The mid-1980s were a time of drastic change. In the United States, the Reagan era was winding down, the Cold War was heating up, and the IBM PC was the newest of newnesses. The comparatively few wires stitching together the larger university research centers around the world pulsed with a new heartbeat — the Internet Protocol (IP) — and while the World Wide Web was still a decade or so away, The Internet was a real place for a growing number of computer-savvy explorers and adventurers, ready to set sail on the virtual sea to explore and exploit this new frontier.
In 1986, having recently lost his research grant, astronomer Clifford Stoll was made a computer system admin with the wave of a hand by the management of Lawrence Berkeley Laboratory’s physics department. Commanded to go forth and administer, Stoll dove into what appeared to be a simple task for his first day on the job: investigating a 75-cent error in the computer account time charges. Little did he know that this six-bit overcharge would take over his life for the next six months and have this self-proclaimed Berkeley hippie rubbing shoulders with the FBI, the CIA, the NSA, and the German Bundeskriminalamt, all in pursuit of the source: a nest of black-hat hackers and a tangled web of international espionage.
 Published in 1989, shortly after the events it describes happened, The Cuckoo’s Egg: Tracking a Spy Through the Maze of Computer Espionage is a strange beast for a book ostensibly about technology. It reads very much like a novel, with tons of dialog drawn from the copious notes Stoll took during his investigation. He admits that some of the conversations are not recorded verbatim, which is understandable for anyone who has heard Stoll speak; keeping accurate track of that much manic energy would be difficult, to say the least. But his eye for detail is impressive, such as when rattling off the port and line assignments whipping back and forth on a conference call attempting to trace the nationwide web of phone calls and network connections his hacker used to break into LBL’s computers.
Published in 1989, shortly after the events it describes happened, The Cuckoo’s Egg: Tracking a Spy Through the Maze of Computer Espionage is a strange beast for a book ostensibly about technology. It reads very much like a novel, with tons of dialog drawn from the copious notes Stoll took during his investigation. He admits that some of the conversations are not recorded verbatim, which is understandable for anyone who has heard Stoll speak; keeping accurate track of that much manic energy would be difficult, to say the least. But his eye for detail is impressive, such as when rattling off the port and line assignments whipping back and forth on a conference call attempting to trace the nationwide web of phone calls and network connections his hacker used to break into LBL’s computers.
Although a more formal paper was written (PDF link), The Cuckoo’s Egg is more engaging because reads like a story, not a dry technical recounting of what happened. I picked the book up when it was first published, probably as a way to shirk my undergrad studies and escape into a different and far more interesting world than molecular biology. As I read Stoll’s book, I felt an instant kinship with him — we were both misfit scientists, each trying to find a way to meld our interests in computer science with the fields we had chosen. Like him, I felt I had chosen perhaps a bit unwisely, but to read of his exploits showed me there was a wider world out there.
Not a small number of Hackaday readers will remember these early days of the Internet, and despite the narrative nature of The Cuckoo’s Egg, there are plenty of tech tidbits and blasts from the past to satisfy the appetite for details. The title derives from the method Stoll’s hacker used to elevate himself to superuser privileges on an LBL Unix machine; using a then-unknown bug in Emacs, the hacker was able to move a hacked version of the atrun program into system space; it would run within five minutes and give him superuser privileges, in much the same way that a cuckoo bird lays her egg in another species’ nest, letting her chick hatch and grow to the detriment of the host family.
 For my money, the best parts of the book are when science collides with engineering. After a chance meeting in the lunchroom with Nobel laureate Luis Alvarez, popularly known for discovering the iridium boundary that suggests an asteroid impact 65 million years ago had wiped out the dinosaurs, Stoll began thinking of the chase for the hacker in scientific terms. That is to propose a hypothesis, design an experiment, and test your assumptions. Tracing and eventually gathering enough evidence to capture not just a single hacker but a group that had been selling secrets to the KGB was possible only because of Stoll’s meticulous observations and application of the scientific method. Stoll’s work is the reason this approach became a blueprint for my own career, even if I didn’t always stick to the plan.
