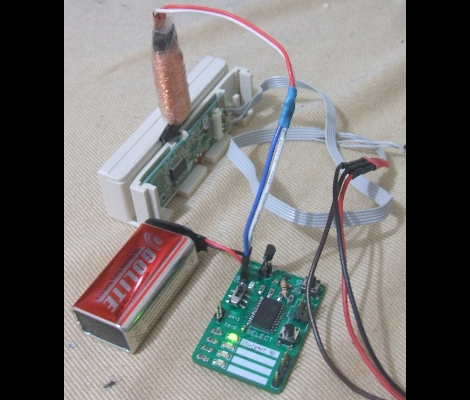
Here’s a field-programmable RFID spoofer developed by [Doug Jackson]. He was inspired by the spoofers we looked at near the end of September that didn’t have source code available. With the idea seeded in his mind he figured he could develop his own version, and then decided to share the build details with the rest of us.
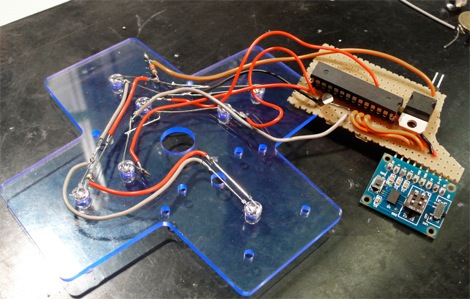
The tags that he purchased for testing and developing the spoofer have a code printed on the back of them. A bit of sleuthing at the data from a tag reader and he managed to crack the code. From there he built this tag spoofer with a keypad on which you enter the number from the back of any 125 kHz tag and the device becomes that tag. If you have been waiting to test your RFID hacking skills there should be nothing holding you back now that [Doug] shared the details of his own adventure.