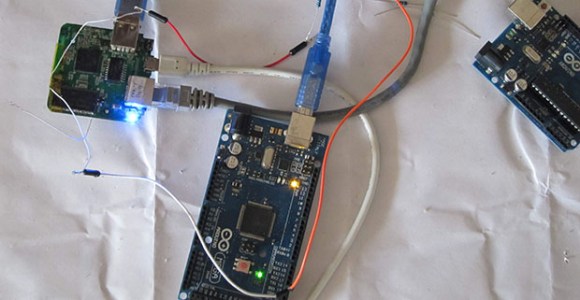
We’ve been waiting for this one. A worm was written for the Internet-connected Arduino Yun that gets in through a memory corruption exploit in the ATmega32u4 that’s used as the serial bridge. The paper (as PDF) is a bit technical, but if you’re interested, it’s a great read. (Edit: The link went dead. Here is our local copy.)
The crux of the hack is getting the AVR to run out of RAM, which more than a few of us have done accidentally from time to time. Here, the hackers write more and more data into memory until they end up writing into the heap, where data that’s used to control the program lives. Writing a worm for the AVR isn’t as easy as it was in the 1990’s on PCs, because a lot of the code that you’d like to run is in flash, and thus immutable. However, if you know where enough functions are located in flash, you can just use what’s there. These kind of return-oriented programming (ROP) tricks were enough for the researchers to write a worm.
In the end, the worm is persistent, can spread from Yun to Yun, and can do most everything that you’d love/hate a worm to do. In security, we all know that a chain is only as strong as its weakest link, and here the attack isn’t against the OpenWRT Linux system running on the big chip, but rather against the small AVR chip playing a support role. Because the AVR is completely trusted by the Linux system, once you’ve got that, you’ve won.
Will this amount to anything in practice? Probably not. There are tons of systems out there with much more easily accessed vulnerabilities: hard-coded passwords and poor encryption protocols. Attacking all the Yuns in the world wouldn’t be worth one’s time. It’s a very cool proof of concept, and in our opinion, that’s even better.
Thanks [Dave] for the great tip!