You shouldn’t transmit encryption keys over Bluetooth, but that’s exactly what some popular wireless-enabled microcontrollers are already doing. This is the idea behind Screaming Channels, an exploit published by researchers at EUERCOM, and will be a talk at Black Hat next week. So far, the researchers have investigated side-channel attacks on Bluetooth-enabled microcontrollers, allowing them to extract tinyAES keys from up to 10 meters away in controlled environments. A PDF of the paper is available and all the relevant code is available on GitHub.
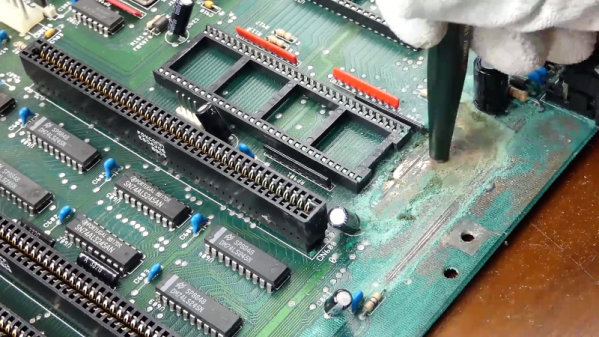
The experimental setup for this exploit consisted of a BLE Nano, a breakout board for a Nordic nRF52832 Bluetooth microcontroller, a Hack RF, a USRB N210 software defined radio from Ettus, and a few high-gain antennas and LNAs. The example attack relies on installing firmware on the BLE Nano that runs through a few loops and encrypts something with tinyAES. Through very careful analysis of the RF spectrum, the AES keys can be extracted from the ether.
Side channel attacks have received a bit more popularity over recent years. What was once limited to Three Letter Agency-level Van Eck phreaking can now be done inexpensively and in a system with devices like the ChipWhisperer.
Of course, this is only a demonstration of what is possible with side-channel attacks in a highly controlled environment with a significant amount of work gone into the firmware running on the microcontroller. This isn’t evidence that balaclava-wearing hackers are sniffing your phone from across the parking lot to get the password to your Instagram account, but it does show what is possible with relatively cheap, off-the-shelf hardware.