I just had my car in for an inspection and an oil change. The garage I take my car to is generally okay, they’re more honest than a stealership, but they don’t cross all their t’s and dot all their lowercase j’s. A few days after I picked up my car, low and behold, I noticed the garage didn’t do a complete oil change. The oil life indicator wasn’t reset, which means every time I turn my car on, I’ll have to press a button to clear an ominous glowing warning on my dash.
For my car, resetting the oil life indicator is a simple fix – I just need to push the button on the dash until the oil life indicator starts to blink, release, then hold it again for ten seconds. I’m at least partially competent when it comes to tech and embedded systems, but even for me, resetting the oil life sensor in my car is a bit obtuse. For the majority of the population, I can easily see this being a reason to take a car back to the shop; the mechanic either didn’t know how to do it, or didn’t know how to use Google.
The two most technically complex things I own are my car and my computer, and there is much more information available on how to fix or modify any part of my computer. If I had a desire to modify my car so I could read the value of the tire pressure monitors, instead of only being notified when one of them is too low, there’s nowhere for me to turn.
2015 was the year of car hacks, ranging from hacking ECUs to pass California emissions control standards, Google and Tesla’s self-driving cars, to hacking infotainment systems to drive reporters off the road. The lessons learned from these hacks are a hodge-podge of forum threads, conference talks, and articles scattered around the web. While you’ll never find a single volume filled with how to exploit the computers in every make and model of automobile, there is space for a reference guide on how to go about this sort of car hacking.
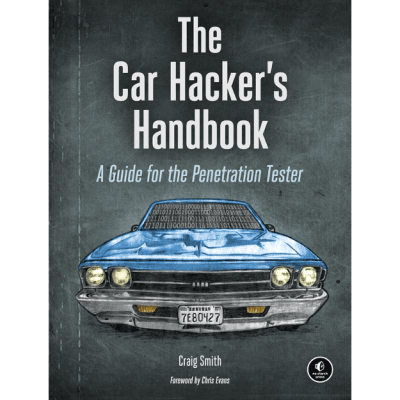
I was given the opportunity to review The Car Hacker’s Handbook by Craig Smith (259p, No Starch Press). Is it a guide on how to plug a dongle into my car and clear the oil life monitor the hard way? No, but you wouldn’t want that anyway. Instead, it’s a much more informative tome on penetration testing and reverse engineering, using cars as the backdrop, not the focus.
Craig Smith is one of the founders of Open Garages, one of the best repositories for vehicle documentation that you won’t find in a Haynes manual. He’s been in the car hacking game for a long time, too. One of his first car hacks, back when the extent of car hacking was modifying an ECU, was a complete teardown of the navigation system in his 2009 Civic. There’s depth and breadth to Craig’s knowledge, a necessity when it comes to reverse engineering a car.
Reverse Engineering. Also, Cars.
 Were it not for vehicle-specific communications protocols and mentions of ECUs, The Car Hacker’s Handbook could easily lose the word ‘Car’ from the title. I don’t think this is a bad thing. This is an introduction to pen testing, finding exploits, and futzing around with embedded electronics. It’s not a guide on tuning a Miata or making your nav system work after you’ve decided OnStar isn’t worth $250 a year.
Were it not for vehicle-specific communications protocols and mentions of ECUs, The Car Hacker’s Handbook could easily lose the word ‘Car’ from the title. I don’t think this is a bad thing. This is an introduction to pen testing, finding exploits, and futzing around with embedded electronics. It’s not a guide on tuning a Miata or making your nav system work after you’ve decided OnStar isn’t worth $250 a year.
The clearest example of this focus on reverse engineering, instead of modifying cars, is Chapter 8, Attacking ECUs and Other Embedded Systems. This is quite literally a tutorial on reverse engineering anything. The chapter begins with the sub-heading, ‘Analyzing Circuit Boards’, with the simple instruction, “When reversing a circuit board, first look at the model number of the microcontroller chips on the board.” This is how you begin to break down every bit of electronics, from cheap WiFi routers to broken Internet of Things devices.
