Imagine cooling your building with the same principle that kept Victorian-era icehouses stocked with lake-frozen blocks, but in modern form. That’s the idea behind ice batteries, a clever energy storage hack that’s been quietly slashing cooling costs across commercial buildings. The invention works by freezing water when energy is cheap, and using that stored cold later, they turn major power hogs (air conditioning, we’re looking at you) into more efficient, cost-effective systems.
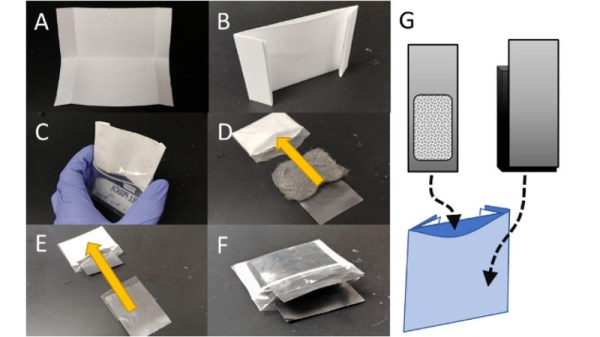
Pioneers like Nostromo Energy and Ice Energy are refining the tech. Nostromo’s IceBrick modules pack 25 kWh of cooling capacity each, install on rooftops, and cost around $250 per kWh—about half the price of lithium-ion storage. Ice Energy’s Ice Bear 40 integrates with HVAC systems, shifting up to 95% of peak cooling demand to off-peak hours. And for homes, the Ice Bear 20 replaces traditional AC units while doubling as a thermal battery.
Unlike lithium-ion, ice batteries don’t degrade chemically – their water is endlessly reusable. Combining the technology with this hack, it’s even possible in environments where water is scarce. But the trade-off? They only store cooling energy. No frozen kilowatts for your lightbulbs, just an efficient way to handle the biggest energy drain in most buildings.
Could ice batteries help decentralize energy storage? They’re already proving their worth in high-demand areas like California and Texas. Read the full report here and let us know your thoughts in the comments.
Continue reading “The Coolest Batteries You’ve Never Heard Of”