Do you miss the days of thumbing through a sticky, laminated booklet to order your food? Sick of restaurants and their frustrating electronic menus? Fear not, for [Guy Dupont] and his QR code menu printer are here to save the day.
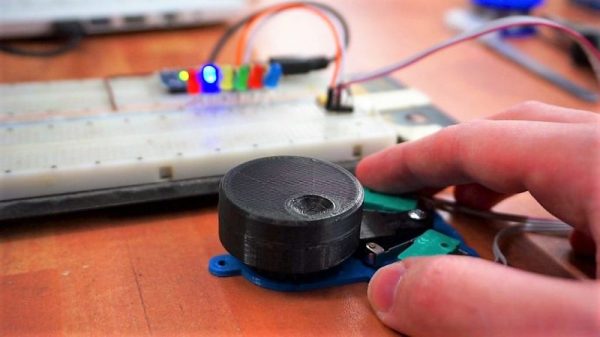
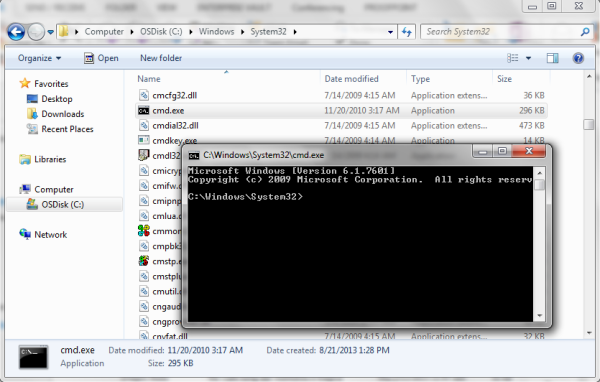
Yes, that’s right — it’s a lunchbox-sized printer designed to spit out a paper version of a digital menu. Using a Tiny Code Reader from Useful Sensors, the device can scan a QR code at a restaurant to access its menu. A Seeed Studio XIAO ESP32 takes the link, and then passes it to a remote computer which accesses the menu online and screenshots it. The image is processed with TesseractOCR to extract food items and prices, and the data is then collated into a simple text-only format using ChatGPT. The simplified menu is finally sent to a thermal printer to be spat out on receipt paper for your casual perusal.
[Guy] was inspired to build the project after hating the experience of using QR code menus in restaurants and bars around town. It’s his latest project that solves an everyday problem, it makes a great sequel to his smart jeans that tell you when your fly is down.