The chapter on Attacking Embedded Systems goes through the usual tools – the JTAGulator, using an STM32 Discovery board for its SWD functionality, to side channel analysis with the ChipWhisperer. The only thing missing from this book is dropping acid and looking at the layers of metal and polysilicon in a chip, a subject that could fill several volumes.
Of course, this focus on the tools and techniques of reverse engineering is not at the expense of proper, traditional car hacking. The classic car hack – removing the 27-series ROM from an engine control unit tuning a car with a pattern of bits and bytes is still covered. Hacking infotainment displays is there, and there’s even a chapter dedicated to Vehicle to Vehicle communications, the next great advancement of our interstate highway system that’s been around for 20 years. This is, after all, a book on car hacking.
The Ethics of Car Hacking
There are bigger names than Craig Smith in the world of car hacking. Before last year’s Def Con, Charlie Miller and Chris Valasek made a name for themselves by taking a Wired writer out for a spin on a public highway. This was widely regarded as a bad move, even if it was great for publicity. You simply don’t remotely commandeer a vehicle while someone is driving it on a highway. Charlie and Chris had the opportunity to use a closed track for this demo for a tech journo, but didn’t. I can’t say I blame them; the press they got from that stunt was incredible.
George Hotz pulled a similar stunt with Bloomberg putting a self-driving car on I-280 in San Francisco. Yes, the self-made self-driving car worked as intended, but George did put a relatively untested system on the open road, with idiots texting and driving in the next lane.
The most important trait a person can have is the ability to differentiate between what is legal and what is ethical. The car hacks that have received the most attention are neither. Charlie Miller’s exploit is simply awesome, and George Hotz’ self-driving car is easily several PhD theses, but test tracks exist. There is no reason to put these cars on the road until sufficient testing is done.
Craig Smith falls on the safer side of garnering media attention. All of his modifications are on a test bench. From a Reddit AMA, he avoids demonstrating his exploits on real cars at all costs. This, by the way, is the standard way of doing things. No, vehicle exploits done in a controlled, non-public environment are not the most widely reported – that’s just a function of how much attention illegal and unethical vehicle exploits receive.
This focus on safety extends to Craig’s introduction of threat models before introducing the reader to the CAN bus. The Car Hacker’s Handbook is not a book telling the reader how to control everything in three thousand pounds of rolling steel. It’s a book telling the reader how to control a ton and a half of rolling death safely.
Takeaway
 This is first and foremost a book about hacking the electronics in cars. The skills required to modify an ECU, snoop the CAN bus, or update your sat nav maps without shelling out hundreds are the same skills required to install OpenWRT on a weird router and install Linux on a hard drive the hard way. Craig provides an excellent introduction to what can be done to hack a car, but presents it under the banner of hacking, without cars involved at all.
This is first and foremost a book about hacking the electronics in cars. The skills required to modify an ECU, snoop the CAN bus, or update your sat nav maps without shelling out hundreds are the same skills required to install OpenWRT on a weird router and install Linux on a hard drive the hard way. Craig provides an excellent introduction to what can be done to hack a car, but presents it under the banner of hacking, without cars involved at all.
The full title of this book is, The Car Hacker’s Handbook: A Guide for the Penetration Tester. The heading and subheading should be swapped, and that’s a good thing. This is a guide on how to reverse engineer, exploit, and modify any kind of embedded system; cars are just the example. Craig presents this in a way that is eminently comprehensible and spends enough time reinforcing the idea of hacking a car safely, legally, and ethically. It’s a great read, an excellent introduction to fiddling with embedded bits, and truly owning the devices you’ve already purchased.















Wanted to buy the book, saw the price….
50USD for a book ain’t that bad…
Found the college student.
