Hardware fault injection uses electrical manipulation of a digital circuit to intentionally introduce errors, which can be used to cause processors to behave in unpredictable ways. This unintentional behavior can be used to test for reliability, or it can be used for more nefarious purposes such as accessing code and data that was intended to be inaccessible. There are a few ways to accomplish this, and electromagnetic fault injection uses a localized electromagnetic pulse to flip bits inside a processor. The pulse induces a voltage in the processor’s circuits, causing bits to flip and often leading to unintentional behavior. The hardware to do this is very specialized, but [Pedro Javier] managed to hack a $4 electric flyswatter into an electromagnetic fault injection tool. (Page may be dead, try the Internet Archive version.)
[Pedro] accomplishes this by turning an electric flyswatter into a spark-gap triggered EMP generator. He removes the business end of the flyswatter and replaces it with a hand-wound inductor in series with a small spark gap. Pressing the power button on the modified flyswatter charges up the output capacitor until the developed voltage is enough to ionize the air in the spark gap, at which point the capacitor discharges through the inductor. The size of the spark gap determines the charge that is built up—a larger gap results in a larger charge, which produces a larger pulse, which induces a larger voltage in the chip.
[Pedro] demonstrates how this can be used to produce arithmetic glitches and even induce an Arduino to dump its memory. Others have used electromagnetic fault injection to corrupt SRAM, and intentionally glitching the power supply pins can also be used to access otherwise protected data.


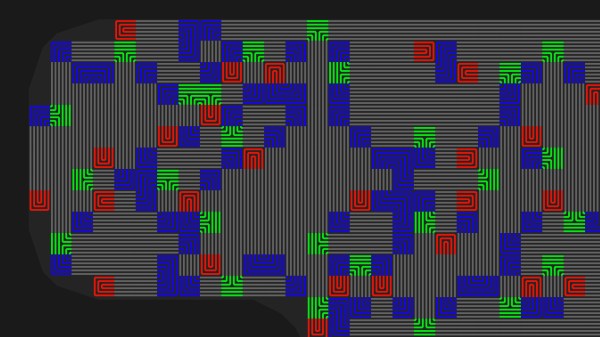
 The idea is pretty simple, place traces very close to one another and it makes it impossible to drill into the case of a device without upsetting the apple cart. There are other uses as well, such as embedding them in adhesives that destroy the traces when pried apart. For [Sebastian’s] experiments he’s sticking with PCBs because of the ease of manufacture. His plugin lays down a footprint that has four pads to begin and end two loops in the mesh. The plugin looks for an outline to fence in the area, then uses a space filling curve to generate the path. This proof of concept works, but it sounds like there are some quirks that can crash KiCad. Consider
The idea is pretty simple, place traces very close to one another and it makes it impossible to drill into the case of a device without upsetting the apple cart. There are other uses as well, such as embedding them in adhesives that destroy the traces when pried apart. For [Sebastian’s] experiments he’s sticking with PCBs because of the ease of manufacture. His plugin lays down a footprint that has four pads to begin and end two loops in the mesh. The plugin looks for an outline to fence in the area, then uses a space filling curve to generate the path. This proof of concept works, but it sounds like there are some quirks that can crash KiCad. Consider 









