when you’ve never been near a blu-ray.
Now this is a hack!
I’m just disappointed that the article didn’t write anything about the board he uses.
Did it make it himself? only for this application? Will it be open hardware? Will he provide the dev tools to use it in another context?
I’m wondering why this gets posted just now, s’if we didn’t all watch the 28c3 live :>
So does this mean it can be used for an ambilight clone? I thought the NeTV had been written off because it passes some of the hdmi connections straight through?
This cannot be used for ambilite as implemented because it does not decrypt the input video. There is enough information in the source to change this into an HDCP decrypter, but you would still need to have a way of buffering the large amount of data, downscaling it to something usable for ambilight, and spitting it out to a string of GE Color Effects.
I’m going to go ahead and say that’s actually not too difficult. You don’t need fancy scaling, just take a couple samples from each region and average them. The hard part is decrypting the HDMI and keeping it within the size constraints of that FPGA.
so when is the Internal Architecture /source for the FPGA, going to be released?
http://www.kosagi.com/w/index.php?title=NeTV_FPGA_architecture
and
http://sutajiokousagi.com/netv_hardware/
the file you want is under ./fpga
So can you read HDMI data that way? Or only change pixels to something else? If reading is possible then we can finally build that LED set that makes the wall behind any tv glow with the colors of TV’s image
Hmmm, this and a public place, and you could have some fun with a fake news ticker XD Maybe a tornado warning…
I just thought that it would be easier and more fun to hack a Google TV (Logitech Revue) box to do this. They used to go for as low as $80. Since it is clear that the Revue can overlay over protected HDMI signal from the cable box to add its own content.
The 45 min video is worth your time.
I think his presentation slightly mischaracterizes HDCP in that this device could be made completely without the HDCP master key, but would require an HDMI license and HDCP license. There is nothing in either of those licenses that prevents him from doing this the ‘right’ way. In fact if he did have those licenses he wouldn’t have to jump through so many hoops, and could just do the overlay, including true alpha layer by handing in the clear video data, the re-encrypt with a new key on the way out.
So it seems to me that this is more of a technique to avoid license fees, and a novel one at that!
Paying a licence might be reasonable if you want to make use of HDCP to protect your content, but if you don’t then why should you need to pay a licence fee in order to provide your own content to your own tv?
does this allow recording or displaying on non compliant devices?
bump