[Bunnie Huang] and [Edward Snowden] have teamed up to publish a paper exploring the possibility of introspection on the iPhone.

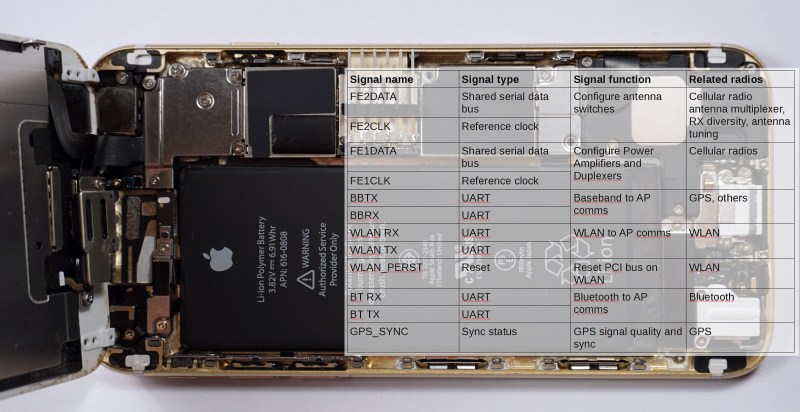
The idea is that phones are increasingly complex and potentially vulnerable to all kinds of digital surveillance. Even airplane mode is insufficient for knowing that your phone isn’t somehow transmitting information. The paper looks at the various radios on the iPhone, going so far as opening up the device and reading signals at each of the chips for cell, WiFi, Bluetooth, GPS, and NFC to determine whether the chip itself is doing anything, regardless of what the screen says. This introspection can then be used to be confident that the phone is not communicating when it shouldn’t be.
The paper goes on to propose a device that they will prototype in the coming year which uses an FPC that goes into the phone through the SIM card port. It would contain a battery, display, buttons, multiple SIM cards, and an FPGA to monitor the various buses and chips and report on activity.
Significant hacking of an iPhone will still be required, but the idea is to increase transparency and be certain that your device is only doing what you want it to.















This seems… Overdone useless and looking for hype.
Even if I grant you that, it is still a pretty epic hack to be able to introspect a modern computer in this way.
Fine, ill admit that, but still, this whole thing weirds me out and seems like a completely backwards way to do something
Well it is backwards, you’d have to work at Apple to do it forwards.
I’m one of those who supported Bunnie’s latest initiative. I even bought him a beer (+5usd).
Therefore, I am now a little sad to see him jump in at the deep end and become a conspiracy mongler. They do not help, they just spreads confusion and crush all forms of logical thinking. We should fight for logical thinking(!) not against.
It is of course easier to just intercept phones WiFi through the AP that you own! And the cell by an SDR.
“Big conspiracy” then say: -“…of course there are secret circuits with secret technique, unknown to everyone else … that goes on top of the Internet.”
Sure, a conspiracy that has passed thousands of technicians who have not said anything. Yess..
Then the “Snowden tells the truth while he sits in Putin’s lap”. Criticism of the United States from Moscow, on the border to technically impossible. And commercial and godwill suicide if funde true. Why waste time on this? WHY!?
Wow, living in denial much, huge black budgets must be spent on girl scout cookies.
The conspiracy theorists are too scatter brained to understand the true depth of the massive conspiracy represented by USA tech sector interconnection to 3-letter agency cooperation.
CIA has an investment bank for startups. Meanwhile all ‘our’ communications are routed into countries like Israel for first dibs on data mining us for blackmail, extortion, and corporate espionage purposes.
Things like San Bernardino, Nice France, etc. are not revealed because those events justify the massive spying in the first place.
One has to be totally naive to think security researchers are conspiracy theorists in the ‘moon landing didnt happen’ variety.
