If you’re reading Hackaday, you’ve almost certainly heard of JTAG. There’s an excellent chance you’ve even used it once or twice to reflash an unruly piece of hardware. But how well do you actually know JTAG? More specifically, do you know how useful it can be when reverse engineering hardware?
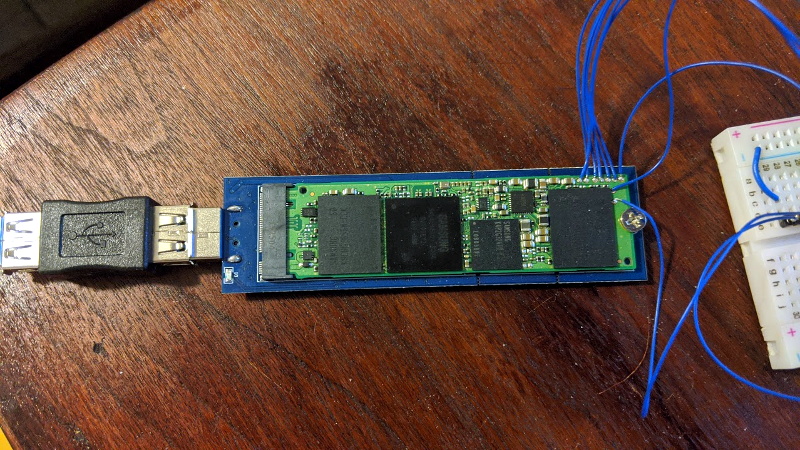
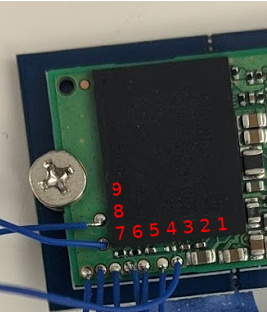 Whether you’re a JTAG veteran or a novice, this phenomenal guide written by [wrongbaud] is sure to teach you a thing or two. Starting with a low-level explanation of how the interface actually works, the guide takes you though discovering JTAG ports on unknown targets, the current state-of-the-art in open source tools to interact with the device, and finally shows a real-world example of pulling and analyzing a gadget’s firmware.
Whether you’re a JTAG veteran or a novice, this phenomenal guide written by [wrongbaud] is sure to teach you a thing or two. Starting with a low-level explanation of how the interface actually works, the guide takes you though discovering JTAG ports on unknown targets, the current state-of-the-art in open source tools to interact with the device, and finally shows a real-world example of pulling and analyzing a gadget’s firmware.
There’s no way to do his write-up justice with a breakdown or a summary, so we won’t even try. Just get comfortable, maybe grab a drink, and dive in. It’s certainly not a short read, but there isn’t a wasted word on the page. Every piece of the puzzle, from how to figure out an unlabeled pinout to determining the instruction length, is explained in exactly the amount of detail you’re looking for. This is a guide for hackers written by a hacker, and it shows.
It will probably come as no surprise to find this isn’t the first time [wrongbaud] has done a deep dive like this. Over the last few months we’ve been covering his series of practical reverse engineering guides, and each one has been an invaluable resource. Perfect study guides for when a global pandemic has you stuck in the house.















JTAGenum.sh is still using sysfs GPIOs, go-jtagenum should be way faster:
https://github.com/gremwell/go-jtagenum
And it is using libgpiod, so not dependent on using an Rpi.
Plus it outputs you if it finds a known manufacturer (there were talks to integrate that feature in Urjtag, don’t know if it is merged or not):
# go-jtagenum -known-pins ‘{ “tdi”: 18, “tdo”: 23, “tms”: 24, “tck”: 25, “trst”: 8 }’ -command test_idcode
================================
Attempting to retreive IDCODE…
devices:
0x0684617f (mfg: 0x0bf (Broadcom), part: 0x6846, ver: 0x0)
0x5ba00477 (mfg: 0x23b (Solid State System Co., Ltd.), part: 0xba00, ver: 0x5)
0x0684617f (mfg: 0x0bf (Broadcom), part: 0x6846, ver: 0x0)
================================
And we are looking for people to help with DirtyJTAG OpenOCD support, there is a repo WIP here:
https://github.com/jeanthom/openocd-dirtyjtag
Very cool, will look into assisting with DirtyJTAG OpenOCD support. Thanks for sharing!
omg, i need more time…
glad that i found this: https://wrongbaud.github.io/writing-a-ghidra-loader/
Nice, most times I’m messing with JTAG I’m following someone elses debricking instructions and it all feels a bit voodoo in that you say the magic incantations and nobody goes into the whats and whys. Ask anything about it and get “It’s on the forum” meaning that if you followed something blow by blow for 6 months, heading down all the same rabbit trails, mentally integrating all the side threads as they appeared in time, read the 3 main threads comparing post date by post date, eventually you’d be able to assemble the 2% actual information vs the 98% noise, red herrings and dead ends. Or even worse it’s posts 4325, 4439 and 5092 you need in some gigathread *glaring in digitalhomes direction* So it’s great to see full summaries of such subjects top to bottom. (Software wanted, time machine forum replay so you can follow a topic as it develops, with everything appearing in chronological sequence.)
Anyway, looking forward to getting stuck into a couple of things, cheap and nasty e-reader and a flaky HDD (need a firmware pull) oh yeah, and installing linux on everything natch :-D
Forum replay….that is actually a really good idea. Maybe include some kind of system to categorize posts so you can distinguish between multiple threads of conversation in a single topic. Allow multiple topics to be included in a replay, perhaps even across sites. Links for important posts. Store only the metadata so you can share the replay with friends.
I haven’t done web programming since PHP5 was new, someone get on this.
The first link in the article has changed to: https://wrongbaud.github.io/posts/jtag-hdd/