When you’re right, you’re right. Back in January, we predicted that exoskeletons were about to break out as a mainstream product, and gave several examples of prototypes poised to become products. So it was with interest that we read about Sarcos Robotics and their new Guardian XO, a cyber suit aimed at those doing heavy lifting tasks. The wearable, full-body exoskeleton is supposed to amplify the wearer’s effort 20-fold, making a 200-pound load feel like lifting 10 pounds. It runs untethered for two hours on hot-swappable battery packs, and will be offered for lease to civilian heavy industries and the military for $100,000 a year. Honestly, it seems like you could hire a fair number of meat-robots for that sum, but still, it’s an interesting technology and a promising development.
Aficionados of 3D printing know all too well the limitations of the technology. While we’ve come a long way with things like a print in place, multiple materials, embedded electronics, and even direct 3D printing of complex mechanisms like electric motors, there’s been a long-standing obstacle to turning the 3D printer into the replicators of the Star Trek universe: batteries. But even that barrier is falling, and a new paper shows just how far we’ve come to printing batteries right into our designs. Using an off-the-shelf Prusa Mk 3 and specially formulated lithium iron phosphate/PLA and silicon dioxide/PLA filaments, the group was able to print working batteries in one shot. It’s exciting news because previous 3D-printed batteries required special printers or laborious post-processing steps. We’ll be watching for developments here.
Speaking of laboratory work, anyone who has been around labs is probably familiar with LabVIEW, the de facto standard for programming data capture and automation applications in the laboratory setting. The graphical programming language makes it easy to throw together a quick interface, and many lab-rats regret not having the expensive, proprietary environment available for their after-hours hacking. That might no longer be true, though, with special LabVIEW licensing for non-commercial users. It looks like there are two levels: LabVIEW Home Edition and a Community Edition of LabVIEW, which is currently in Beta. Either way, it’s good news for LabVIEW fans.
Friend of Hackaday Eric Strebel released a video the other day that we just had to comment on. It has nothing to do with electronics – unless you’re into circuit sculpture, that is. In the first of a two-part series, Eric covers the basics of modeling with brass and copper, using both wire and tubing. He has some great tips, like work-hardening and straightening copper wire by stretching it, and the miniature roll bender seen at 7:40 looks like something that could easily be 3D-printed. We recently did a Hack Chat on circuit sculpture with Mohit Bhoite, and saw his Supercon talk on the subject, so this video really got the creative juices flowing.
If you’re local to the Elkhorn, Wisconsin area, consider stopping by the Elkhorn Mini Maker Faire on February 15 and 16. Elkhorn looks like it has a nice central location between Milwaukee and Madison, and doesn’t appear too far from Chicago either, which is probably why they drew 1,200 people to the inaugural Faire last year. They’re looking to get that up to 2,000 people this year and over 150 booths, so if you’ve got something hackish to show off, check it out. The organizers have even set up a Hackaday.io event page to coordinate with the Hackaday community, so drop them a line and see what you can do to pitch in.
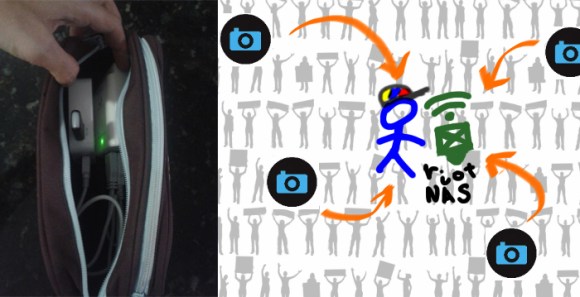
And finally, this one has us scratching our head. Activist group Extinction Rebellion (XR) has claimed they’ve “decommissioned” thousands of electric scooters in French cities. Why they’ve done this is the puzzler; they claim that the scooters-for-hire are an “ecological disaster” due to the resources needed to produce them compared to their short lifespan. We haven’t done the math. What is interesting, though, is the mode of decommissioning: XR operatives simply defaced the QR code on the scooters, rendering them un-rentable with the vendor’s smartphone app. Scooter companies might want to look into alternative rental methods if this keeps up.