This is a cell phone case that can recharge a cellphone using energy captured from its own radio. It’s been featured on dozens of tech blogs, wowed judges at TechCrunch Disrupt, and it’s a Kickstarter Staff Pick. It’s also proof that nearly everyone in the media who claims any knowledge of technology has no idea behind the foundational properties of technology.
What it is
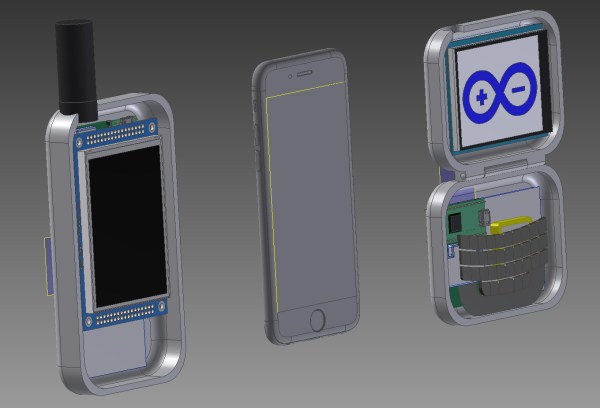
The Nikola Phone Case from Nikola Labs is a very special phone case for the iPhone 6 and Samsung Galaxy S6. The claims behind this cell phone case state it will recharge your battery by capturing radio energy put out by the cell phone itself. This means capturing RF from the WiFi and cellular transmitters. This captured energy is then converted into something that can recharge the phone, is sent to the USB or Lightning port, and – theoretically – the cycle of electrons turning into photons begins again.
Why it’s crap
Astonishingly, this is not a perpetual motion machine, a device that is completely impractical, or an outright fraud. It’s deceptively correct when it comes to the physics of this device, and as always implementation is everything.
Inside each Nikola Phone Case is a small antenna, boost converter, and circuitry to capture the RF energy coming from the phone. This phone case will actually harvest RF energy, but it will never be able to extend the life of the phone’s battery. Nikola Labs claims their phone case will recover 30% of a battery’s life by harvesting RF energy and using that energy to recharge the phone. However, the energy for this RF energy harvesting scheme comes from the phone itself. The captured energy that would – ideally – end up at a cell phone tower or WiFi router will disappear into this cell phone case. This results in both a dramatic decrease in reception and most likely an increase in power draw due to the phone increasing its transmit power.
To Nikola Labs’ credit, the FAQ on their Kickstarter does address concerns that a phone’s transmitter and antenna may be affected:
The device may change the impedance and overall pattern slightly. We are performing detail characterization of these changes, if any.
Nikola Labs has not performed due diligence on their design. There is a method that will report the RSSI of the cellular radio in an Android phone. Any competent engineer would, upon first seeing this device, figure out if signal strength is affected. This can be done in a few dozen lines of Java. It can be done in under an hour by someone who has never programmed an Android device. Nikola Labs does not provide a comparison of the signal strength of a phone both with and without their case. This is evidence of incompetence, if not malice.
Simply by definition, any device that captures RF energy will ‘shadow’ the transmission. Just like putting a solar panel in front of a flashlight, energy will be captured, but the overall light output of the flashlight and solar panel system will decrease. Nikola Labs has an answer to that:
The device harvests the RF energy around the phone, which is usually absorbed by the hand holding the phone.
It is true that the human body will absorb RF coming out of a phone. WiFi works on the same frequencies as a microwave oven, and defrosting a piece of chicken in a microwave isn’t that much different from grabbing an antenna on a router. Lower powers and different geometries aside, you are right now absorbing microwaves from a WiFi router.
The best way of understanding why simply holding a phone isn’t a very big deal is coming at it from the direction of designing a smart phone. One of the biggest drivers behind the design of a cell phone is how long it will last on a single charge. You can design a phone with a powerful CPU and a huge screen, but the battery won’t last long. Likewise, the engineers that design cell phones will put the antennas in an out of the way place, where they won’t be absorbed by the human body. The Nikola Labs case destroys the engineering decisions inside each cell phone. Think about it; if power was wasted inside a cell phone, wouldn’t engineers at Apple and Samsung work to reduce that waste?
Why everything else is crap, too
There is simply no excuse why hundreds of people would give tens of thousands of dollars to a company that makes outrageous claims with zero evidence. One could attribute this to the public’s severe lack of understanding when dealing with electricity or radio. This, in my opinion, is far too kind.
Nikola Labs’ Kickstarter would not exist without the help of Kickstarter itself and members of the tech media. We first heard of Nikola Labs at TechCrunch Disrupt, where four judges could not find anything wrong with this technology. The presentation at Disrupt went on to be covered by Engadget and a flurry of other tech blogs. Now, dozens of other tech blogs have reported on this Kickstarter, and Kickstarter itself has named it a Staff Pick.
Yes, there are stupid people out there. There are people who will throw money at anything. There are also people who will Barnum up the place sell snake oil to rubes. The fact that Kickstarter would endorse something without a technical assessment defies belief. The only conceivable reason this could be a Staff Pick on Kickstarter is because Kickstarter believes it will be funded, thus earning them a percentage of gross.
This is the end of capitalism, folks. No longer do you need to innovate and make a better mouse trap. All you need to do is convince enough people that you’ve made a better mouse trap.




 While we’re not sure that we have the patience to paint our walls this way, it’s a cool effect. But even more, we love the idea of using the cellphone camera for location sensing. Many robotics applications do just this with an overhead camera.
While we’re not sure that we have the patience to paint our walls this way, it’s a cool effect. But even more, we love the idea of using the cellphone camera for location sensing. Many robotics applications do just this with an overhead camera.











