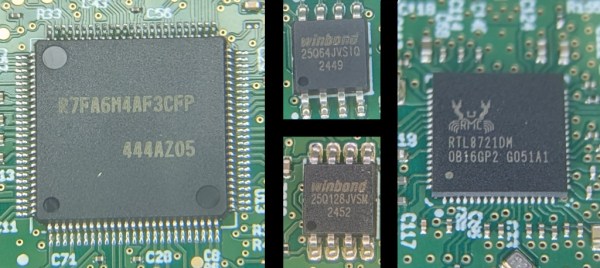
You would think a guitar amplifier would be a straightforward piece of analog electronics. But, of course, these days, everything has firmware, including [mforney]’s Yamaha THR10c. The service manual showed both a UART and JTAG header on the schematic, so as many of us would, he took that as a challenge.
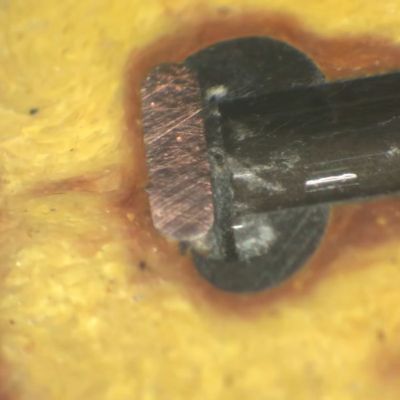
Of course, the production board doesn’t have headers for these ports, but that’s not a real problem. The serial port seemed quiet, but the JTAG port was more productive. This revealed two binary images: a bootloader and the main firmware. Once you have the code, it is a straightforward, if not laborious, process to reverse engineer what the code does.
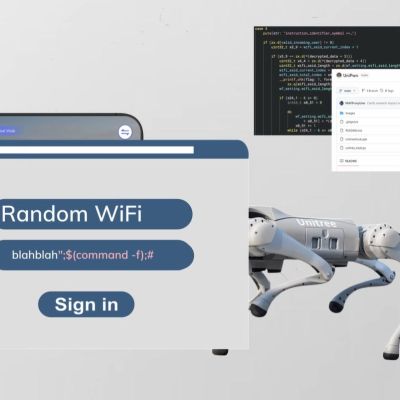
The next step is to figure out how to load new firmware. You can see in the post that this was done, and custom features sprang into life with custom-patched firmware.
We never get tired of seeing people dig into consumer devices like this. Things like JTAG and the wide availability of JTAG tools have made it easier but no less fun. Of course, there are even more features [mforney] has in mind, but now that’s just a matter of coding.



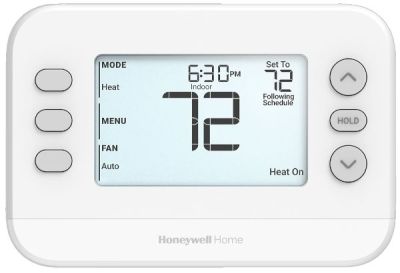 The Honeywell X2S Smart Thermostat is a Wi-Fi-enabled thermostat that is meant to integrate with your typical ‘smart home’ setup, with mobile app control available as well. Of course, just using it as-is would be extremely boring, so fortunately we have [author0] to take it apart and
The Honeywell X2S Smart Thermostat is a Wi-Fi-enabled thermostat that is meant to integrate with your typical ‘smart home’ setup, with mobile app control available as well. Of course, just using it as-is would be extremely boring, so fortunately we have [author0] to take it apart and