For my money, the best parts of the book are when science collides with engineering. After a chance meeting in the lunchroom with Nobel laureate Luis Alvarez, popularly known for discovering the iridium boundary that suggests an asteroid impact 65 million years ago had wiped out the dinosaurs, Stoll began thinking of the chase for the hacker in scientific terms. That is to propose a hypothesis, design an experiment, and test your assumptions. Tracing and eventually gathering enough evidence to capture not just a single hacker but a group that had been selling secrets to the KGB was possible only because of Stoll’s meticulous observations and application of the scientific method. Stoll’s work is the reason this approach became a blueprint for my own career, even if I didn’t always stick to the plan.
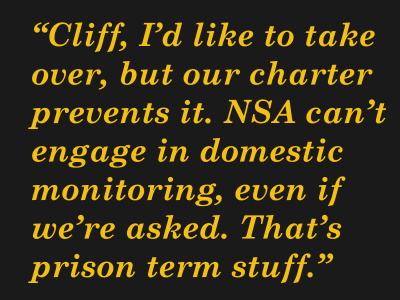
The book also foreshadows the rise of the security state and suggests that everything we’ve become accustomed to these days in the US, including domestic surveillance by the NSA, was probably being actively if covertly pursued back in the mid-80s; an NSA analyst’s profession that domestic monitoring would result in prison terms rings hollow these days.
I’d say The Cuckoo’s Egg is a must-read for anyone interested in the interface between science and engineering, and by this point it has even become something of a classic of tech literature. It’s well worth the read, but of course if you’d rather spend an hour watching a NOVA episode, the video after the break will give you the gist with the bonus of putting faces to the names in Stoll’s book, since many of the people involved were used in the reenactments. But fair warning: if you skip the book you’ll miss the connection between Stoll’s search and one of the most famous worm attacks in computer history.














“In 1986, having recently lost his research grant, astronomer Clifford Stoll was made a computer system admin with the wave of a hand by the management of Lawrence Berkeley Laboratory’s physics department.”
From astronomer to sys admin. Quite the leap.
It’s a great read. As is Steven Levy’s CRYPTO.
What’s old, is new again (with different technology)
Maybe we’ll have a Captain Crunch whistling into a cellphone.
Agreed. I read it years ago and it unfolds like a great mystery / spy story. The fact that it actually happened was simply all the more exciting. In fact I think the book is still on my shelf even now. Well worth reading, a lot of fun.
We’ve got several copies in our family, my dad, my brother and I all have paperback plus we got 2 signed hardcover copies when we bought a Klein flask from Cliff for a gift for dad. This is one of my favorite books, and as noted several times here the fact it’s true just makes it better. Not to mention it gives a great insight into the early days of what became the Internet/World Wide Web we know today…..
Well, back then, anyone who had to work WITH computers, had to know a lot about HOW they worked.
Although I was the electronics guy in my family, my brothers who were accountants were using PCs long before I got my hands on one. And because they were the first in their companies to have computers, they had to train others on how to use them, after Visicalc and Lotus 1-2-3, then came the word processors and the need for other office people to know how to use them. One brother set up the network in his company, installing network cards and software, cutting and attaching connectors and terminators to Thinnet, and setting up the modem, and attaching printer(s).
Sometimes one would call me with a question relating to computers, and I had no idea on how to help them.
But, I was the first in the family with Internet access (a few years later).
This. And before you knew it, you were the designated computer guy at your company. It happened to a lot of my friends.
Never let them know you can type. Even if you are the CEO, once the know you can type, you are no different than a pool secretary.
Not even remotely out of line for the era. My old boss started as a medicinal chemistry postdoc and became the IT sysadmin (well the entire IT department at the time) because he was running the biggest computers we had at the time, some old SGI boxes used for molecular modelling. He just retired as Director of IT for a sizable college.
Not at all. I was did IT in academic environments for 15 years and there was a lot of people who branched into IT because they had a shadow IT department and they started picking up skills (I hired a few of them). Sysadmin wasn’t as much of a profession then, so it’s easy to see how someone who spent years banging away on Sun or DEC systems would move there.
“Shadow IT”
I haven’t heard of that term before, but it makes sense, it certainly describes the work one of my brothers is doing writing software (as an accountant) that gets used by other departments including IT.
There is a brief documentary about tjis book too called KGB Computer and me. I love Clifford Stoll’s books. Even those that made predictions like “e-commerce will never work” like Silicon Snake Oil and High Herectic. Even failing in the predictions, the concerns it raises are still valid, maybe even more today.