Yes since the inception of digital computation for codebreaking in WWII the intelligence agencies have been a decade ahead of the civilian application of computer science. The intensity of development and application of resources has not slackened from wartime, it’s all still regarded as crash projects urgent for national security and literal gigadollars are thrown at them. Since semiconductors you might think this is restrained by Moore’s law, but what I’m talking of is application, and this they leverage on absolutely massive scales. Civilian applications only imagined because “It would take hundreds of…” already done, they used thousands. For example in the mid-late 80s one of the 5eyes sigint sites had a massively parallel supercomputer using commodity hardware, a concept not seen in the civilian world until the “Beowulf” systems of the mid-late 90s. They used Microvax II units with dual processors and maxed out RAM, I don’t have exact figures, this was gleaned from examining Microvax units on the surplus market in late 90s, storage was of course removed and destroyed, but labeling on them indicated they were nodes in a cluster in excess of 2000 units, and they were early units, so as soon as they came available they ALREADY knew what to do with them. This cluster, live by about mid ’86, would have had a performance of several hundred megaflops, in 1986. This was 10 times the performance average of the Top10 supercomputers in the inaugural 1993 Top500 list. In fact such a machine would not have dropped off the Top500 list until a few years into the 2000s, but already they had replaced it for something BETTER in 1996ish.
Also you might wanna do an economic analysis of Intel’s CPU pricing when they release a new generation or process, the top of the line is always a bit more expensive than makes sense, and there’s always talk of “Maybe Intel not getting the yields they should be” along with channel shortages of the part. They are getting decent yields, it’s just most of them are already bought. And further than that, when a new process is brought online, those “unexpected delays” until it’s in full production, some of them might be actual technical problems, some of them can depend on how many special black runs are imposed on them by national agencies needing specialist parts.
Dammit, misspoke, gigaflops, performance was into the hundreds of gigaflops not megaflops.
Did you not stop to wonder about the term “reverse engineering” any time ever?
“Seems” implying you have no real evidence to back up your claim, right?
…but of course it’s overdone, useless and looking for hype! This is why it’s called an iPhone.
hypePhone, maybe?
I don’t see you getting anything better done… this project looks amazing and is needed now more than ever, done by people with the proper expertise. What’s with the condescending comments? It’s not like it’s your time on the line, maybe you’ll learn something, maybe not.
Ok lets break it down:
1] Lets face the harsh reality for a second, we all know that America can see anything you do on your iPhone/Android/Windows device if they really want too, no news there.
2] All this actually gets you is an answer to ‘is used at the moment?’ which really doesn’t tell u anything useful at all.
3] Im guessing people are supposed to open up their iPhone to be able attach the introspection device (“Significant hacking of an iPhone will still be required”) which i doubt any would like to do (considering price etc)
4] Making a phone ‘safer’ / ‘more secure’ by adding more hardware, thats really just a glorified logger? i dont see how thats supposed to work
5] What does Snowden have to do with any of this? i havent seen or heard anything about him being involved in any way with hardware before this point, so hes just lending his name to this, which is strange even if he’s a wistleblower on a related subject, it ‘almost’ seems like hes just looking for attention (again)
Point 2 again, cuz i used the wrong brackets causing part of the text to vanish
2] All this actually gets you is an answer to ‘is -chip x- used at the moment?’ which really doesn’t tell u anything useful at all.
Yeah, you’re probably right, their time is better used by doing nothing…
Some rebuttals:
1. Who said it was news. Knowing it happens doesn’t mean it’s something we should accept.
2. If I wanted to make a sensitive call, it’d be useful to know if “chip x” is being used at the moment I want to make the call.
3. Your guesses and doubts have no bearing on whether or not the device is useful for some people.
4. See my rebuttal to your assertion that knowing when you’re being surveilled isn’t useful in #2.
5. Snowden *is* looking for attention. Again. That’s his job now. To bring attention to himself, and thereby bring attention to the state of surveillance (among other things) most of us are subject to. Also, if you’ve been paying attention to Snowden at all, you shouldn’t be surprised he is focusing on hardware. Hell, a good portion of his life is spend communicating by telepresence robots. The tools governments use for surveillance start at the hardware level. It’s all about the hardware.
You’ve made it clear that you think the project is “overdone, useless, and looking for hype”, which is fine – it’s your opinion. But your opinion has very little value in the absence of ideas for how you’d solve the same problem. I’ll admit, I’m assuming you think the problem (introspection of phones) is a problem worth solving. I feel like that’s a fair assumption given the fact that you’ve spent time commenting on this article in the first place.
So tell us: how would you do it?