50? I picked up up for $36 and that’s with tax shipped to my door
take care at not confusing V-TEC vs. V-TECH: both are toys but the price tag & audience differ :-)
If you buy only one tool for your car (besides the metal ones), buy a ODBII reader. It will allow you to see what the “check engine” light (MIL) is complaining about, and to clear the fault codes.
Around $50 at Amazon: for example: https://www.amazon.com/dp/B00X5EO6VC?psc=1
Re: clearing fault codes. Sometimes, all you want to do, is get your car through inspection. A lit MIL is an automatic fail. You can clear the fault codes with the ODBII reader, turning off the MIL. You need to then wait “some period of time” (I’ve been told 24-48 hours), before going to inspection. If the MIL doesn’t come on again (and it may very well not), you’ve deferred the repair until after inspection. This is important if you need a new catalytic or oxygen sensor or whatever, but don’t have the money & need to pass inspection so you can go to work and earn it!
I average 30 minutes until ready for a smog.
The ‘readiness monitors’ just need to reset to ok status, often a 5 mile or less trip on the highway from a cold start (you can warm it up for 2-5 minutes if you like) is enough for all the check routines to run.
Most testers will show you those readiness monitors, so you will know when you can smog.
The more you know. Like the gas tank may need to be between 1/4 and 3/4 full to run the evaporative emissions check, or you may pass a smog without that check returning the ok.
The purpose of the OBD2 drive cycle is to let your car run on-board diagnostics. This, in turn, allows monitors to operate and detect potential malfunctions of your cars’s emission system. The correct drive cycle for your car can vary greatly depending on the car model and manufacturer. Also, the monitor in question affects the required drive cycle.
Today, many vehicle manufacturers include these drive cycles in the vehicle owner’s manual. Typically, a few days of normal driving, both city and highway, will make the monitors ready. The following generic drive cycle can be used as a guideline if a specific drive cycle is not known. It will assist with resetting monitors when a car specific drive cycle is not available. However, it may not work for all cars and monitors.
The drive cycle can be difficult to follow exactly under normal driving conditions. Therefore, it is better to drive it in restricted area!
1. The universal OBD-II drive cycle begins with a cold start (coolant temperature below 50 C /122 F, and the coolant and air temperature sensors within 11 degrees of one another). This condition is easily achieved by letting the car to sit overnight.
2. The ignition key must not be left on prior to the cold start. Otherwise the heated oxygen sensor diagnostic may not run.
3. Start the engine and idle the engine in drive for two and half minutes, with the A/C and rear defroster on if equipped.
4. Turn the A/C and rear defroster off, and accelerate to 90 km/h (55 mph) under moderate, constant acceleration. Hold at a steady speed for three minutes.
5. Decelerate (const down) to 30 km/h (20 mph) without braking or depressing the clutch for manual transmissions.
6. Accelerate back to 90-100 km/h (55-60 mph) at 3/4 throttle. Hold at a steady speed for five minutes.
7. Decelerate (const down) to a stop without braking.
You can get a bluetooth one on eBay and free apps on your cell phone for under $5.
They work Ok too. Occasionally have trouble pairing with mine, but solid when it connects. Torque is a great free app too. The best things is these cheap adapters let you read live sensor data, not just fault codes. You are probably looking at around $100 for regular handheld units that will show live data.
Link for a recommended one?
https://www.amazon.ca/gp/product/B011NSX27A
Works like a charm with Torque. Went through several cheap “chinese” ones before finding this beaut.
Search for ELM327. Is hard to tell, they are basically all the same, a cheap ripoff of the ELM327 serial bridge chip paired with a cheap Bluetooth module, with questionable build quality.
OBDII reader should be able to tell you when you have satisfied all of the required monitors. You should also be able to see any faults that are pending but cannot be confirmed because the monitor is not complete.
Temporary faults can clear themselves given enough time so if your light has been on for a while then clearing the stored codes won’t help, they will just reappear as soon as the monitor is set which is exactly why its required to pass an inspection.