Yeah, I started reading “Silicon Snake Oil” a few years after it came out. I didn’t finish it. He was right about some stuff, but it also seemed like it wasn’t going to work at all, and at the time I was reading it, some things were working.
Yeah. But he also said that Internet would be a source of misinformation and lies, thatcitvwoylscisolate people instead of bringing them together and would be sold as a way of direct participation in the government and a tool for education that would not materialize.
Sounds familiar? While people organized to bring every starving kid on the world the OLPC, children still died of hunger, but accessing the Internet.
One of the few that did not fell pray to this fake utopia was Stoll and Bill Gates that when visiting Africa to donate some PCs realized that this was an empty act and began to envision the Gates Foundation, bringing toilets to those people is far more fundamental but not as cool, but he did it anyway.
Look around on a mall or at a restaurant and you will see everyone looking down to their fakebook acounts forwarding fake news and memes and say Cliff was wrong.
In a way we have brought computers to the majority. We just call them smartphones. So much capability, so cheaply, in such a small size. So revolutionary that most futurist and science fiction didn’t even guess right.
Stoll referenced this in the book, IIRC (haven’t read it since around 1991-2). He said something to the effect that the astronomers all said “he’s not the best astronomer, but he’s magic with computers!”, and the IT guys all said “he’s not much with computers, but man, does he know astronomy!”
The KGB has been at this for a very long time.
The book (and the full video if I can find it) are on my list now!
Saw the documentary. I think this is the point where the KGB decided to bring those efforts internal. I also think there was an unsolved murder. Hathor would have known all the information that he sold. That would have been a liability for the KGB. At that point he was a loose end that had to be tied up.
And seriously, who sets themselves on fire?
YES! One of my favorite books. Always wished they would have a made a movie about it.
There is a PBS NOVA episode with most of the actual people involved playing themselves. “The KGB, the Computer, and Me” http://www.imdb.com/title/tt0308449/
I should obviously read the article before the comments.
There is actually a much better dramatization although copies are extremely rare called Spycatcher that was produced by Yorkshire Television in the UK as part of a series called Science Fiction. If you can find a copy it is definitely worth the effort expended.
http://www.worldcat.org/title/spycatcher/oclc/221635062&referer=brief_results
http://www.imdb.com/title/tt1385328/
I read this years ago and should read it again. One neat detail that stuck with me all these years was when he delayed an active hacker’s progress by jangling his keys over an exposed cable connector to introduce errors that slowed down communications. At least I think it was from this book.
You are correct, he was actually touching between the wires briefly with the keys.
Interesting. Why’d he do that instead of unplugging the cable? Had to keep some kind of connection going? I suppose I should just get the book and find out for myself. I’ll add it to my reading list!
He was inserting noise rather than dropping the connection.
That way he could slow them down and not let them know someone was onto them.
Read the book. :)
This is a yearly read for me. It’s such a good book.
Also, if you’re so inclined, here’s the Grateful Dead show he blew off the afternoon to go catch:
https://archive.org/details/gd86-06-21.sbd.brame.15406.sbeok.shnf
Whelp, there’s my soundtrack for the afternoon’s writing session. TFTL!
Only a yearly read?….
This is wild. I’m not even a Deadhead, but l’m listening to this as I reply.
Something about being able to slip back in time and hear the very concert referenced in the book, without moving my butt from my couch, is totally surreal. The massive preservation of data by folks we don’t like or trust is unnerving and threatening, but when it’s done by folks who tape shows and present their archive as a library, it’s pretty awesome.
This is indeed a fantastic book and a great read. I suggest reading the book first, and then watch the documentary film. I first read the book not long after it came out, and again several times since. It is a great story and would make an excellent screenplay if brought up to date here and there.
Somewhere there is a paper where he in detail recorded all *nix commands, social hacks, and red-tape cutting. I haven’t seen it in a while & I lost my copy. If anyone has this, please post for the edification of all.
Sorry, It’s in the article.
BTW, this book is what got me into computers.
My non-tech 70 yr old mother loved this book. She even had Cliff sign it during a book tour in Los Alamos. It’s a great read, I liked the key jiggling discussion.
This jogged a faint memory that he got into selling Klein bottles .. and sure enough … here’s a cool video that is super-worthy of Hackaday
https://techcrunch.com/2015/06/23/how-clifford-stoll-sells-klein-bottles-from-under-his-house/
I’ve got one of those bottles in my office.