Saddam’s secret police had a house called “the fingernail factory”. everyone tells everything they know. much more efficient. smartphone not needed.
This is just to stop the police in democratic countries from doing search and seizure in criminal proceedings.
this we know as fact. no guesswork. no assumptions.
He’s trying his hardest to stay relevant. Vice interviews, remote teleconferencing, and this – it’s like coming out as the ‘whistleblower’ in a burgois manner wasn’t enough. If he cared so much about America and freedom, wouldn’t he be able to do more by staying inside the organization and continuously leaking information until he was caught? Chelsea Manning did that, she took her medicine with dignity and is serving in prison.
Meanwhile, Edward Snowden – who was a Dell Technician – is trying to mansplain the world on privacy. Yea, OK.
Did you see his last Vice interview? The editor asked what he could do to prevent his phone from being snooped on. Want to know Snowden’s answer? Desolder the external microphone and camera board from the phone. His assumption is that a government/organization will stop at software hacks.
LOL, yea OK. That makes perfect sense. Cause a government has no way of tapping a call through the carrier, if they really wanted to. Echelon doesn’t exist, right?
Everyone knows they will go in-line at the manufacturing level if they absolutely have to. How hard would it be to add a 2nd hidden microphone on-board and send the phone on it’s way. Parasitic taps hooked onto the primary phones power source, hidden on the circuit board of the phone or even using the phones resources.
The editor asked him how does he make a phone call if he desolders the microphone. Answer: use a headphone set with built in microphone. Yea. This guy has no idea what he’s talking about. Governments have never been known to be able to snoop on signals emanating from electronics. They have never been known to plant their own microphones in locations.
Desolder your camera, microphone, speakers, display, keyboard, touchscreen, R1, R5, C1, and so on until you are left with just the battery. Oh wait, some batteries have microcontrollers built in – we should desolder them as well.
I like the idea of an open phone, like Bunny’s other laptop project. An audit-able phone that not only allows for DIY repairs but gives the user more power and control over the phone, unlike a closed blob Samsung or iPhone.
Scarfing down caviar in a Russian hotel totally disconnected from reality while Chelsea Manning sends out communiques through her attorney and suffers through extreme depression.
I think the “disconnect the mic” issue is to stop them spying on you when you’re NOT making calls. It’s well known that The Man has been switching on the mic of phones and relaying the sound, when the phone’s supposedly quiescent.
As for a hidden, second mic, sure, it’s not impossible, but it’s not invisible either. If you know what to look for, you’ll find it.
In the United States, a group of consumers can get together and sue a manufacturer, called a “class action lawsuit”. For example, Volkswagen will pay 13 billion dollars in compensation to the owners of their diesel cars in the US.
So if there is any kind of “information leakage” intentionally placed in the phone by the manufacturer, the manufacturer will be … bankrupt.
Why would the manufacturer to take that risk?
Because they are not leaking info.. They are ‘cooperating’ and have been given ‘immunity’.
The real reason they do it is $ though. They charge the government for their cooperation. Selling user info to government is even a new business plan.,
Someone leaked or found documents detailing how much AT&T and friends would receive per call tap, phone log retrieval, it was crazy.
It would be useless for your average ‘cog in the machine’ kind of person that doesn’t have intelligence agencies targeting them. The article here “https://theintercept.com/2016/07/21/edward-snowdens-new-research-aims-to-keep-smartphones-from-betraying-their-owners/” talks about Marie Colvin who was a journalist killed by Syrian intelligence and was tracked down using her phone. What would you be comfortable using to communicate to the outside world from within Syria with a target on your back?
No, by itself I wouldn’t trust it, but it can’t make things any worse. Every little helps. Mostly I think it’ll be useful (assuming it works) in research, letting researchers know actually what’s going on under the cover.
If I wanted phone security I wouldn’t buy an Iphone in the first place though. Apple are innovative in finding ways of exploiting their users. And it’s a bit expensive to buy anonymously then throw away. I’m sure it connects to all sorts of servers without you being aware of it.
I can only imagine they chose the Iphone because it’d get media attention, Iphones always do. Little bit of a shame. Then again if you want to discover hidden transactions coming from a phone, Apple’s phones are a good place to look.
I will buy this the day it becomes available, which is unheard of.
