Even the most well designed crypto algorithms can be broken if someone is smart enough to connect an oscilloscope to a processor. Over the last 15 years or so, an entire domain of embedded security has cropped up around the techniques of power and side channel analysis. The tools are expensive and rare, but [Colin O’Flynn] and the ChipWhisperer are here to bring a new era of hardware security to the masses.
The ChipWhisperer was the second place winner of last year’s Hackaday Prize. It’s an interesting domain of security research, and something that was previously extremely expensive to study. If you’re looking for a general overview of what the ChipWhisperer does, you might want to check out when we bumped into [Colin] at DEFCON last year.
While the original goal of the ChipWhisperer was to bring the cost of the tools required for power and side channel analysis down to something a hackerspace or researcher could afford, this was still too expensive for a Kickstarter campaign. To that end, [Colin] designed the ChipWhisperer Lite, a cut-down version, but still something that does most of what the original could do.
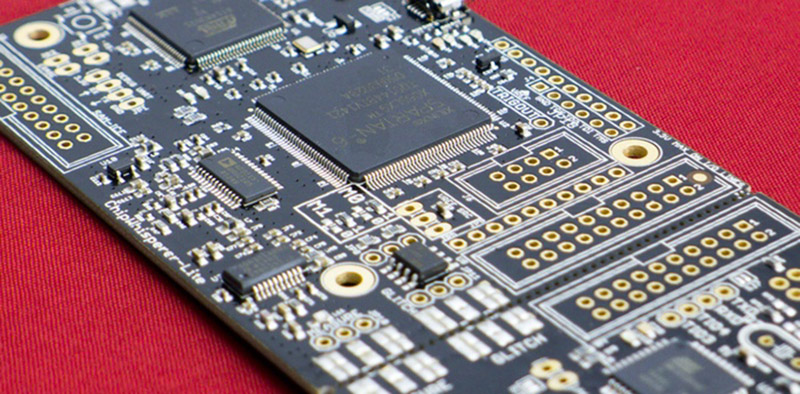
There are two parts to the ChipWhisperer Lite – the main section contains a big microcontroller, a big FPGA, and a high gain, low noise amplifier. This is the core of the ChipWhisperer, and it’s where all the power analysis happens. The other part is a target board containing an XMega microcontroller. This is where you’ll run all your encryption algorithms, and where you’ll find out if they can be broken by power analysis. The main board and target board are held together by a break-away connection, so if you want to run a power analysis on another board, just snap the ChipWhisperer in half.
[Colin] is offering up a ChipWhisperer Lite for around $200 USD – far, far less than what these tools cost just a year ago. We’re looking forward to a successful campaign and all the neat findings people with this board will find.















Shouldn’t that read “a new era of hardware insecurity to the masses”?
It certainly lowers the financial barrier for using such attacks.
potato, potato.
wait. That doesn’t work as text.
Tomato, tomato.
“Even the most well designed crypto algorithms can be broken”
I don’t believe this is true, the evidential case is publicly distributed algorithms, of which there are many.
People can know how public key encryption works, for example, but it knowing how it works still doesn’t help you break it without the private key (for example), discounting of course any brute-forcing methods (using computers that we do not have yet).
I don’t think they are talking about “breaking” the algorithms, they are peeking inside the silicon “virtually” to see the decoded data running on the internal data bus. Older systems like this (cable boxes unless I’m mistaken) have been cracked because the whole circuit would not fit on one chip so they had to send the data unencrypted between two chips. Nowadays they can fit the entire circuit on one chip, so decrypted data never leaves the chip, but it is present on the chip as signals, so it should be possible to detect these signals.
The point of the board is to use side-channel attacks to extract the private key. It’s not breaking the encryption per-se.
Suppose your processor emits a known, small packet of heat energy for each bit of each operation. Further, suppose that you have a sensitive thermometer that can measure the heat output of the CPU.
Using this method, and doing the decryption operation many times and averaging the results, you can infer some of the data used in some of the paths of the decryption algorithm. Do this enough times, and in enough ways, and you can reduce the search space of possible private keys.
For example, you might be able to measure the temperature of the CPU and infer the number of 1’s and 0’s in the register at a particular point in the algorithm.
I think the value of this project will be to crack DRM schemes. My friend has a Cubify 3d printer with chipped filament cartridges which cost several times more than raw filament. I looked into breaking the encryption using one of these boards to see if it was a worthwhile endeavor – for me it wasn’t, but someone with more time and more motivation could have a small business selling cartridges that bypass the DRM.
This board would allow them to do that.
As companies start to embed security in their IoT products, there will be a market for systems that can bypass the DRM. Crack and publish the Blue-Ray DVD keys, or crack the inkjet printer cartridge chips, or crack the *whatever* security that locks your product to an account on the manufacturer’s website.
As others have stated, the side-channel power analysis attacks capture information that is unavoidably leaked simply because of the laws of physics, which is then correlated and turned into something meaningful. The example of publicly distributed algorithms is not an evidential case of anything to do with this attack.
Here’s a short excerpt from wikipedia:
Power analysis provides a way to “see inside” otherwise ‘tamperproof’ hardware. For example, DES’s key schedule involves rotating 28-bit key registers. Many implementations check the least significant bit to see if it is a 1. If so, the device shifts the register right and prepends the 1 at the left end. If the bit is a zero, the register is shifted right without prepending a 1. Power analysis can distinguish between these processes, enabling an adversary to determine the bits of the secret key.
I imagine this side channel power analysis attack is the equivalent of van eck phreaking, but on a smaller scale.
Amazing project but why using those ATMEL SAM3U MCU (or XMEGA ..) when NXP LPC43xx or STM32 are so better …
Its somewhat religious matter
Im same way with PICs, and silverlight
“you don’t save too much going DIY, but some people like to be difficult.”
Wow! This is _really_ impressive stuff. I wish I had the necessary knowledge to play with such equipment…
Breaking AES in 120 seconds: https://www.youtube.com/watch?v=3RK5J6MgjgA
Hats off!
Eh. His work, while extensive, isn’t really that impressive.
Please post links to yours.