Some of the more entertaining parts of the book came from sort of culture shock from going between California colleges and the government intelligence agencies. There’s a scene where Stoll has a few minutes alone in a CIA agent’s office. He borrows the agent’s “Top Secret” stamp and stamps a bunch of blank papers with it. The CIA guards are not amused.
Don’t’ forget microwaving the wet sneakers, then trying to mask it with vanilla extract in a frying pan…..
Funny you should mention that: https://hackaday.com/2015/06/24/crawlspace-warehouse-includes-midget-forklift/
There is a lot of information in German about the other side of the story:
– After Karl Koch, the hacker, burnt alive in a forest, his friends made a 68 page booklet about him that can be found at http://s23.org/wiki/Karl_Koch/Doku
– A movie was made in 1998, but it is not 100% accurate. F.ex. several of his friends were combined into one person. http://www.imdb.com/title/tt0126765
– When the movie was released, the media picked up the story. One video with interviews of his friends can be found at https://chaosradio.ccc.de/doc023.html
Cliff is one weird man. Anti-tech, but did all of this.
The Cuckoo’s Egg and The Hacker Crackdown, the two books that sum up the 80s and early 90s comp.sec scene.
I don’t think of him as anti-tech. He just had an early look behind the curtain and he found it (justifiably) frightening and decided to warn others. Of course no one listened, so see where we are today?
My question is, Does having all those Klein bottles in his basement warp the fabric of space-time in his local? Just curious.
+1 for ‘The Hacker Crackdown’, a classic book I re-read every 5 years or so.
First thing I though of upon seeing the title in my email was this https://en.wikipedia.org/wiki/Cuckoo%27s_Egg
I hope that Amazon allows downloads.
“Soul of a New Machine” is also an awesome book. Love the part about the flakies.
(humorous Stoll-CIA-Tom West link follows)
I have a hardbound copy of SoaNM. I was working at DG at the time, and knew many of the participants. My group later worked under West. He hated being asked to sign books, but his secretary had a signature stamp on her desk, and I got in to work early…my book has a red “J T West” signature on the title page :-)
Which probably makes the book more valuable because of the uniqueness of the “signature”.
B^)
I first read the book, when it became available as an ordinary hard copy. Read hard backed book. And a library one. Then we (dad and I) saw the Nova show on it. Suffice to say it is still an interesting book. And oddly enough most of the sites he notes that the pest found, were still active right around the beginning of the dial-up access to the Internet movement period. In fact that’s the book that got me interested in retrocomputing and the PDP-11 and VAX systems. Oh and the fun of confusing the people sent to operate booths for the IBM RT/PC designs, circa middle to late 1990s.
Picked this up a month ago for .99 cents at a used bookstore. Glad I did because it is a very good book.
His website’s pretty hilarious: “Yes, I am Cliff Stoll, and I make and sell Klein Bottles…”
http://www.kleinbottle.com/
Thanks for the link!
“Acme Klein Bottles – where yesterday’s future is here today!“
I remember what happened to Koch and his friends. It was quite a big discussion over here in the days. And it did raise good questions on what “hacking” is or should be considered.
I think Cliff described it best in the book when he described those guys as ‘Cyberpunks’… “hacking” is what this website is about.
A part of the book I especially like is when Stoll was facing his doctoral defense;
one of the panelists asked him, “Why is the sky blue?”
The book and the documentary complement each other. Had a chance to email Cliff many years ago. Interesting conversation.
I used this one for a research paper in 12th grade (1993). As part of my sources, I also used an email interview I did with Cliff (which my English teacher had no idea how to cite). I wish I still had it, but alas, time and tides…
One of the things I remember though, was asking him if he thought we’d ever see state-employed hackers…a question which he curiously answered in the negative. I recall his answer being along the lines of “it’s a nice thought for those in power, but in the end it would be impossible to control.”
Great book….
You should read? That doesn’t sound nice. “You might like these books” sounds a bit better.
Read this book too, numerous times, exciting and suspense, wow, a must read if you’re into this genre :)
Thank you for this post! I finished reading the book over the weekend, and it was great.
Just ordered both the Cuckoo’s Egg and the Hacker Crackdown. Can’t wait to read both.