This is complete BS, most data/control flow between cellular modem and AP are on high speed interface (like shared memory or even usb) and not uart. Uart are used for debug or other purpose (like boot recovery etc…).
Same for RF interfaces which are now dedicated high speed bus.
That’ why you need fpga. To access all those high-speed busses. For uart a small atmega or stm would be enough.
So are you saying that putting an FPGA magically gives you access to internally connected buses of the device?
Have you even read the post? Youneed to conenct things inside the iPhone, using the SIM card slot as an entry.
Yes, I have read it. The post talks about UARTs and medium speed RF control buses, not about shared memory or other really high speed buses which mac012345 mentioned. It may be that the solution offered will be able to draw significant conclusions, or not. But for sure an add-on FPGA cannot monitor signals that are not accessible on connectors and test points.
FPGA have a few advantages. If you need a logic analyzer, you can configure one inside the FPGA with the vendor’s tool. If you need an odd ball interface or one that can injects bit stream into the existing interface in real time, that’s easy to code one up. Much harder to do so in firmware and not mess up the timing.
Have you actually bothered to read the original paper, and have you been able to develop a thorough understanding of its contents?
Ehm, you’re wrong. If you look at datasheet from SiLabs/Nordic BT4.2 wireless data modules the UART is used also to comunicate.
And for certain MCUs UART may go fast up to 1GB, maybe I’m unprecise about the max speed but the concept still the same.
UART/USART can be used for data com.
May be 1Mbps is what you are thinking. Units are wrong, multiplier are wrong.
My HDD can’t even go 1GB/s.
oh yea, ops wrong letter : )
They can, in very old product or niche ones. Most new smartphone either use usb hsic interface or direct shared memory (when modem is on the same die). RF interface use proprietary bus most of the time or i2c/spi, so if testpoint are not accessible you’re stuck.
There can be some peripheral around that are still on an uart, but it’s less and less common.
Modern phone are more and more integrated (CPU/modem combo with popup flash/ram, BT/wifi single chips etc…). The right approach is software introspection, not hardware. And the ultimate protection is to leave phone away, or better, use phone tracking as a deceiver/decoy device.
ITT: cancer, leave now!
Simple. Don’t buy an iPhone.
For maannyyy reasons!
Want to Bluetooth a picture? Too bad, you have to buy an app first.
Why would i ever need to Bluetooth a picture?
Because no common cloud provider, flaky Internet connectivity, no cables at hand.
Because there are still users of “dumb” (read more secure) phones which have only IrDA and Bluetooth as a way of sending data.
I worked construction a few years ago and that job isn’t nice to technology, so we had flip phones. We took lots of photos and transferred them frequently.
The boss had Apple tech. :/
Really difficult to get the two to talk when I’m not familiar with anything Apple and there is a group of coworkers watching.
Kept trying to transfer via Bluetooth before I learned that Apple doesn’t make it easy. Eventually found working data cables and bounced the data across the devices.
I Phone Hater….
I’m with you. Anything ” I ” is BAD and Evil.
Never Never Never.
For an open source hardware design the key is a centralized power supply kill for each radio. This is present on the latest OpenMoko design, the Neo900.
There was talk on the maemo.org boards of a POCSAG pager plugin module for the hacking bus which would allow live radio silent connection to the world through an available and cheap service with good coverage.
In theory the POCSAG should be an inexpensive and very low power consumption(6 weeks on AA battery for a 90’s Motorola pager) system vs those transmitting radio waves at high bandwidth.
I dont think Apple would use normal low speed UART for their internal communication. Even they use their own proprietary JTAG like debug bus.
The pragmatic way.
1. Wrap your Iphone in tinfoil.
2. Place in small Faraday cage.
3. Throw it all in the river.
Umm a full wrap of tinfoil is a small Faraday cage.
Brought to you by the redundant department of redundancy.
Which one?
SWOOSH
As i remember correctly from 1st year college, placing it in Faraday cage would only stop the device from receiving transmissions but still can emit, it won’t be able to emit if the f.cage is grounded..or it was the other way around?
