 Between 2000 and 2002 the Fisher Price Pixter was sold to children as an educational handheld toy with a touch screen that enabled drawing and listening to music in addition to cartridge-based games and more. It was followed up by multiple new iterations of the system, but as an ecosystem didn’t last beyond 2007. This has left much of the system in obscurity, with people like [Dmitry] doing their best to reverse-engineer, dump and document what they can, such as recently for the entire range of Pixter devices and most of the games.
Between 2000 and 2002 the Fisher Price Pixter was sold to children as an educational handheld toy with a touch screen that enabled drawing and listening to music in addition to cartridge-based games and more. It was followed up by multiple new iterations of the system, but as an ecosystem didn’t last beyond 2007. This has left much of the system in obscurity, with people like [Dmitry] doing their best to reverse-engineer, dump and document what they can, such as recently for the entire range of Pixter devices and most of the games.
One of the reasons why [Dmitri] got interested in the second-generation Pixter Color originally was as a potential PalmOS porting target, which gives somewhat of an idea of how these devices were meant to be used.
With absolutely no remaining known official documentation on how to develop software for the hardware reverse-engineering posed somewhat of a challenge. Fortunately this was made somewhat easier by the Pixter Color using the ARM-based LH7541, but worse by just how much of a minimal ARM7 implementation the SoC is. This was meant to go into a cheap-ish kid’s toy after all.
Where things got wild was that the firmware implements a 16-bit stack-based virtual machine, possibly due to initially having selected a completely different SoC. From here things get even crazier with how audio output is implemented, with [Dmitry] descending into a long-winded rant on this and all the weird things encountered during reverse-engineering.
After the Color Pixter its Multimedia sibling with slightly better SoC was also reverse-engineered, as well as the Classic device that started it all. This particular device uses an 8-bit VM, but a black-blob 6502 processor, which is rather astounding for a 2000-era device, but then again it was meant to be a toy.
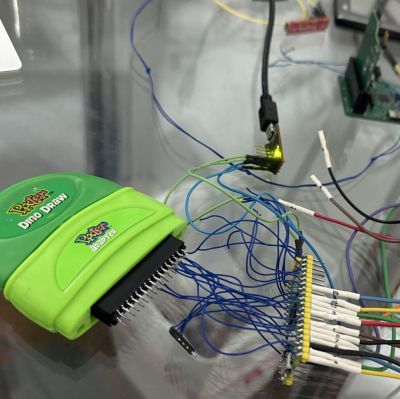
In addition to getting a lot of reverse-engineering woes off his chest, [Dmitri] also details how he reverse-engineered and dumped the cartridges, as well as writing emulators to ensure that the Pixter legacy will endure, for better or worse.
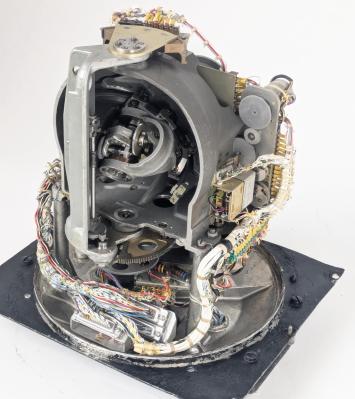
Top image: Pixter with opened case. (Credit: Raimond Spekking, Wikimedia)



 In any MMORPG, the average user will generally only encounter the client side of the system. This makes building a compatible open source version of the proprietary server into a bit of a chore. Of course, sometimes you get a bit of a break, such as with the – still active – MMORPG Ultima Online, when the disc for the 1998 The Second Age expansion contained a stand-alone demo. This also meant a (stripped-down) server which has been gratefully reverse-engineered by the community, with [draxinar] now claiming to
In any MMORPG, the average user will generally only encounter the client side of the system. This makes building a compatible open source version of the proprietary server into a bit of a chore. Of course, sometimes you get a bit of a break, such as with the – still active – MMORPG Ultima Online, when the disc for the 1998 The Second Age expansion contained a stand-alone demo. This also meant a (stripped-down) server which has been gratefully reverse-engineered by the community, with [draxinar] now claiming to