We are doing a lot this spring to get people elbow-deep in hardware hacking. We have so many live events coming up that we’re going to be doing Saturday morning recaps to keep you informed. Here are the upcoming events should be planning to attend if you’re nearby.
 Today! NYC Hardware Hackathon
Today! NYC Hardware Hackathon
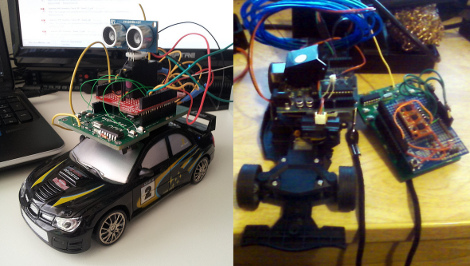
We hope you didn’t miss our announcements about the Hardware Hackathon we’re putting on in New York. It starts this afternoon and runs all night and into Sunday. If you really want to get in on the hacking we might be able to help you out (hit us up on Twitter). But you can also show up on Sunday to see the results live. Tickets for that are available here.
 May 9 & 10 Hackaday Prize Worldwide: Los Angeles
May 9 & 10 Hackaday Prize Worldwide: Los Angeles
Next weekend we open up the Hackaday Design Lab of Pasadena, California for a workshop, talks, and a day of hacking. This is the Hackaday Prize Worldwide: Los Angeles. Start out on Saturday with the Zero to Product workshop which will discuss getting from design to production. Interspersed with this are a set of talks from amazing presenters before a bit of social time at night. On Sunday we open our doors for Free Build and hope to see a ton of people working on their Hackaday Prize entries. RSVP now!
 Saturday, May 16 BAMF Meetup
Saturday, May 16 BAMF Meetup
Seeing everything at Bay Area Maker Faire means a lot of time on your feet. By the end of the day the Hackaday Crew is ready to take a load off and toss back a tasty beverage. We invite you to join us on Saturday, May 16th starting at 7pm. All the cool kids will be there so please RSVP now.
It’s not compulsory, but a lot of people bring hardware they’ve been working on to show off at this meetup and you should too!
 May 23 & 24 LayerOne Conference
May 23 & 24 LayerOne Conference
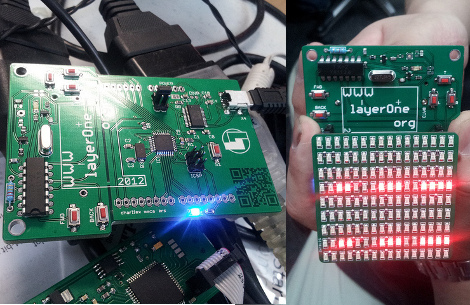
Every year our friends from NullSpace Labs organize the LayerOne Conference in Los Angeles. This is LA’s premier hardware security conference. This year Supplyframe is sponsoring the badges and Hackaday will be camped out at the Hackaday Hardware Villiage.
[Brian Benchoff] and [Mike Szczys] will be hacking their own badges while looking for awesome hacks other people are pulling off. We’ll bring plenty of swag and want to get everyone there to try at least some level of badge hack.