I’d like to see something that monitors for rogue base stations (ones that pop in and out, one that fades in and out when the phone is not moving exc)
Monitoring the spi line won’t tell you all that much about an exploit being carried out
I’m no expert but I don’t think the big attack vector chips are sharing a single bus
… Maybe nfc …
There’s an android app for that…
CellSpyCatcher
Not perfect, but better than nothing.
Yes! I’d like to see a good way of externally documenting law enforcement and other agency indiscriminate and willy nilly use of StingRay type devices, which I have noticed as a potential culprit in inflicting “collateral damage” on law abiding citizens.
Starting with mere annoyances, getting bounced off a (real) tower frequently and having calls disconnected for no reason when you’re in good signal area and not moving. Other similar disruptions of service. The capability of forcing cell radios to constant full power. I have two problems with that, one is you seemingly randomly get super short battery life, like 100% to dead in an afternoon, and while “normal” cell radio use has not been linked to biological damage, having your cell cooking you at full power for an afternoon cannot be good. Possible more severe consequences would be unavailability of phone in an emergency due to forced full radio power flattening battery.
Forced roaming states… I’ve been in my local area, apparently getting full normal signal yet my phone tells me it’s roaming, unpossible! If the local towers have gone dead and I’m somehow getting a fringe signal, it should not be full power! This next has not caught me out yet, but several people I know have had roaming charges from 30 or 40 miles out of home area, when they have not left the city. Long arguments with cell providers ensuing, with them insisting that if that’s what shows up on their system, that’s what must have happened. My suspicion in these cases is LE or other use of high power stingers on aircraft, following a suspect or whatever, but being high enough that they’re basically acting as a repeater or clone for the tower miles away that it should otherwise be physically impossible to connect to.
Would turning off roaming in your phone help? Phones usually have an option to manually select your network.
Just out of interest, do you still have to pay for calls if the The Man is routing them through his own equipment? And more importantly, WTF is going on where this sort of stuff is used so frequently? There should be no need for false base stations beyond James Bond doing something impossibly clever. If a court wants to spy on a phone user’s calls, have the provider keep a copy of them.
There’s too, too much power in the hands of a small, unanswerable minority of powerful fuckheads. Life never used to be like this. It’s not very good. Who do I vote for to put an end to this?
Like video calls, it was James Bond in the 1980s, now… https://en.wikipedia.org/wiki/Stingray_phone_tracker#Usage_by_law_enforcement
Actually, on that subject, something like an app to use public-key encryption for voice and txt would be useful. A big problem though would be that most people wouldn’t use it, making it a bit of sore thumb for those few who did. I suppose you could hide the data, disguise it as HTTPS or Torrent data or whatever, make it at least a bit more difficult to find. Volunteers could host sites providing public keys for each user’s phone number. Or else, if not a site, some sort of peer network again.
What would help, too, is if it was easy. Easy enough for your mother to use, though she still probably wouldn’t. To encourage use, and to keep the project alive. That, and keep the standard open.
Wouldn’t do a thing for the service disruptions, may even make you more “interesting” and more prone to them. You could find yourself escalated to getting denial of service whenever there was an ongoing incident in the area.
You mean something like Signal? Simple PKE, uses a key database linking public key to phone number (private key on the device), works by just installing the app. Routes phone or text over data or WiFi so the transmission is end-to-end encrypted.
Just think of all those apartment buildings that now have cell towers on them. I would never live on any of the floors that are with in 10 floors of those. Think of all the new borns that are being cooked in there mommies tummies.
It’s entirely possible to roam off network even with good RSSI from local towers. If those towers are saturated with traffic from others with better RSSI, they’ll push you off network. Also possible is maintenance blocking calls for troubleshooting purposes forcing one off network.
I work on towers and we have to do that quite often, though the transfer is usually within network. Switch maintenance and such can take a whole area ‘offline’ so to speak and calls will roam if there’s a suitable carrier nearby. That’s why I use an AT&T phone for working at Verizon sites and vice versa- many of their sites are co-located.
Roaming charges can be tricky to work out. Sometimes it’s not the local tower’s location that is used but the carrier’s switch, LNOC or RNOC that gets used depending on the agreements.
Cell towers that pop in and out may be COWs. (Cell On Wheels.) These are portable cell stations that are brought to large events where temporary crowds are expected (concerts, conventions, fairs, etc.) Just because there’s a new cell suddenly in the area doesn’t mean it’s a stingray.