Over here they stick a tube up your exhaust pipe and measure the gasses. A warning light is only an indication of potential failure rather than a reason to fail.
Some cars have “secret handshakes” to display the fault code without using an ODBII reader.
On mine, I have to turn the ignition off, stamp on the brake and gas, then turn the ignition on until the dash lights up.. et voila, the fault code is shown on the odometer.
Still seems a moronic way of doing things though, I mean, why can’t they just make the centre console display “Cam sensor failure” instead of “ECN 036504”, it’s almost as if Microsoft wrote the software !
That way you (and anyone interested in fixing cars) must either spend money on special software that decodes OBD2 codes, including ones that are manufacturer-specific, or spend money in authorized car service center. I’m expecting that in the future people won’t be able to fix or even sell their cars o their own because everything will be DRMed “for our safety”. I imagine car industry will operate the same way games industry is working, ie. selling used car will be the same as selling used game and will require buyer to pay 40% of cars value to the manufacturer for making him authorized to start the engine…
Didn’t one of farm equipment manufacturers DRMed their embedded computers so fixing engine or any other system was next to impossible without asking them to fix it? I read it on HaD last year…
John Deere
I assume it’s because for many years the embedded systems in cars didn’t have a lot of RAM available, so they wrote smaller error code messages (Like HTTP 404 instead of “Page Not Found”). That said, you’re right: There should be human friendly error messages. With Bluetooth available on many cars, maybe these error messages could be sent to the owner’s phone so they have a record of what’s happening.
Personally I’d like to see all the data (emissions, engine performance, atmospheric conditions, seat heater use, tire pressure, etc.) logged in a database of some sort which I can store on (or copy to) a removable drive and access via a laptop. And ditch a lot of the custom cable connectors and use RJ45.
I think automakers really prefer you are kept in the dark. You might tinker with things and then they get saddled with a warranty return.
I just went through this, with a wifi enabled OBDII reader. You can’t just clear the codes. All but 2 monitors must be in the ready state for a <=2000 car in NY. Had the typical high idle & cyl1 misfire on Saturns SOHC. (supposedly a robot F'd up the gasket at the factory on MANY cars)
Changed the intake gasket & coolant temp sensor then the program got past the misfire & high idle to tell me about secondary air & EGR, which weren't getting read bc the program STOPS at the first trouble code. Fixed these & passed.
I would have never been able to fix this without the OBDII tool. All the above would have been either $1000 at a garage, or more likely the car killer. Instead it was all less than $100 between pick & pull, autozone & Amazon (OBDII reader included)
I had a faulty sensor that would trigger the code for a while, then go for weeks without triggering it (CATALYST EFFICIENCY BELOW THRESHOLD). Kept clearing the code until it took a break, then waited a few days and took it through inspection. The MIL came on as I drove out with my new sticker!
My mechanic finally troubleshot it and replaced a $50 sensor. Nothing wrong with the cat-con, which was a relief.
Pff. Why buy an OBDII reader? This is Hackaday, build your own. There’s even some basic concepts littered around here on how to do it.
Here’s all the neat things that have been posted so far: https://hackaday.com/tag/obd-ii/
I’m sure there’s even some good notes if you’d like to do the unthinkable and buy a gadget :).
You can get 30% off the book with coupon ”CARHACKERS” but I agree that the price is a bit steep. And 39.95$ for a digital copy? I’ll wait for it to be much cheaper on amazon in a few years.
It ends up being $27.96. Careful though, you have to enter it when you first view the cart, and at checkout (even though its listed at the top it still didn’t take the price off)
There is a free download link for a digital copy: http://opengarages.org/handbook/2014_car_hackers_handbook.epub
Am I the only one that bothered to look at the website to see the book is downloadable for free? http://opengarages.org/handbook/
The review was for a 259 page book, but when I download from your link, I only get 71 pages… somehow not quite the same thing
On the page you have first, free edition that was a part of two-day course or something. The new book is expanded edition…
That looks like the 2014 edition
I once dropped acid and stared at my face in the mirror for hours once…. or twice… or A LOT. Can’t say I’ve got much to show for it though…
Hopefully you didn’t drop (sulfuric) acid on your face.
