[AndrewMohawk] had seen all kinds of ambient lighting systems for TVs come and go over the years, and the one thing they all had in common was that they didn’t live up to his high standards. Armed with the tools of the hacker trade, he set about building an Ambilight-type system of his own that truly delivered the goods.
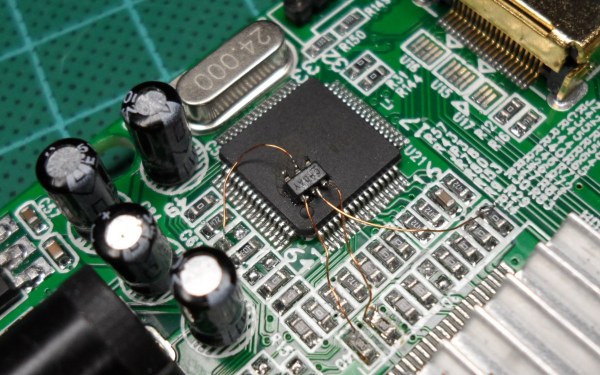
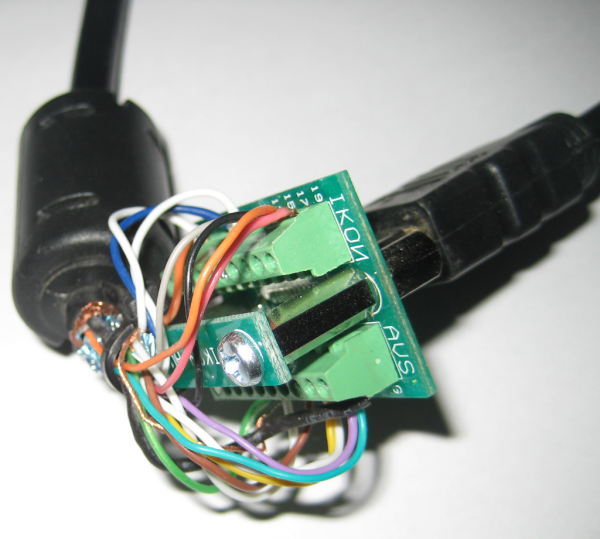
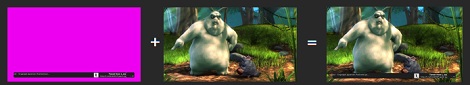
The development process was one full of roadblocks and dead ends, but [Andrew] persevered. After solving annoying problems with HDCP and HDMI splitters, he was finally able to get a Raspberry Pi to capture video going to his TV and use OpenCV to determine the colors of segments around the screen. From there, it was simple enough to send out data to a string of addressable RGB LEDs behind the TV to create the desired effect.
For all the hard work, [Andrew] was rewarded with an ambient lighting system that runs at a healthy 20fps and works with any HDMI video feed plugged into the TV. It even autoscales to work with video content shot in different aspect ratios so the ambient display always picks up the edge of the video content.
With 270 LEDs fitted, the result is an incredibly smooth and fluid ambient display we’d love to have at home. You can build one too, since [Andrew] shared all the code on Github. As an added bonus, he also gave the system an audio visualiser, and tested it out with some Streetlight Manifesto, the greatest third-wave ska band ever to roam the Earth. The Fourth Wave still eludes us, but we hold out hope.
We’ve seen plenty of hacks in this vein before; one of the most impressive hacked a smart TV into doing the video processing itself. Video after the break.
Continue reading “TV Ambient Lighting Built For Awesome Performance”