What about unofficial short range radios inside the chips?
1) Remove your battery
2) Watch your phone magically not transmit anything anywhere whatsoever until you replace it, no need for any BunnyCases at all!
3) Works with any phone, no need to buy anything – Profit!
Is there room inside an iPhone for a reed switch? Use a NC type, so holding the magnet in the right spot cuts power to the phone?
Putting the phone in an RF shield just makes it crank up the TX power to max and drain the battery faster.
Of course, you can always buy a phone with a removable battery – just not an iPhone.
There isn’t even enough room for a headphone jack
+1
Awesome!
Bunnie is legit and the real deal. I’d be interested in who manufactured the equipment and provided training to the Syrian government for the ability to tap the sat link for the killing of Marie Colvin. Of course the true irony would be if it was manufactured in Russia, the country Edward Snowden hides in.
This raises lots of questions but it seems more sensible to just turn it off.
Wow you like to drink the CIA cool aid don’t you.
Honestly, what does it matter if we are being monitored 24/7? Is not like half of you are rocket scientist or top decret engineers…. what are they gonna see? You guys wacking off to porn? Your mom calling you for dinner waiting for you to finish a project on your basement? Lets admit it, most of use are just garage dreamers and tape and solder mechanics, we dont have anything interesting going on, nothing worth surveillance 24/7, the only reason i see any of us being paranoid about this, is if you have something to hide, or something important brewing in your code lines planning the next big website takedown or wiring relays setting off bombs and stuff like that, come on guys, the most interesting thing any of us has is probably a cool dog that walks more than you and gets more workout than any of us
Because we live in a time when any circuit board could be a bomb trigger, anyone who messes with that kind of thing for fun can’t be up to any good and can get a SWAT team response. Because we live in a time when any glassware or chemicals obviously mean you’re running a drug lab and can get a SWAT team response. Because we live in a time where satisfying your intellectual curiosity about any number of subjects could easily get you put on a no fly list. Because we live in a time that’s looking for the next scapegoat to blame all societies ills upon, to persecute and dehumanise, to be a synthetic problem that will create a political hero, this week Mexicans, next week Furries.
any circuit board is INTERPRETED as a bomb trigger regardless of true function
It’s about time. Furries are scum.
https://en.wikipedia.org/wiki/Nothing_to_hide_argument#Arguments_for_and_against
Well sure, most people aren’t doing anything wrong or interesting by normal standards. But what happens when the entities spying on everyone decide that X is illegal. Fill in X with pretty much anything – religion, your ethnicity, political views, or even meeting people after curfew! Now suddenly you are a criminal and they will snatch you! So mass surveillance is bad because it will be abused sooner or later.
I think there’s lots of unnecessary rhetoric here. For those who haven’t actually READ the proposal, it’s about knowing what your phone is doing via an independent, trusted physical device.
Why? Because if you’re a journalist, a whistleblower, someone named Isis, or an activist, there’s a strong possibility that a TLA agency or another will want to track and monitor you. Generally, we’re not worried about Apple opening up back doors in the OS for TLA agencies. We’re worried that, at some time, the device was not in your physical possession and was taken and modified. Or, when you ordered it, it was physically intercepted and modified.
Those here who want to be dismissive of conspiracy theorists are really daft. Snowden provided EVIDENCE of program after program that attempt to do nefarious things completely outside the purview of a warrant or anything remotely resembling due process, yet you want to dismiss the work one person who knows more about what’s possible in these devices and another who knows intimately what the TLA agencies are willing to do? What’s YOUR game?
You are not worried that Apple would open a back door? They have shown in the past and after San Bernardino that they are ready and willing to assist gov/orgs to access phones/communications/records. They just like to pick and choose which ones they do and how many press releases they will send out patting themselves on the back for.
If you suspect your phone is being tapped, is there really a point in knowing it is tapped? The point is moot, since there is no way to prove who did it – unless the TLA stamp all their worked with their respective name and address? Please return to TLA Headquarters, Maryland, USA.
