It’s been said that hackers are enamored with complex networks. In the 60s and 70s, the telephone network was the biggest around, singing a siren song to an entire generation of blue-boxing phone phreaks. I started a bit closer to the house. As a child I was fascinated by the heating system in the basement of our home: a network of pipes with a giant boiler in the middle. It knew when to come on to provide heat, and when to kick on for hot water. I spent hours charting the piping and electrical inputs and outputs, trying to understand how everything worked. My parents still tell stories of how I would ask to inspect the neighbors heating systems. I even pestered the maintenance staff at my nursery school until they finally took me down to see the monstrous steam boiler which kept the building warm.
It’s been said that hackers are enamored with complex networks. In the 60s and 70s, the telephone network was the biggest around, singing a siren song to an entire generation of blue-boxing phone phreaks. I started a bit closer to the house. As a child I was fascinated by the heating system in the basement of our home: a network of pipes with a giant boiler in the middle. It knew when to come on to provide heat, and when to kick on for hot water. I spent hours charting the piping and electrical inputs and outputs, trying to understand how everything worked. My parents still tell stories of how I would ask to inspect the neighbors heating systems. I even pestered the maintenance staff at my nursery school until they finally took me down to see the monstrous steam boiler which kept the building warm.
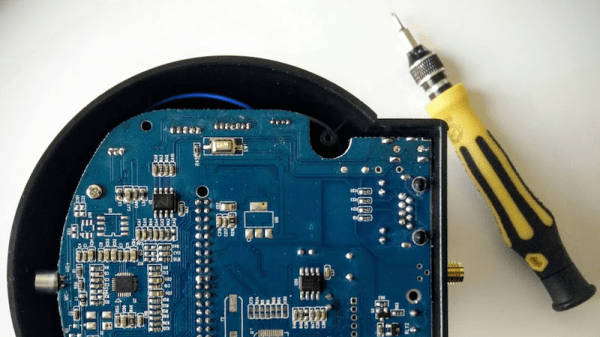
My family was sure I would grow up to be a Heating Ventilation and Air Conditioning (HVAC) tech. As it turned out, electronics and embedded systems were my calling. They may not have been too far from the truth though, as these days I find myself designing systems for a major manufacturer of boiler controls and thermostats.
Recently a house hunt led me to do some HVAC research on the web. What I found is that HVAC techs have created a great community on the internet. Tradesmen and women from all over the world share stories, pictures, and videos on websites such as HVAC-Talk and HeatingHelp.
Continue reading “HVAC Techs – Hackers Who Make House Calls”