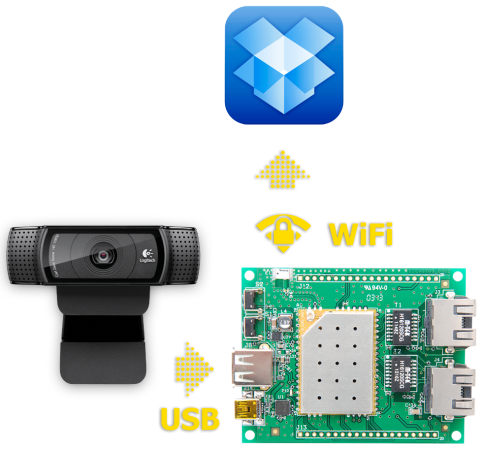
We have friends watch the cats when we go out-of-town. But we always leave a server running with a webcam (motion activated using the Linux “motion” software) so we can check in on them ourselves. But this project may inspire a change. It leverages the features of a Carambola2 to capture images and upload them to Dropbox.
In the picture above the green PCB is a development board for the tiny yellow PCB which is the actual Carambola2. It is soldered on the dev board using the same technique as those HC-05 Bluetooth modules. That shielded board includes a Qualcomm SoC running Linux and a WiFi radio. The dev board feeds it power and allows it connect to the USB webcam.
There’s a bit of command line kung-fu to get everything running but it shouldn’t be out of reach for beginners. Linux veterans will know that taking snapshots from a webcam at regular intervals is a simple task. Uploading to a secure cloud storage site is not. A Bash script handles the heavy lifting. It’s using the Dropbox Application API so this will not violate their TOS and you don’t have to figure out your own method of authenticating from the command line.