Also, tapping the phone in software or hardware only makes the paper trail a little less shorter for gov/orgs. No access to the phone insides? Just have the calls redirected, copies of the texts from the carrier, etc… Listen through a placed microphone or from the distance. Have the phone transmit encoded data over the speaker through VH or low freqs. If your phone is so important that it would merit hardware hacking by some gov/org, they are not going to give up if they can’t access the inside of their phone. They are not going to give up if all of a sudden you start putting your phone on airplane mode to make calls for certain hours of the day. There are lots of ways to listen to your calls and read your communications.
:They are not going to give up if all of a sudden you start putting your phone on airplane mode to make calls for certain hours of the day.:
That’s the point, and we need to show it to the people that they don’t give up and use all kinds of hijinx.
Unfortunately, the device is already mostly useless.
Why would someone who has completely pwned the phone and is surreptitiously monitoring the audio/camera/GPS/data feel the need to transmit that data in real time? All the phone may be tasked to do is listen to the mic and record, and occasionally read existing location services data (which doesn’t always originate from the GPS radio.) It doesn’t have to transmit the recording until the data radio is in use sending legitimate user data, or perhaps it sends a batch only when it’s near the subject’s home tower, where typical update or sync types of transmissions are expected. The NSA isn’t populated only by Jack Bauer from “24”. Only in case of imminent takedown would they need real-time intel on a subject; otherwise, they can let them roam, free to interact with and implicate other likely co-conspirators. They can always analyze the data later, at their leisure.
Stealthy blackhats already do this in order to camouflage their exfiltration of data from a business network, transmitting batches of data only during working hours, using normal looking ports and protocols. Why would Snowden be so naive as to think the NSA incapable of similarly disguising their work?
Because he’s starting to look more and more like an attention hungry A++, MCSA IT helpdesk know’s-better-than-you.
“Stealthy blackhats already do this”,
All windows10 users do it too. Not that they know it though.
I actually expected Bunnie to just make a new phone like the laptop.
…for moderate amounts of “laptop” as opposed to rectangular metal box housing some random hardware.
Yeah that would have been admirable, and genuinely useful.
Seconded
Yup an open 3G / LTE / 2G core would be a nice thing for the world to have. So we know we could at least trust our own hardware, if not the networks it connects to. I suppose there’s the dirt-cheap Chinese Mediatek chips, if you want to make your own phone, and don’t mind the possibility of the Chinese spying on you. Which is unlikely outside of China’s information networks.
Such a phone would be bought by 20 people, but only after they dropped the price to 2% of manufacturing cost.
Realistically people will be using iphones and android phones, and it makes more sense to be in the know abut those.
I’m not saying sell a phone, just have a free open FPGA core for people to do whatever they like with. If someone wants to make their own phone, they can. SDR is coming down in price, FPGAs aren’t too expensive, it could all be possible in not-too-long. And everyone could do it their own way.
Of course it’s good to know about the hardware we actually have, but you can’t trust it completely. In fact you’ve no idea how far you can trust it.
Regarding the Mediatek chips, read Bunnie’s old article about “Gongkai”. There’s thousands of cheap little phones available in Shenzen, probably hundreds of companies, quite possibly a few in somebody’s garage. The chips are all-in-one phones, and the firmware’s widely shared / pirated / whatever / it’s China so there’s no diffference.
Reverse-engineering one of those (an ARM core for the phone’s main code, and another ARM for the cellular-interface side) would be very useful too, an free (libre) open firmware’s nearly as good as a free open phone. Mediatek chips seem to be inside most of these me-too phones, and they come in all sorts of capacities, with “dirt cheap” as most of the price range.
https://www.bunniestudios.com/blog/?page_id=3107
A great article in general, not really about freedom, but about Gongkai and the marketplace. It’s got really cheap to design and manufacture a phone these days, in China. No longer the huge investment it was, or still is outside China.
Or,don’t have a phone and use the physical world as your encryption……….
The snowden reveals also showed that the CIA targets people in places like afghanistan/pakistan who either frequently turn their phone off or don’t carry one.
So not carrying one isn’t perfect, especially if they can detect you visually with drones or CCTV and not detect a corresponding signal from your location.
You do know that with a phased microphone array you can pick out 2 people talking in a crowd?