This subreddit has some cool car hacking projects/resources too:
https://www.reddit.com/r/carhacking
Does any of these hacks actually improve these hacked cars performance? From what I’ve gleaned from the internet, not really.
A lot of people who ‘hack’ their vehicle do it so they can bypass the default RPM limits and/or get more power by altering the fuel/air mixture and spark timing. But adding an ‘eco’ mode is available online also.
Don’t let the YouTube videos of morons smoking pedestrians with modified Diesel trucks bring you down! I’ve found several builds that basically turn a vehicle into a drivable power station. :) A homemade generator with a catalytic converter is probably more environmentally friendly than a store-bought one without.
That’s not how cars work. There is no secret power to be unlocked with the right software. Now if you add or replace a significant amount of parts then you can benefit from a a/f map update or something like that, but any software modification has to go with a hardware one.
Very much not true. Turbo-engines have lots of room for software upgrades, no mechanical changes required.
I can’t remember what model but there’s some truck where modders tune the ECM for mileage at the expense of higher harmful emissions. Anybody know what I’m talking about?
Its ironic that the car shown on the cover can’t be hacked using the tools in the book. I own a 1969 Chevelle convertible, the car shown on the cover of the book, and can attest that there is not one computer, ECM or OBD port in the vehicle.
Aaannnnd this is (Part) of why everything I own is pre-computer test age. My newest vehicle is 10 years old and has a carburetor (motorcycle). Though my most used IS fuel injected, but 1993 model. So exempt from computer tests. Of course, the other reason I have vehicles that old is because I’m poor. But yanno… Splitting hairs there. Thinking of ripping the faulty ECU out of an 89′ pickup truck I have access to, and converting to carburetor. (Cheap solution) or doing my own EFI for it. (Expensive) Wonder if this book would be any help for the EFI route.
You can always reverse-engineer the ECU and fix it. Or design an Open Source ECU…
I live in Kansas where for school buses and random pull over of commercial vehicles there are no vehicle inspections. I was under the impression for a carbureted engine to be exempt it had to be standard equipment when manufactured. In the event that is true would your home brewed EFI be accepted if it somehow would meet emission standards for that year? Not sure what you mean by faulty ECU. In the event it’s simply busted wouldn’t the least expensive route to be to replace it, if replacements are available? In the event replacement costs more than the truck is worth slap the carb on it and bring it to Kansas to sell the truck to someone here. To be honest for my daily driver I’m not sure I want to return to a carburetor.
The actual we price isn’t really that bad, but I’ll down load the table of contents and the index first to see how relevant the book would be to my 1994 GMC. Where it can’t last forever I may go ahead and get the book anyway, as it may be useful for a vehicle I’ll own in the future or the vehicles of someone I know. Perhaps the mechanic in the story simply forgot to reset the service timer. As far as errors go that one is fairly benign. Vehicle owners who don’t keep a separate record of vehicle maintenance, and simply rely on others and technology aren’t doing they best they can as well. No one is perfect, expecting perfection in others could be a bitch if one’s own imperfections catches up with them.
CTRL+F “electric car” yields zero results. what is wrong with you people? EVs are the best thing to happen to electronics hackers and hobbyists since the obsolescence of vacuum tubes.
Someone tried to steal my 96 Honda civic, broke the ingiton to turn the steering wheel. I cant get any power past the fuse box under the hood, nothing ! Anywhere , no dome lights no door chime, I can’t even cross the starter and get anything, its almost like I have no ground to the frame….nothing !! Please help me I’m about to roll it down the street