The VICE interview is full of bullshit. Snowden talks about advanced de-soldering skills when we can all see the camera is on a flex cable with a press-on connector. They then go on about your phone being spied on with Flexispy, which cannot be installed remotely, requires a jailbroken/rooted device and any OS update renders it useless. Snowden has run out of ways of being interesting, he probably isn’t as keen with tech as he makes it seem and needs to lie to gain attention. I thought lies was what he was against…
‘which cannot be installed remotely’. Yeah I’m sure happy that you are the chief apple engineer and know that for sure.
Ask anyone who knows how Flexispy works.
Or you can just keep tour tinfoil hat on and be ignorant about the facts.
What is tour tinfoil hat?
Yeah this typo-police thing is getting old fast.
As the worlds most famous traitor it is important for Snowden to stay in the limelight. Even if he has to spew bullshit to do so. The second the spotlight is off him- he will mysteriously disappear.
Somebody call me when Snowden is dead. I absolutely hate that traitorous loser. Huang (who I actually respect) would do well to steer clear of his crazy. The guy didn’t pay attention in school and signed up to spy on fellow Americans and then figures out what his job description meant…
He should be a hero to no one and his supposed leaks were news to no one that hung out on cryptome and the like. That was one of the hiring ploys back then-“come to us we have Carnivore and listen in on the worlds telecomm”.
The point is, spies have to follow certain rules, and they weren’t doing. That’s wrong. Edward informed the people, who the various spies are supposed to be working for, of that. Edward agreed to do a whole load of evil shit, but it turned out it was more evil than they told him, than they’re supposed to.
It’s bad enough the stuff they’re allowed to get away with, without more. And most people don’t hang out on Cryptome. That’s what whistle-blowers are for.
As for him now enjoying the protection of Putin, yep, Putin’s around as bad as the spooks that Edward’s pissed off so much. Nobody really knows exactly how bad, but I’d bet it’s comparable. But assuming the guy wants to live without being tortured, he’s probably in the best place.
You honestly believe Snowden would be tortured? No. He would sit in a prison for the rest of his life, and that’s what he is scared of.
The USA tortures people, your government’s even tried to claim it’s reasonable sometimes. Snowden can easily be disappeared off somewhere where nobody will hear about him. Do you honestly believe there’s nobody with the ability to get away with torturing him, who doesn’t want to do it just because they’re a bit of an evil fucker? Government employees breaking the law is why he’s hiding in Russia in the first place.
I don’t know if he’d be tortured, because I don’t know who these people are. I certainly don’t trust them not to, though. If he was dragged back to the USA, I would be concerned about his safety.
There’s also the organised rape problem American prisons have, where staff collude to have prisoners raped. As well as the prisoner-organised rapes. Rape never happens in British prisons. It’s unheard of. You people really need to sort your shit out. I wouldn’t visit the USA if I had the chance.
Besides all that there’s the point that he doesn’t DESERVE prison! He blew the whistle on other government employees breaking the law. I’m sure they still are, of course, but at least he tried.
By committing treason. You sound like an intelligent but ignorant person, Greenaum. Spying-by its very nature is to steal information. Why would thieves give a shit about rules lmao?
Your jingoistic tirade on torture aside, he would hopefully be released to the American people to have our own “Mussolini headkick”. Most likely, he would be given a goddamn reality show on TV about saving Betta fish from the horrors of pet stores. smh. Unfortunately our country is now run by folks that have no sense of history or future.
Without seeing you I know your color is green. It’s like magic.
anyone play modded minecraft?…mods like nuclearcraft will have you discussing the oddest things while on the phone with your friends…from extraction to purification of nuclear fuels to your new innovative reactor design….
I’m with you. It is funny to think how many times a day they hear people discussing bombing bases, constructing tunnels, and teabagging dead foes. And then we have these goons trying to convince us they are going to arrest innocent folks by the droves over some bit of misunderstood personal data-and yet it never happens. Guess they have good filtering :)
Did I say this before? Never-mind, I’ll say it again (it needs to be said again, and again): Bunnie Huang reminds me of my ABANDONED Chumby! Shame on you BH.
Oh Chumby. That one just petered out didn’t it. Years ahead of crowdfunding woes or more like an alpha project in crodfunding woes lol. My buddy got burned on that one too. I still think Huang is a brilliant person but just wish him and Ben Heck would go have a company together and prosper.